AppLocker Event Logs with OSSEC 2.8
In a previous post, Monitoring Windows Networks Using Syslog, I discussed using syslog to send the event logs to a SIEM. This post covers another technique for collecting event log data for analysis.
A new version of OSSEC (2.8) has been released that includes the ability on Windows to access event channels that were introduced in Vista. To get this to work correctly, I had to have the agent and server on 2.8. This new ability allows admins to send some of the more interesting event logs to OSSEC in a very easy way.
Client Config
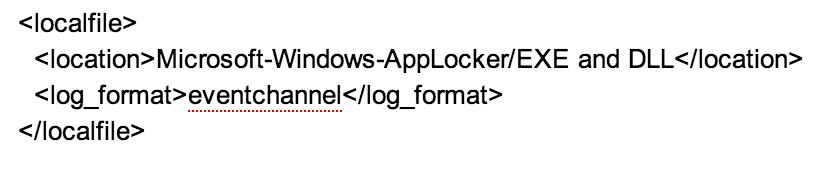
Setting up the config for the subscription is quite easy. If you want to do it on an per install basis, you edit the C:\Program Files\ossec-agent\ossec.conf. Add a new tag for local file, then under location put the XPATH channel name and the log_format as eventchannel.
�??
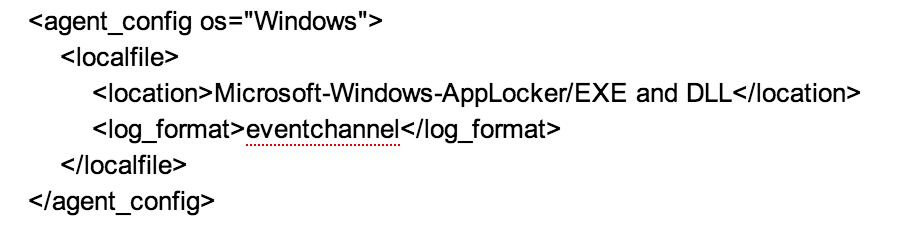
If you want this config to be pushed out to all your Windows OS centrally, you should add the config below to the /var/ossec/etc/shared/agent.conf. This file has a added XML field for matching which system should apply the config.
Creating Rules
Once you get the logs, you need to create rules to get the alerts. When creating the rules, you need to know what event level (e.g. Info, Error ect..) the alerts are created for the event. To get a detailed list of the events, follow this link (hxxp://technet.microsoft.com/en-us/library/ee844150(v=ws.10).aspx)
When creating your own rules, you should always add them to the Local_rules.xml file to make sure they do not get overwritten with updates. These rules should start with 100000 rule ID.
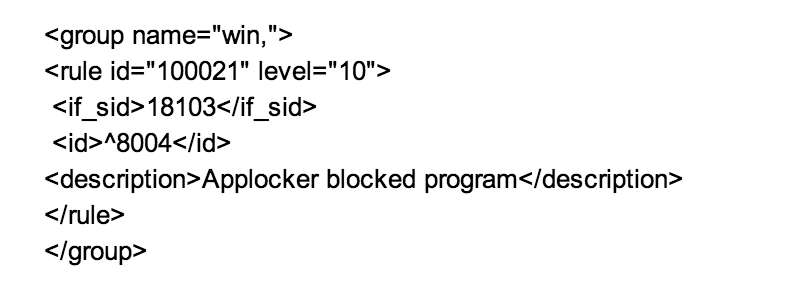
I�??ve posted all my AppLocker rules to my github(hxxps://github.com/tcw3bb/ISC_Posts/blob/master/OSSEC_AppLocker_Local_Rule.xml), and I�??ve also submitted them to the OSSEC group to be added in the next version. When using the local rules, you may need to change rule ID for your environment.
RAW Log
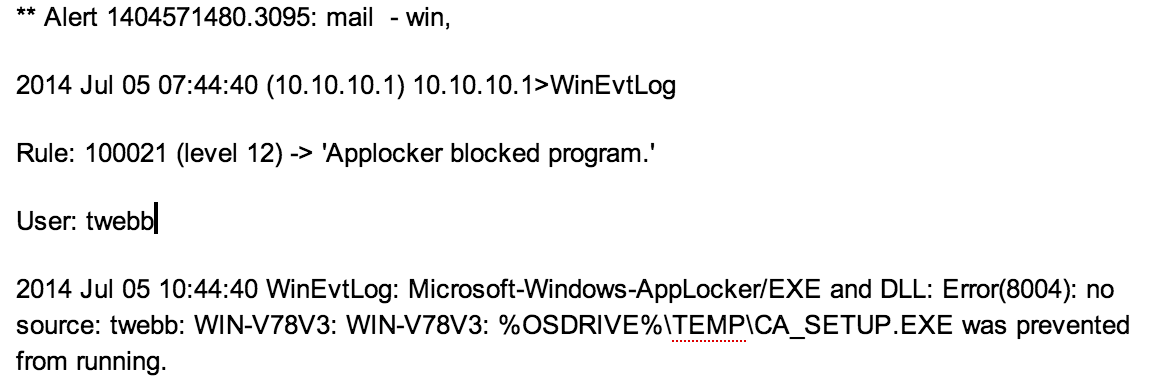
Once you have the rules in place your alerts like the ones below should be created.
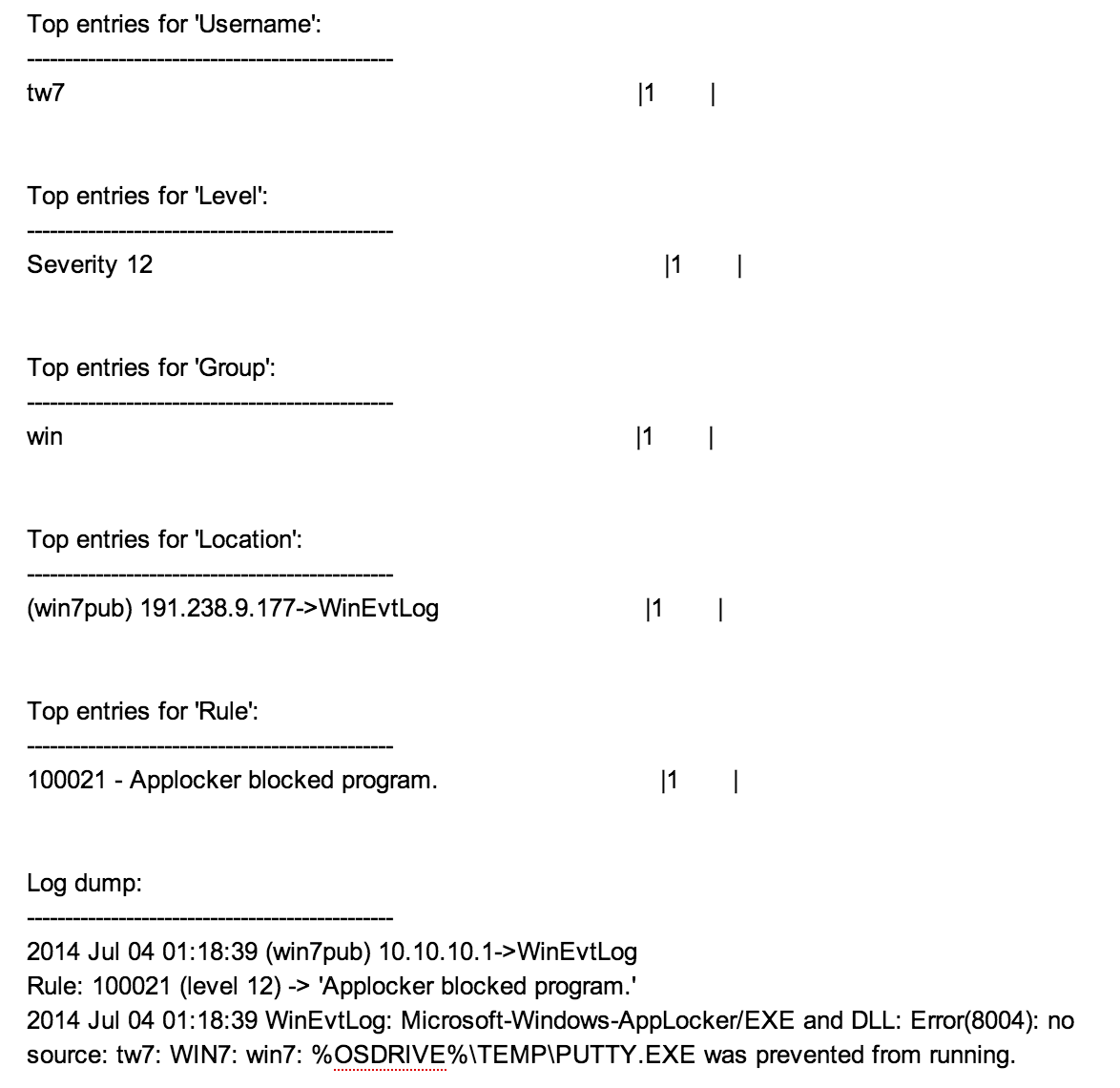
Quick report
To get a report for the current day of who had blocked apps, you can run the following:
>zcat /var/ossec/log/alerts/alerts.log |/var/ossec/bin/ossec-reportd -f rule 100021 -s
I also have a nxlog and an eventsys client config on my github (hxxps://github.com/tcw3bb/ISC_Posts)for additional client config. To use these with OSSEC, you will need to have a different parser and rules.
--
Tom Webb


Comments