An Introduction to RSA Netwitness Investigator
In many cases using Wireshark to do a network forensics is a very difficult task especially if you need to extract files from a pcap file.
Using tools such as RSA Netwitness Investigator can make network forensics much easier. RSA Netwitness Investigator is available as freeware.
Installation:
1-Go to http://www.emc.com/security/security-analytics/security-analytics.htm#!freeware to obtain the latest version of RSA Netwitness Investigator.
2-Launch NwInvestigatorSetup.exe
3- Read the license agreement and accept it (if you wish).
4- Choose users
5-Choose the Install location and click install.
Once you finished your installation you have to register freeware user account. You have to activate your version before you can use it.
Usage:
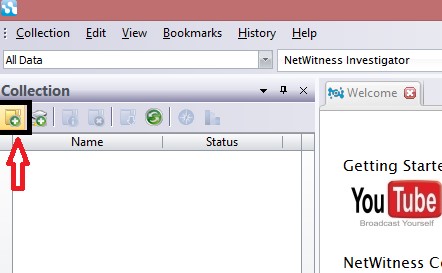
1-Create New local collection
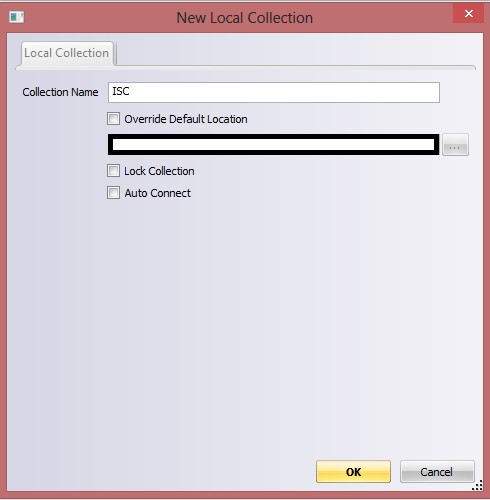
2-Enter the new collection name:
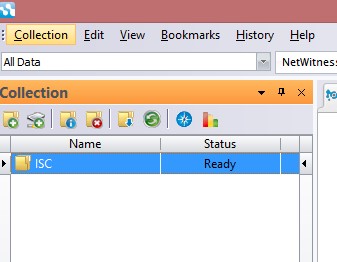
3-Select the collection
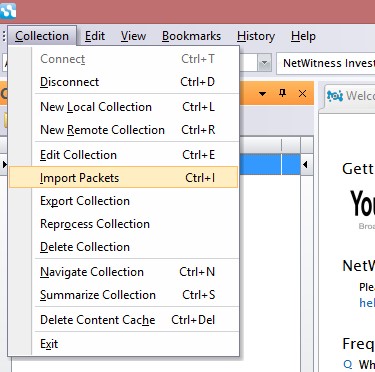
4-Select Import Packets from Collection menu and select the pcap file that you would like to investigate
5-Select Navigate Collection From Collection Menu
6-Now you should have something similar to this screen :
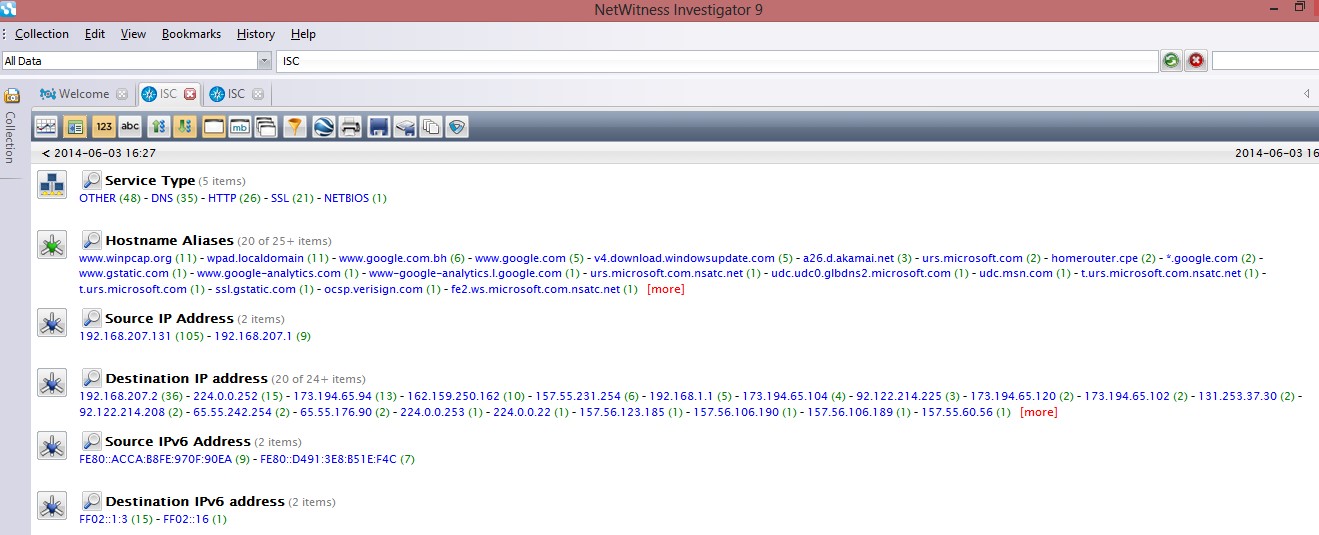
As you can see everything is clear and can browse it by Service Type (protocol) ,hostname ,source IP �?�.. etc.
Let say for example you want to explore the name of the exe files that contained in the pcap file you do that by clicking on extension->exe and you will see all the exe files in the pcap file and you will see all the details of the file such as where it�??s come from (IP Address and hostname ) and how it�??s come (protocol) .
.jpg)


Comments