New Extortion Tricks: Now Including Your (Partial) Phone Number!
Barely a month after we saw extertion emails appearing with leaked passwords (New Extortion Tricks: Now Including Your Password!), we are now seeing extortion emails with partial phone numbers.
Like this example submitted by a reader:
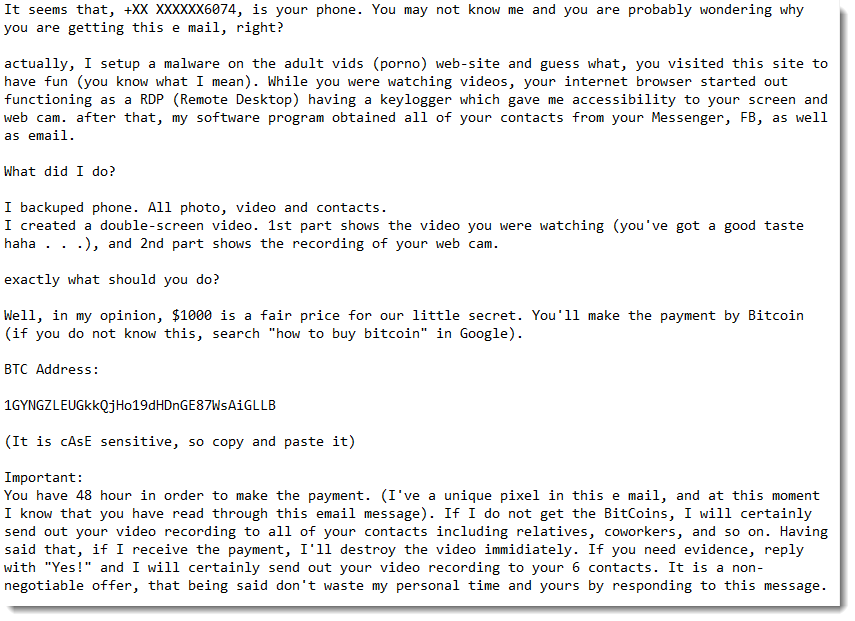
For a couple of emails, we were able to verify that the digits of the partial phone number match the actual phone number of the owner of the destination email address.
We don't know yet what source is used by the extortionists that provides email addresses with partial phone numbers, but I think it is unlikely to be a data breach (like with the password extortion emails).
A classic data breach with phone numbers would contain full phone numbers, and I don't see why the extortionists would mask most of the digits.
They must have another source, and that's where we ask for your help: what ideas or remarks do you have?
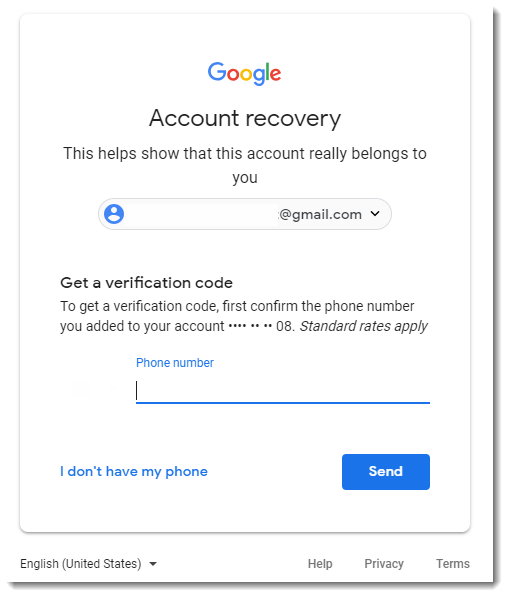
We came up with possible sources like whois data or password reset mechanisms, like Gmail:
Please post a comment with your idea, and if you received a similar email, please consider submitting it.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments