Simple Phishing Through formcrafts.com
For a long time, moving services to the cloud has been a major trend. Many organizations jumped into the cloud because it’s much easier and cost less money (in terms of maintenance, licence, electricity, etc). If so, why should bad guys not follow the same trend? Last year, I wrote a diary about a phishing campaign that used jotform.com[1] to handle the HTTP POST data. Yesterday, I found a new one fully hosted by a cloud service. It was accessed through a bit.ly shortened URL in a mail:
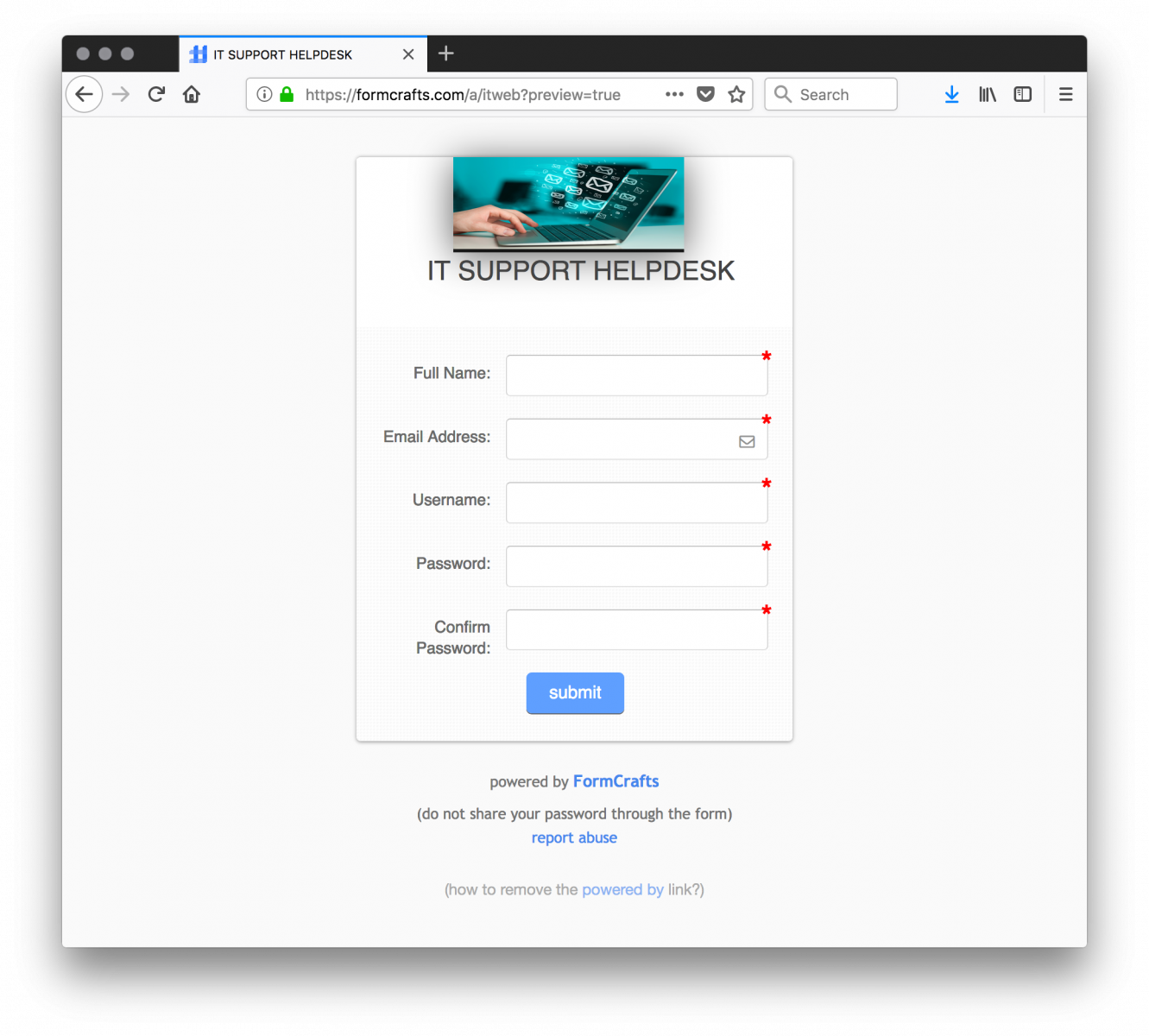
formcrafts.com is a service which offers powerful online forms. They have a free plan which allows 3 forms / 15 fields / 50 submissions per month. This can be more than enough for a phishing campaign, especially if you create multiple accounts. Once registered, you can design your forms and manage them via a nice dashboard:
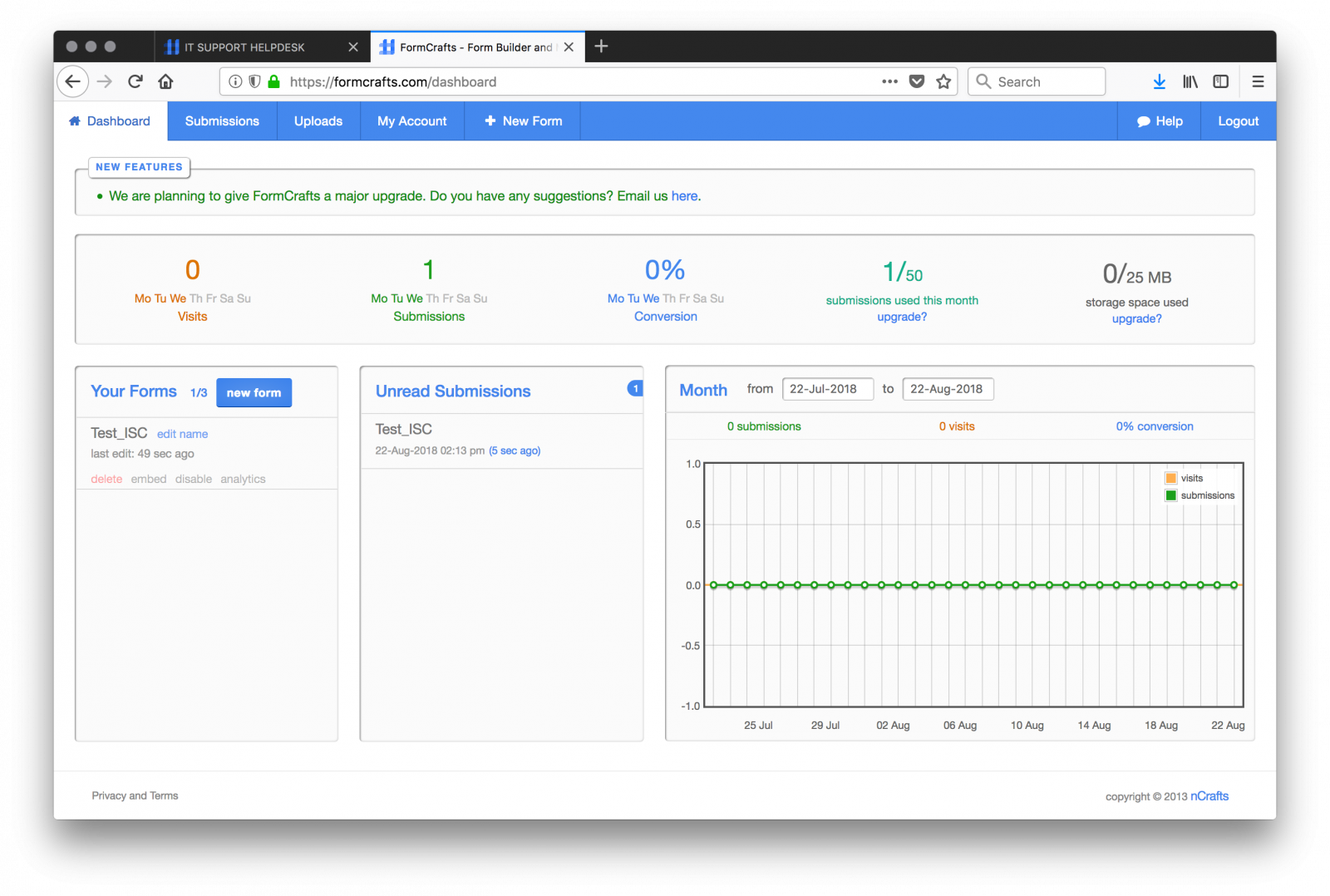
Not surprisingly, I found more than one malicious forms:
hxxps://formcrafts[.]com/a/itsupport
hxxps://formcrafts[.]com/a/itweb
hxxps://formcrafts[.]com/a/webit
hxxps://formcrafts[.]com/a/ithelpdesk
Using such services is interesting from an attacker point of view because they don’t need to compromize other resources to host their phishing pages and cloud services are usually allowed through proxies/access-lists.
[1] https://isc.sans.edu/forums/diary/Phishing+Kit+AbUsing+Cloud+Services/23089
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments