An Analysis of a Discerning Phishing Website
Cybercriminals and adversaries have long used phishing websites to obtain credentials and access systems they usually would not have access to. Indeed, it could be more cost-effective than other methods, such as buying zero-day vulnerabilities and weaponizing them. I was alerted to a phishing attempt and requested further details. After doing some analysis, I observed several differences and technological improvements that the adversaries had made as compared to the usual phishing attempts.
Figure 1 below shows the vector of the phishing message. It arrived via Short Messaging Service (SMS) and informed the victim that their bank account had been suspended due to a tax investigation by the Singapore tax agency Inland Revenue Authority of Singapore (IRAS). It further requested the victim to tap on a link and presumably enter their credentials so the bank could restore access. It was also observed that the adversary likely performed SMS Sender ID Spoofing to make the SMS arrive within the thread of legitimate SMS messages (specific details have been redacted to provide privacy to the reporter and parties affected).
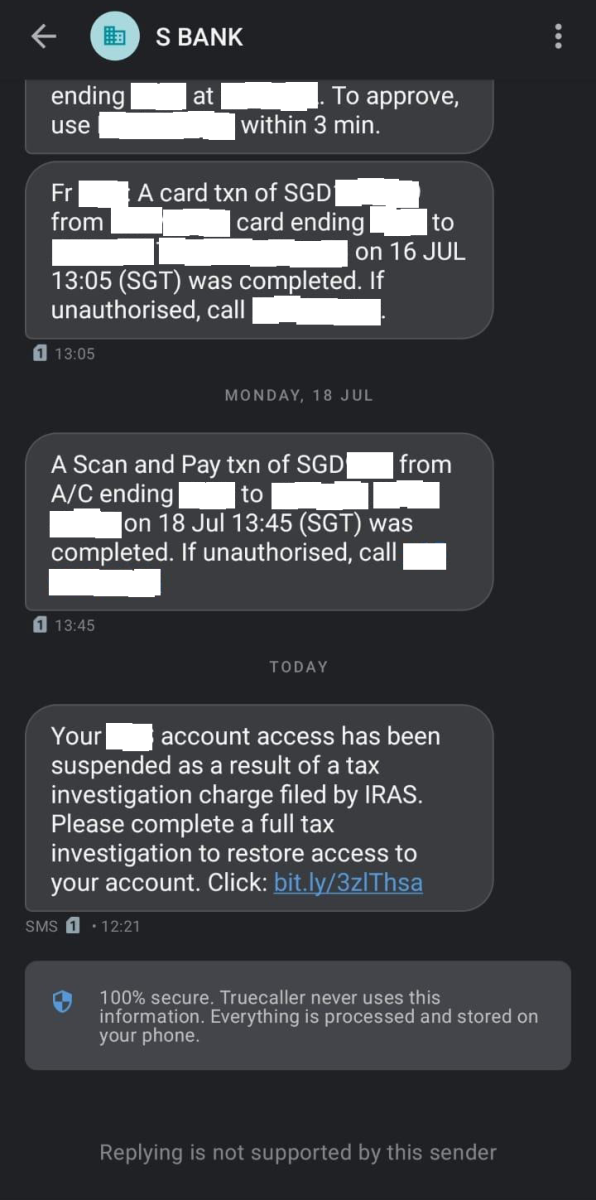
Figure 1: Phishing SMS Purporting the Suspension of Victim's Bank Account
Tapping on the shortened link revealed the link of hxxps://wwwirasgov-sgloginesvweb.sbs/url. However, this is where things started to be very different. I have listed the different scenarios in the list as follows:
Scenario #1: Victim clicks on the link but is on a desktop.
If one clicked on the link via a desktop browser, the website would redirect the victim's HTTP Request with an HTTP 302 Found Response and redirect them to the legitimate IRAS website and leave it as it is.
Scenario #2: Victim/Defenders attempt to do some checks via web reputation sites
With the advent of cybersecurity awareness training (be it in employment or via governmental efforts), many potential victims could check the legitimacy of a link via online web link checkers or web reputation tools before they fully interact with any new sites. This behavior is excellent, but the adversary used Cloudflare's access restriction features to prevent the discovery and exposure of their phishing websites to savvy victims and potential blue teams (with reference to Figure 2 below). With these tools blocked, victims/blue teams would be unable to check on this website's legitimacy and forced to interact directly with the website. This also extends the longevity of the phishing site since it is less likely to be accessed and discovered by the Blue Team.
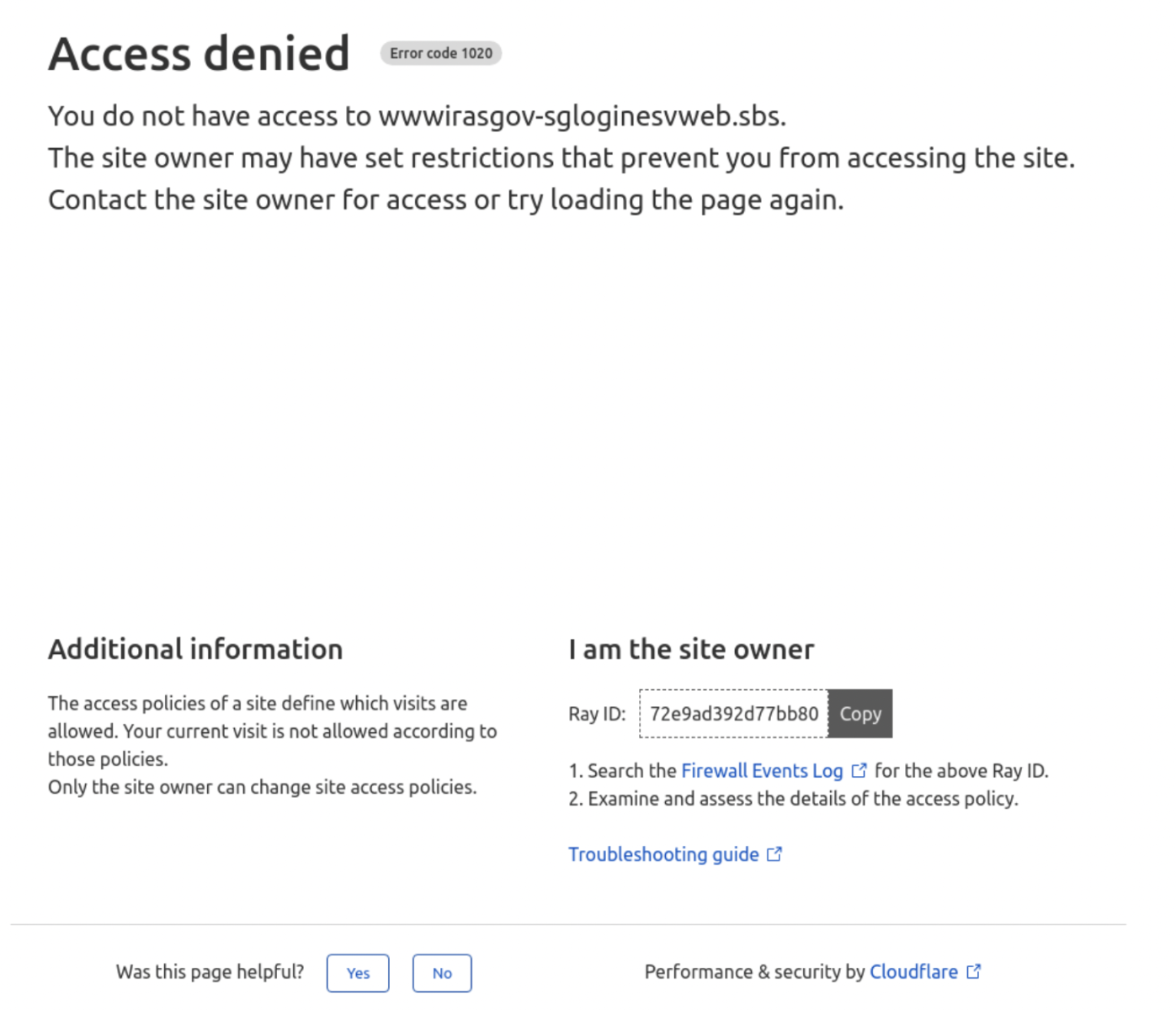
Figure 2: Cloudflare Blocking Reputational Checks Based on Configured Access Policies by Adversary
Scenario #3: Unsuspecting victim accesses link via mobile phone browser
If the victim clicks on the link on a mobile phone, they will be greeted with a webpage, as shown in Figure 3 below. Singapore Personal Access (Singpass) is a digital identity service that is used to access government and private services (such as banking) in Singapore.
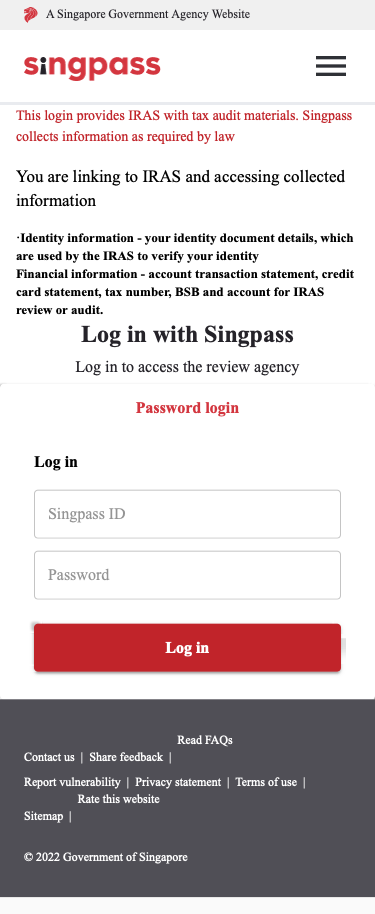
Figure 3: Phishing Website as shown on a Mobile Device
The website even checks whether you are giving false inputs (with reference to Figures 4 and 5).
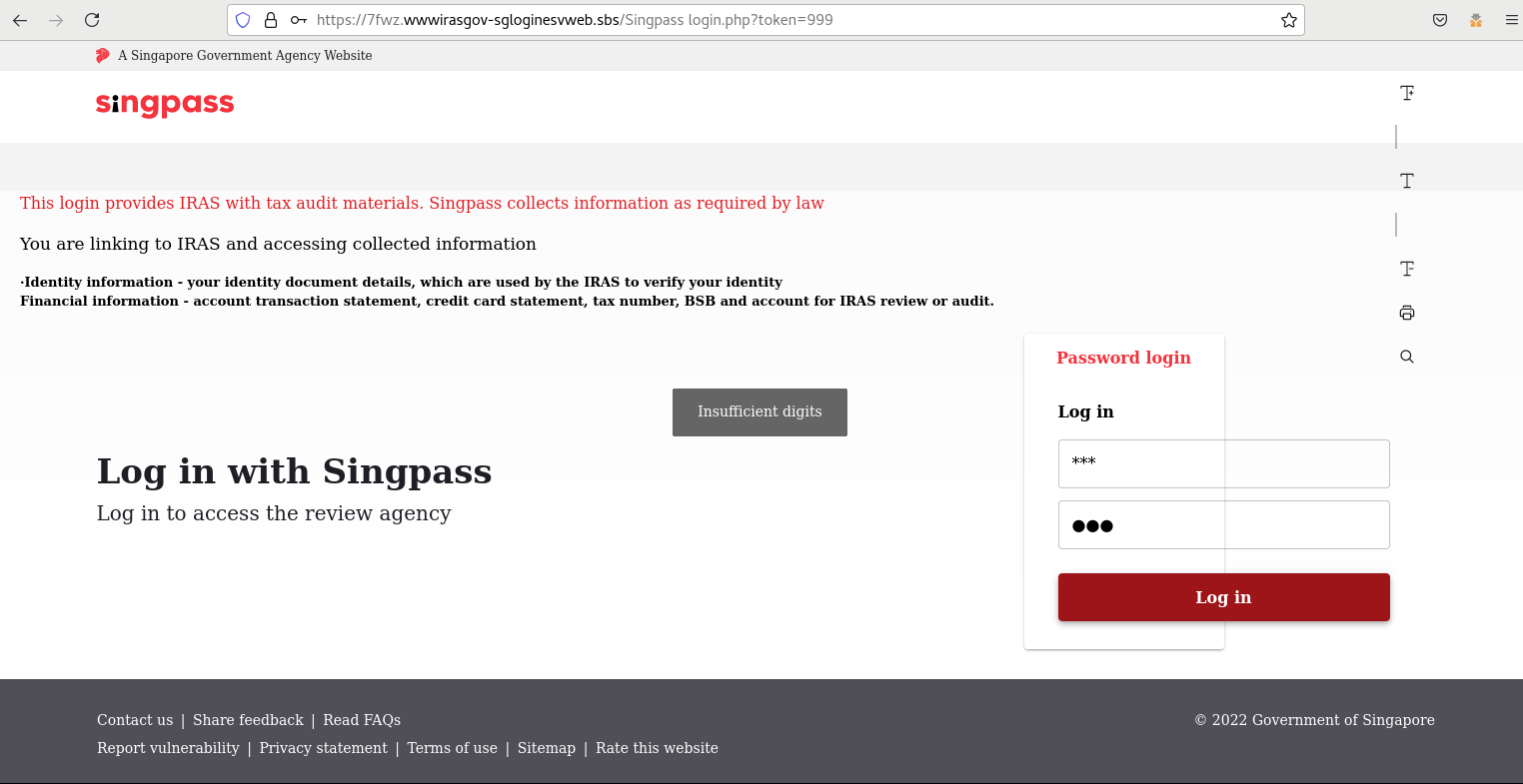
Figure 4: Client-Side Input Validation Checks on Phishing Website
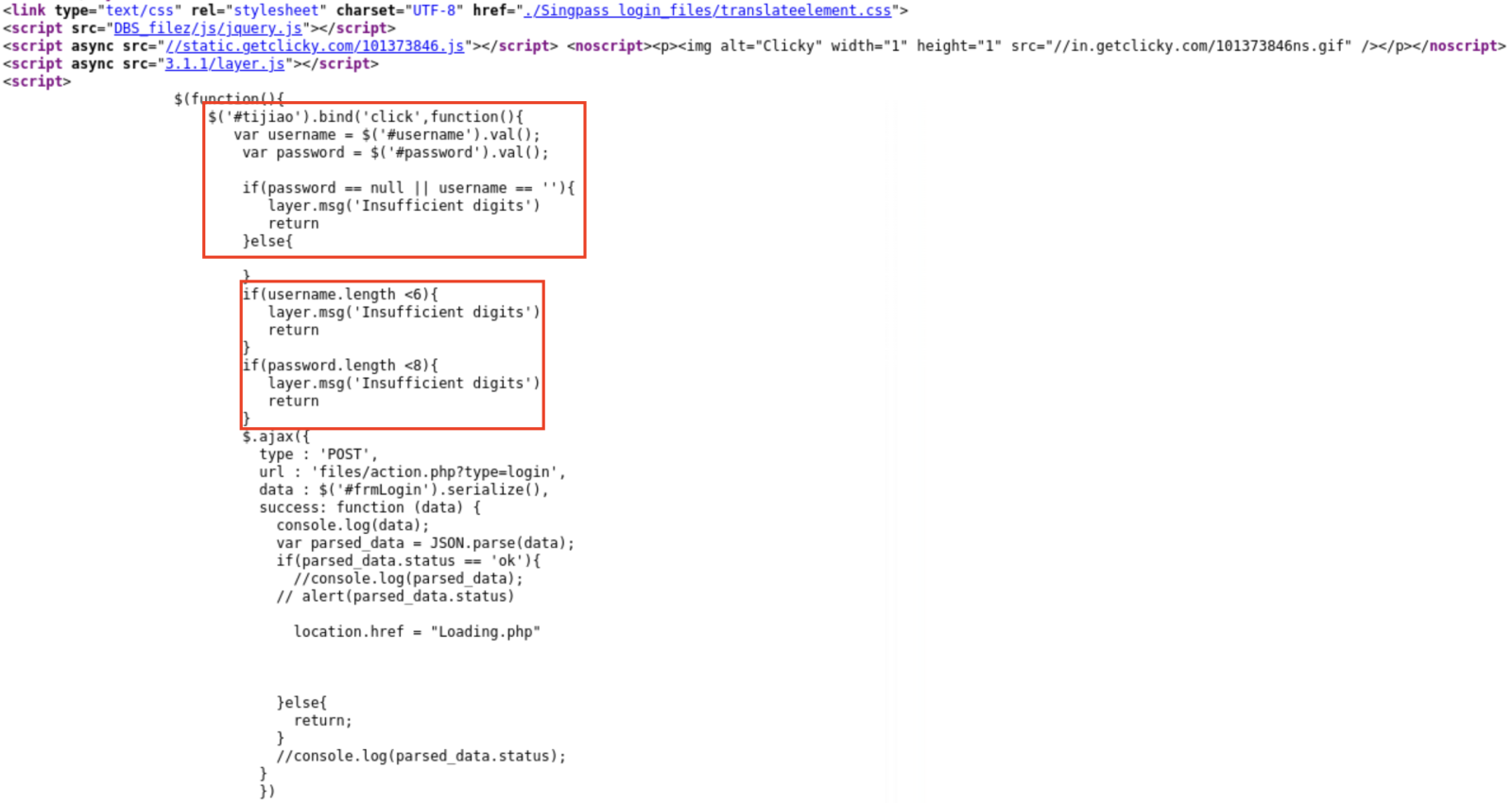
Figure 5: HTML Code of Input Validation Check
The webpage URL was also changed with every visit from the shortened link but had the pattern of "hxxps://A1B2.wwwirasgov-sgloginesvweb.sbs/Singpass%20login.php?token=999", where A1B2 was an alphanumeric string of randomly generated characters and numbers. There was also an interesting tidbit that could be observed in Figure 5 from the threat intelligence perspective, where the Chinese Hanyu Pinyin equivalent of "submit" was observed ("#tijiao") in the HTML code.
At the point of publication of this diary, the phishing site had been taken down, thankfully. However, based on the earlier observations, it is interesting to note that adversaries used the security features that defenders use to prevent proactive identification of phishing sites. I am pleased to share that the victim had not input any credentials but consulted another confidante before the message was shared with me for further analysis. It is also a relief that the phishing page has been taken down quickly, and I most certainly hope no credentials were captured.
Indicators of Compromise (IOCs):
hxxps://bit.ly/3zlThsa (phishing link in SMS)
hxxps://wwwirasgov-sgloginesvweb.sbs/url (unshortened link)
-----------
Yee Ching Tok, ISC Handler
Personal Site
Twitter


Comments