Mixed Messages : Novel Phishing Attempts Trying to Steal Your E-mail Password Goes Wrong
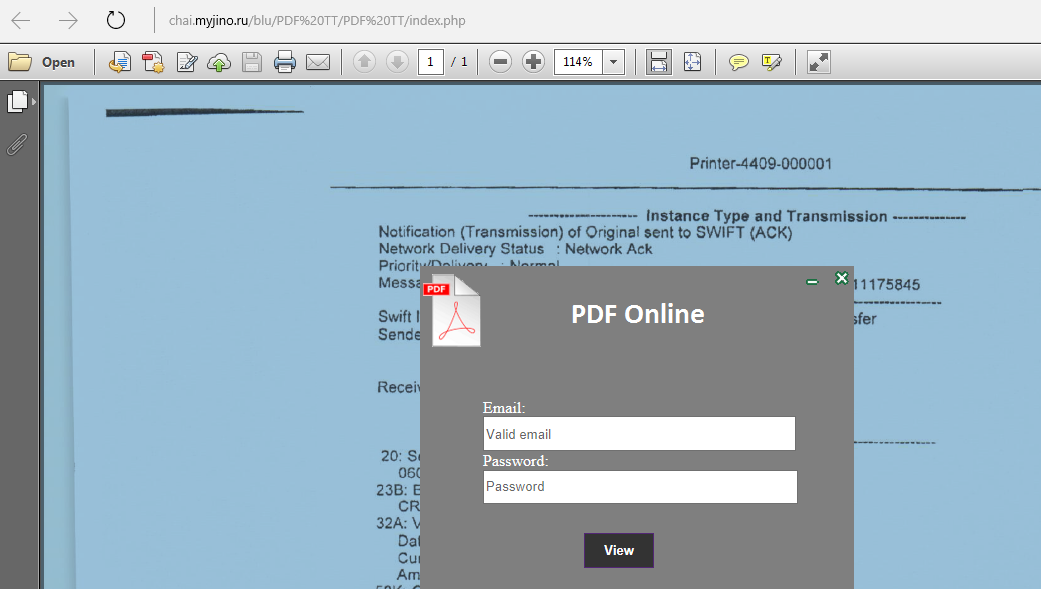
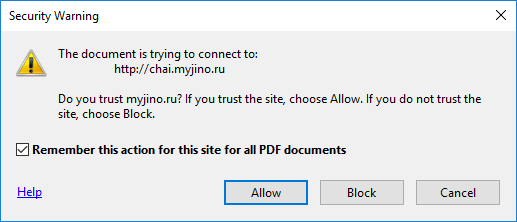
A writer wrote in to send us an interesting phishing attempt they had received at their organization. An email from a school domain that purported to be VetMeds send an "encrypted" PDF that required a user-name and password to log in to. The subject of the email was "Assessment document". The PDF itself was created with Microsoft Word and included a link that suggested it was a locked document and you needed to click a link to unlock it which pointed to chai[.]myjino[.]ru and gave a screen with a purported PDF behind it and a login box that it happily accepts. Below are some screenshots, but some notes. Updated versions of Acrobat should ask before going off to bad websites. What I found interesting was the lure was a VetMeds assessment but the underlying document at the Russian website is for a SWIFT transaction, so some mixes messages there.
Some advice, be wary of emails from domains that don't match the contents, note that encrypted PDF documents are not locked this way (and will never ask you for your actual email password anyway), and look for other inconsistencies that give these away as scams. Make sure users are aware of the little tell-tale signs below so they can stop themselves before becoming victims.
--
John Bambenek
bambenek \at\ gmail /dot/ com
Fidelis Cybersecurity


Comments