Analyzing MSG files
I was asked how to analyze .msg files, e.g. emails saved with Outlook. It's something that I have to do regularly, when readers submit emails for analysis.
We talked about msg files before: they are "Compound File Binary Format", and can thus be analyzed with tools like oledump.py.
A .msg file will contain a large amount of streams (easily more than 100), and their names contain hexadecimal digits to indicate their type and purpose.
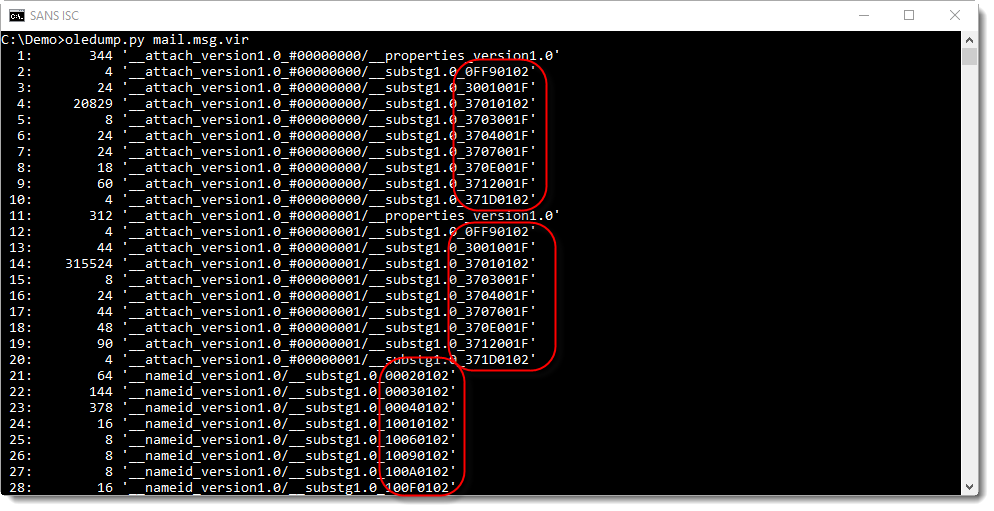
To help me identify streams (like streams with the content of attachments), I have an oledump plugin: plugin_msg.
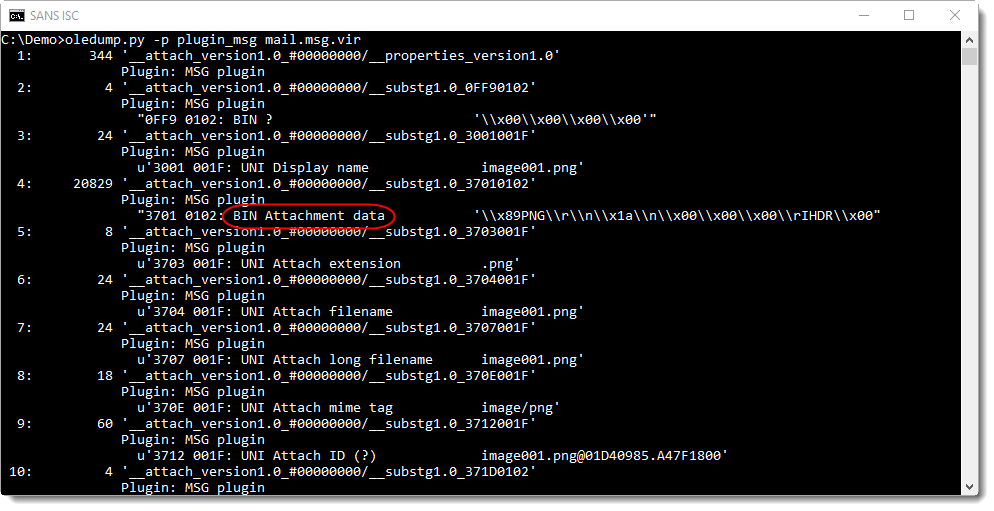
In this screenshot, we can see that the content of stream 4 is binary data (BIN) and that it contains the attachment (Attachment data). The dump of the header on the same line tells us this is a PNG file. Which is confirmed by the attachment name in stream 7 (UNI = UNICODE): image001.png.
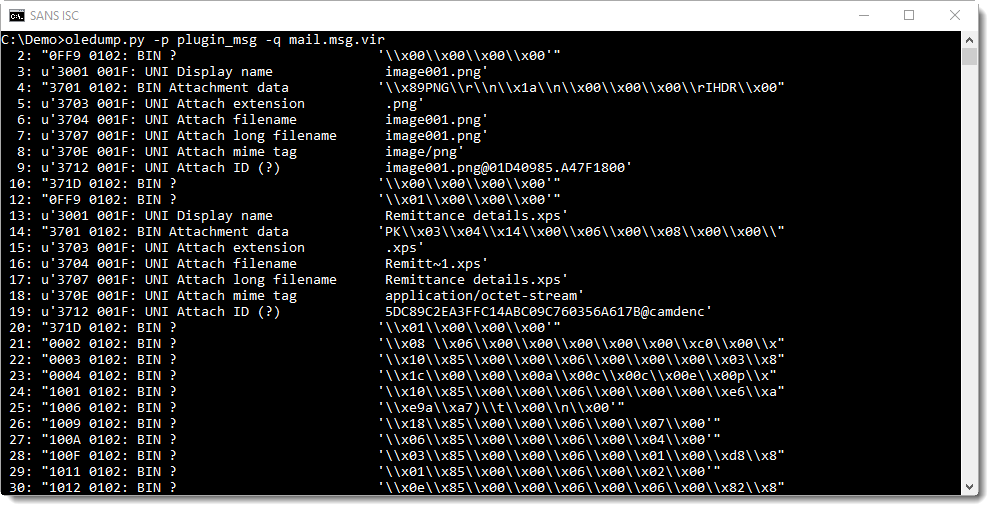
Option -q can be used to limit oledump's output to the plugin, and thus have a more compact overview:
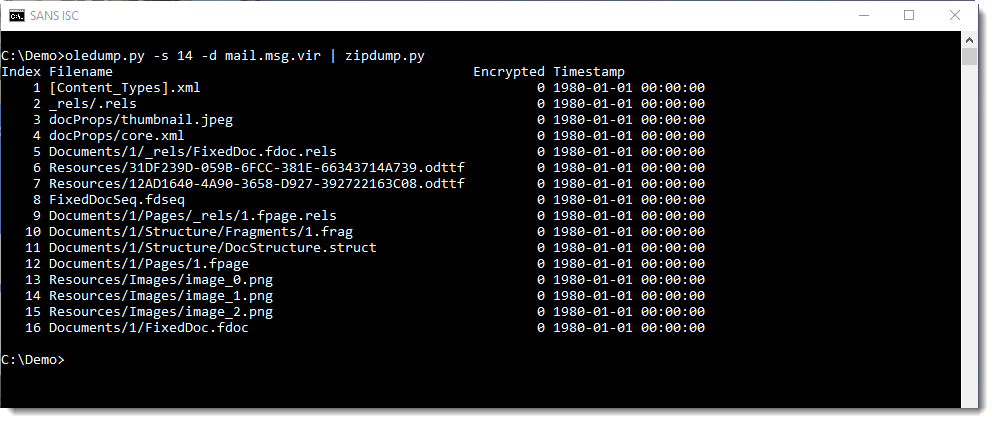
To analyze attachments, we just have to select and dump them:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments