BASE85 Decoding With base64dump.py
Xavier's diary entry "Multiple BaseXX Obfuscations" covers a malicious script that is encoded with different "base" encodings. Xavier starts with my tool base64dump.py, but he can not do the full decoding with base64dump, as it does not support BASE85.
I've now added support for BASE85: base64dump.py version 0.0.0.16.
(you can watch this video: "Adding BASE85 To basedump64.py", if you are interested to know what changes I made to my base64dump.py tool to support BASE85)
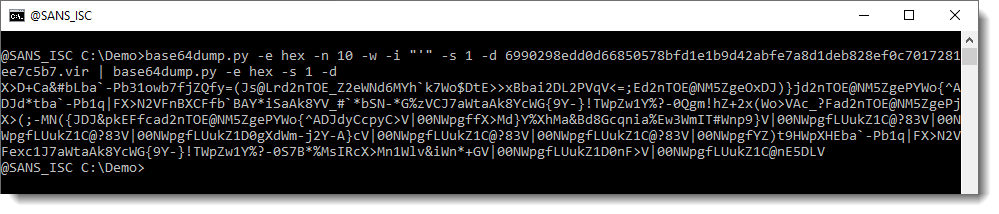
So, let's see how to use base64dump with Xavier's sample. As Xavier showed yesterday, this sample has the payload encoded as a list of hexadecimal string. So let's do hex decoding with base64dump: option -e hex. And option -n 10 for a minimum length of 10:
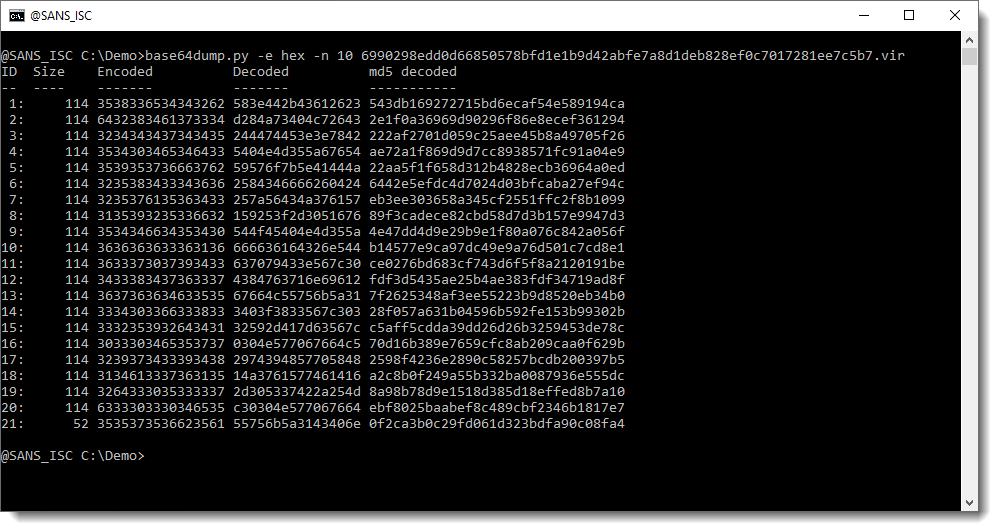
base64dump found 21 hexadecimal strings, with a minimal decoded length of 10.
These strings have to be concatenated together. We can achieve this with base64dump, by ignoring all whitespace (including newlines) and ignoring the string quotes (single quote '), like this:
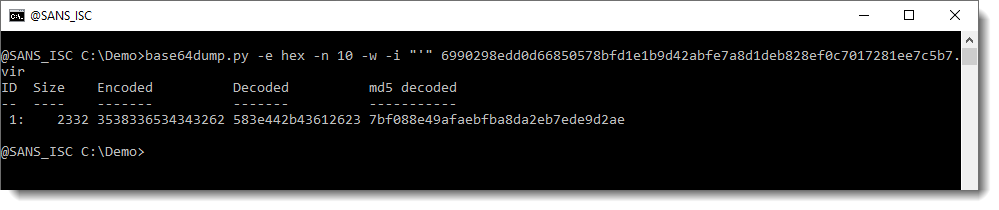
Now we have extracted one single, long hexadecimal string. Let's selected and decode it:
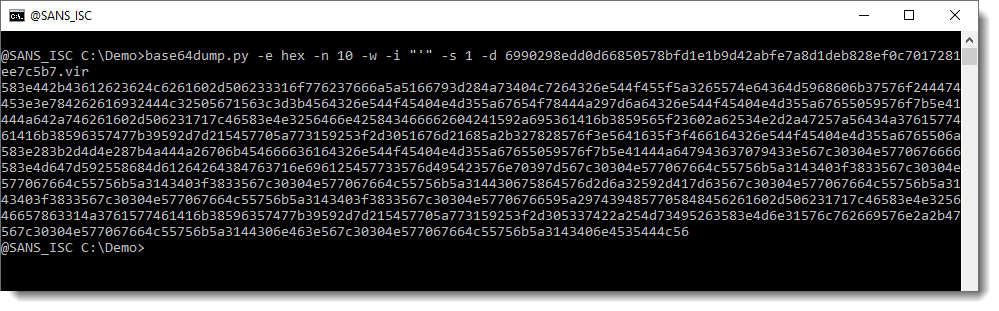
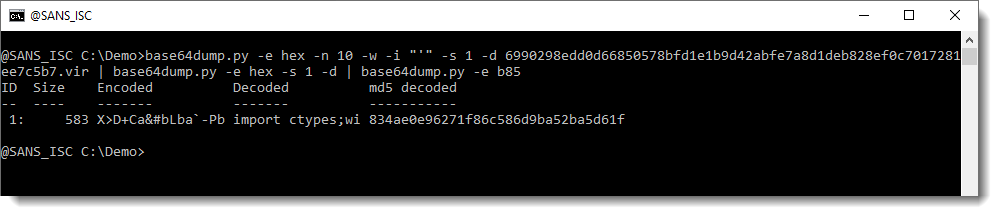
This is again an hexadecimal string. Let's decode it with another instance of base64dump:
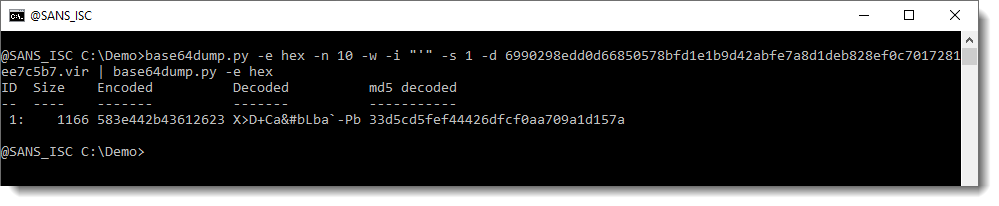
And this is the BASE85 encoded script. Let's decode that too:
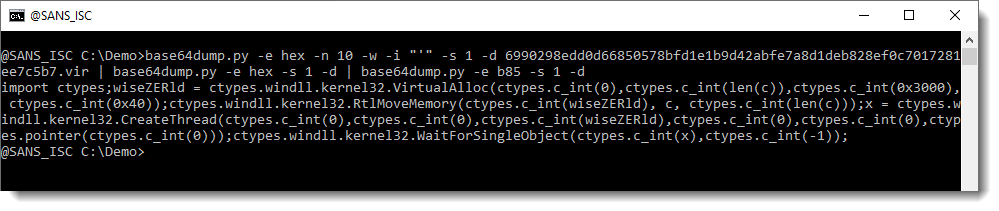
And we end up with the same decoded script as Xavier found yesterday.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com



Comments