Cracking Maldoc VBA Project Passwords
In diary entry "VBA Project Passwords" I explained that VBA project passwords in malicious documents don't hinder analysis: you can just extract the macros without knowing the password. It's only when you would perform a dynamic analysis with the step-by-step debugger of the VBA IDE, that the password would prevent you from doing this. But there are simple methods to remove the password, and then you can go ahead with your debugging.
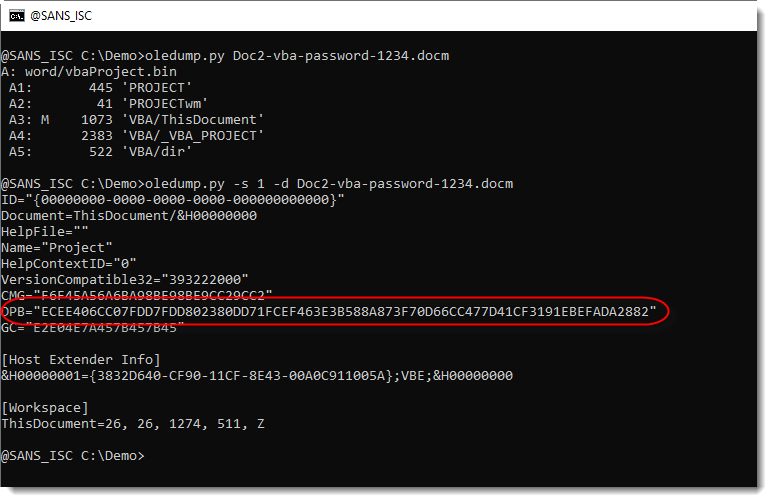
I did some further research, and did not find a free, open-source VBA password cracker. The VBA project password is hashed with a salt (sha1(MBCS(password)+salt)), then encoded with a custom, reversible XOR-encoding and then stored as an hexadecimal value of parameter DPB in the PROJECT stream.
If you want more details, I have a post on my personal blog: Cracking VBA Project Passwords.
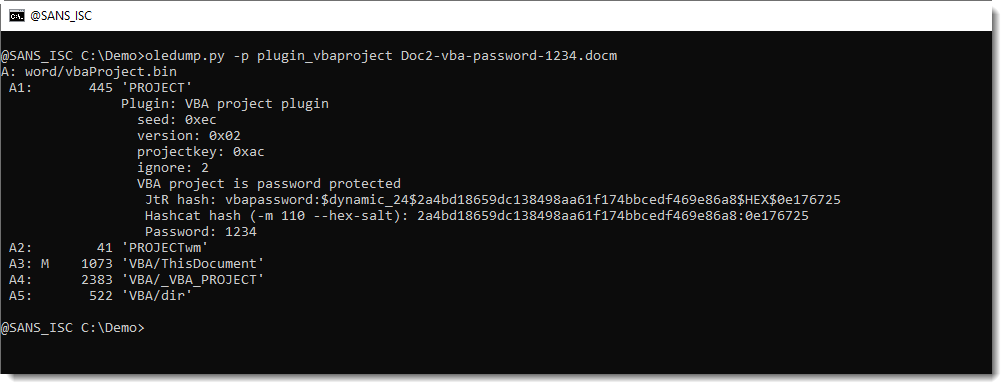
And I also developed an oledump plugin to extract the hash and represent it in the formats compatible with John the Ripper and Hashcat. This plugin also performs a small dictionary attack (using John the Ripper's public domain wordlist), and displays the password if it can crack it:
Finally, I also show the different steps in this video:
VBA project passwords used by actors might become useful threat intel, but that is another research project.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments