Keeping an Eye on Malicious Files Life Time
We know that today's malware campaigns are based on fresh files. Each piece of malware has a unique hash and it makes the detection based on lists of hashes not very useful these days. But can we spot some malicious files coming on stage regularly or, suddenly, just popping up from nowhere?
I'm using VirusTotal to hunt for malicious files based on a bunch of YARA rules and, via the VT API, everything is indexed into a Splunk instance. Here is a sample of detected malicious file:
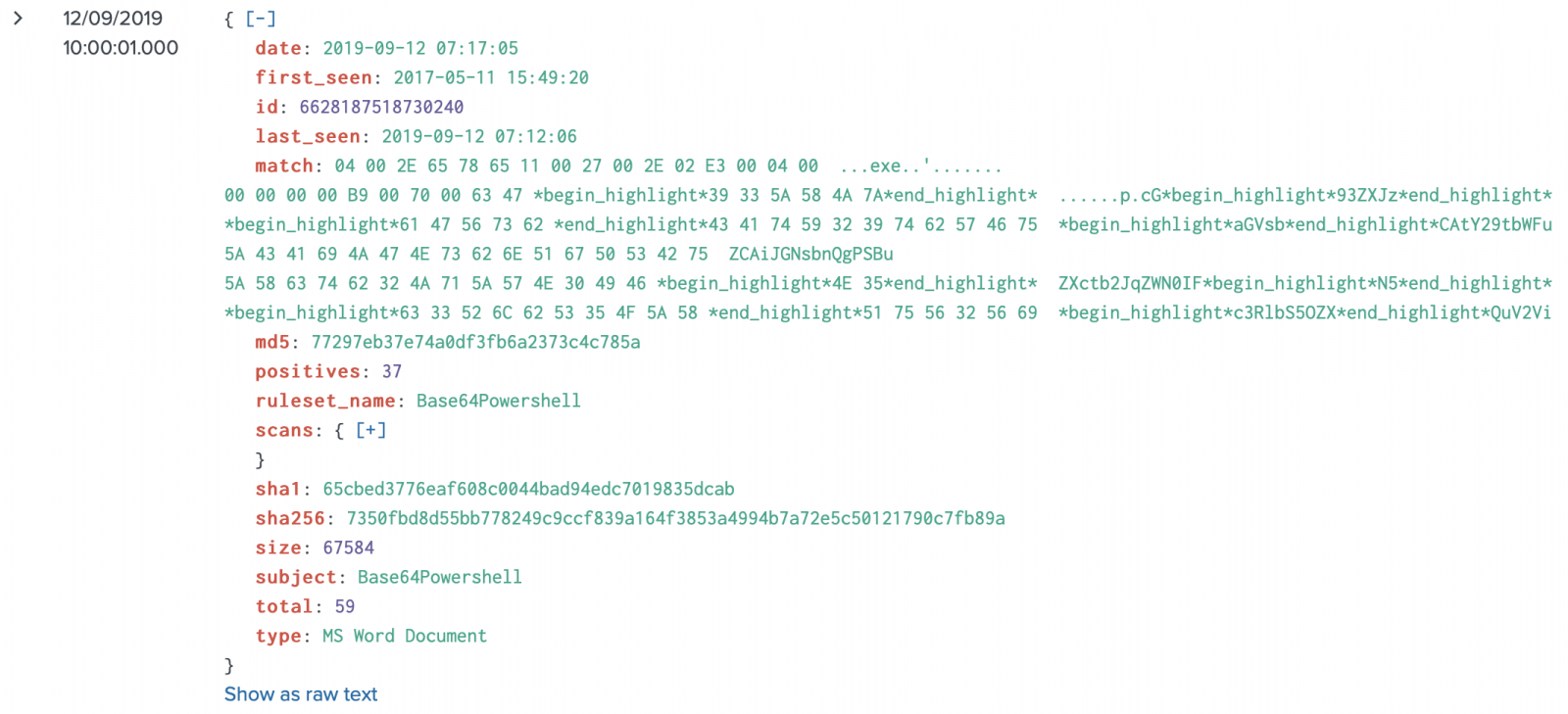
You can see two interesting fields (well, all of them are interesting):
- first_seen
- last_seen
It could be interesting to have a look at the "age" of a file from a VT point of view. By computing the time difference between the two timestamps, we could see if a file is in the wild for a while or a brand new one...
Here is the base query that I performed:
index=virustotal sourcetype=_json | spath first_seen | spath last_seen | spath sha256 | spath type | spath positives | dedup sha256 | eval i = strptime(first_seen, "%Y-%m-%d %H:%M:%S") | eval o = strptime(last_seen, "%Y-%m-%d %H:%M:%S") | eval age = tostring((o - i), "duration") | search positives > 5 | sort - age | table sha256,type,positives,first_seen,last_seen, age
I'm searching only for files detected as malicious (score > 5) from 2019/01/01 until today (16 months). Here are some findings:
- 8042 files have matched my YARA rules
- The oldest file is 1b441fde04d361a6fd7fbd83e969014622453c263107ce2bed87ad0bff7cf13f[1]. It's the famous 'Invoke-Mimikatz.ps1'. It was first uploaded to VT on 2015-11-05 15:27:45. The last submission was on 2019-04-04 10:40:30.
- 7698 files were uploaded only one time (age = 0) (95%)
Here is the split of file types for malicious files that have been uploaded more than one time (age > 0):
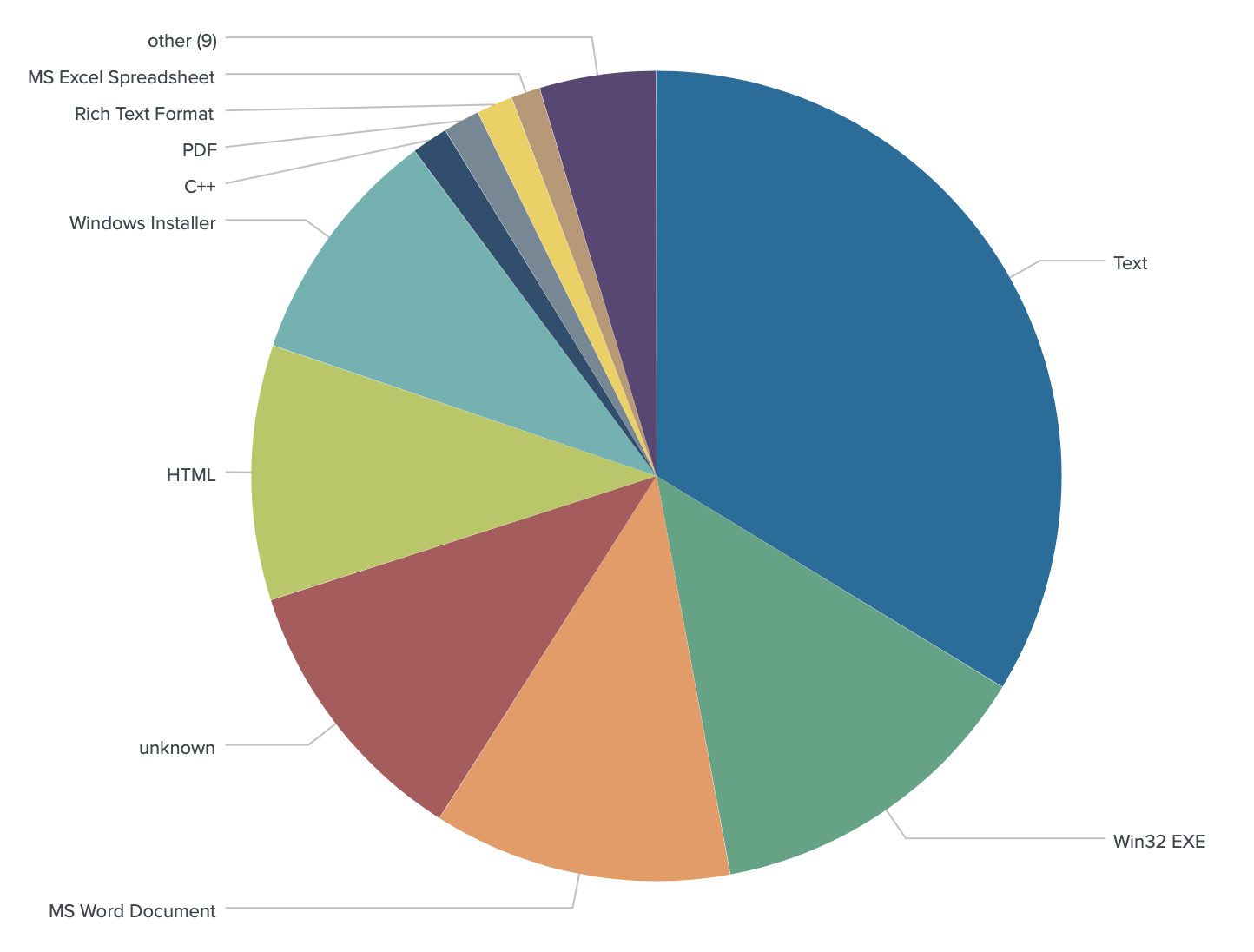
The file type 'Text' means all kinds of scripting languages (mainly PowerShell). Note that the number of malicious Word documents is interesting! (3rd position).
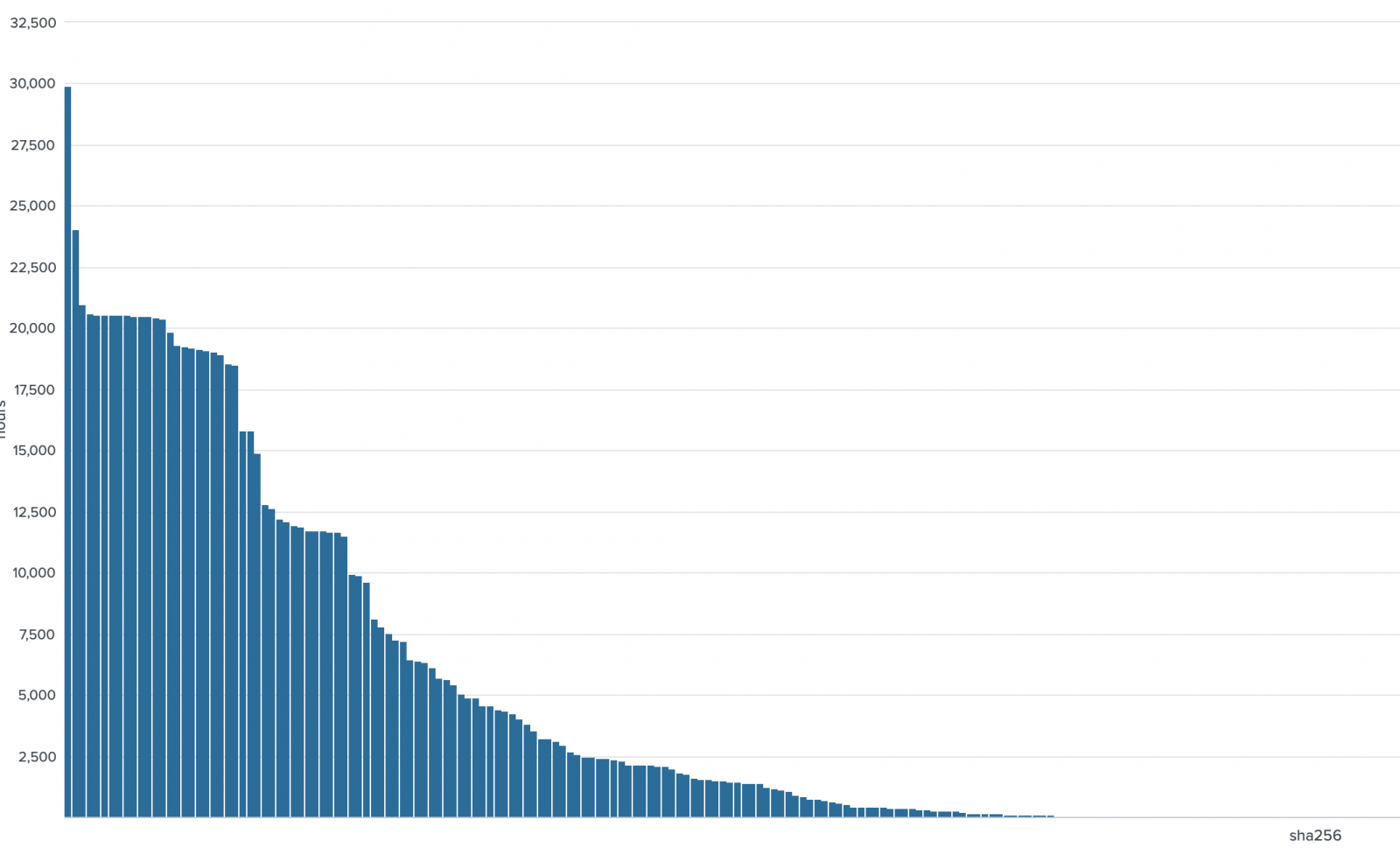
Here is the overview of ages (in hours):
At the opposite, we can also spot malware campaigns just released on the wild (ex: new waves of phishing) because the age remains very low. Many samples have an age of approximatively one hour:
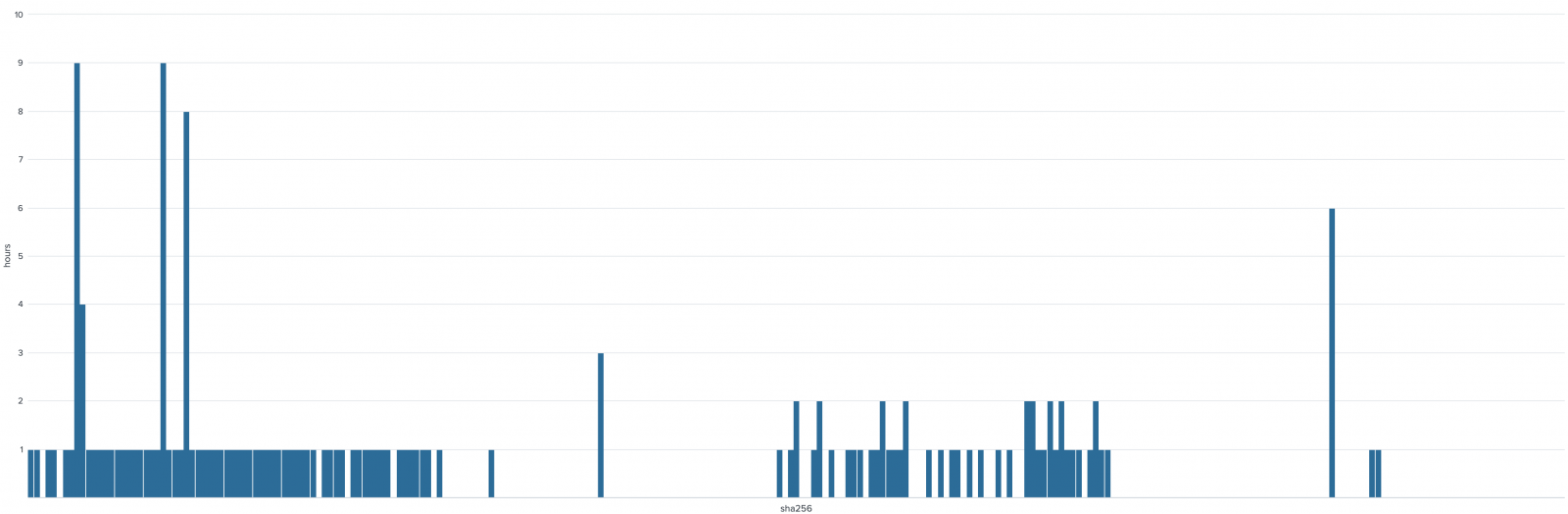
As you can see, most of the samples uploaded to VT are "fresh meat" (new hash) but many of them are coming back regularly... Reasons can be multiple: security researchers resubmitting files, red-teams testing if the score of old samples, old emails reopened with attachments?
Stay safe!
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments