Packet Editor and Builder by Colasoft
I was looking for a tool to modify the packets in a pcap file for testing purposes that would allow me to change and modify any fields in packets and recompile the checksum to be able to use them for testing and training. I wanted to be able to change and modify some of the content such as IP addresses and where necessary, modify the content of the payload to obfuscate sensitive information. This Packet Editor and Builder by Colasoft is advertise as a freeware tool and very useful to manipulate and send packets over a network interface.
The interface is easy to use and intuitive. It is divided into three sections: Decode Editor that present the packet headers, the Hex Editor that shows the packet in hexadecimal format and the Packet List that shows individual packets.
The Decode Editor section can manipulate each part of the packet header, simply select and change the information to what you need. As you modify the information in the header or the payload, the checksum is recalculated (box on top of graph) to ensure the packet is free of checksum errors.
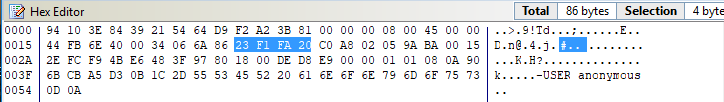
In the Hex Editor section, you can manipulate the payload of the packet by removing, modifying or adding to the payload. This picture is the original packet with USER anonymous:
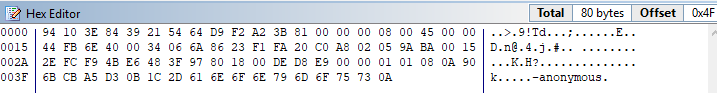
This second picture is after removing USER from the payload:
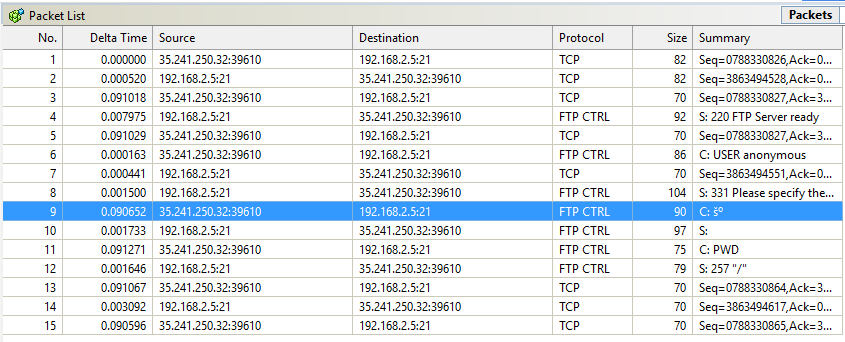
Last is the Packet List section. This section shows the list of the packets which also includes the protocol and a summary of what the payload contains (if available).
Also a nice feature that is built-in this tool, it allow for building your own packets from scratch or reuse a pcap file and sending them via one of the host adaptors.
[1] https://www.colasoft.com/download/products/download_packet_builder.php
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu
.PNG)
.PNG)


Comments