Dealing With False Positives when Scanning Memory Dumps for Cobalt Strike Beacons
I updated my Cobalt Strike beacon analysis tool 1768.py to deal with false positives in Windows system's memory dumps.
When my tool is given a process memory dump or a system's full memory dump, it will search for the header of a beacon configuration.
This often gives false positives in full memory dumps. I have now introduced a sanity check (option -S), to hide these false positives.
Here is a short howto video.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com
Sysinternals Updates: Sysmon v14.0 and ZoomIt v6.01
Both Sysinternals utilities (Sysmon and ZoomIt) received updates that significantly extends their scope: Sysmon can now also block actions, and ZoomIt can record videos.
Sysmon
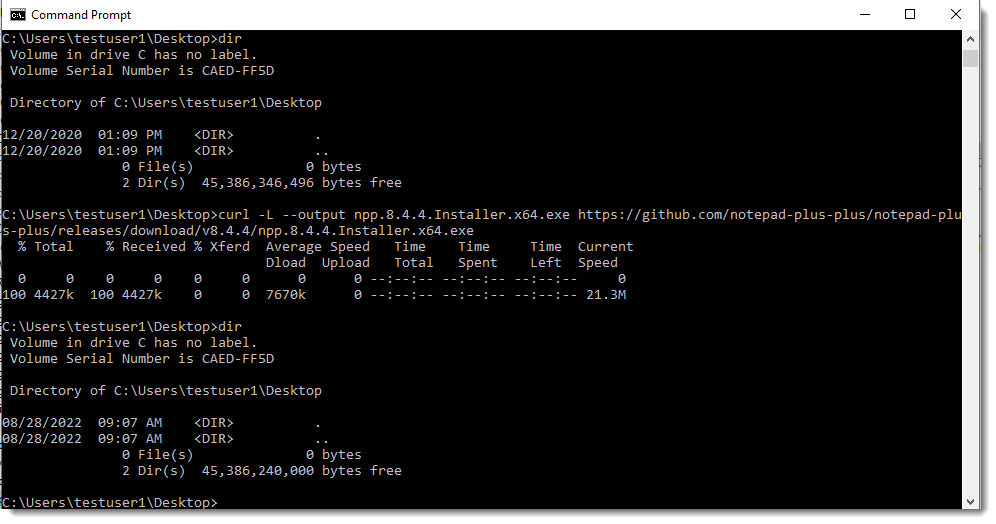
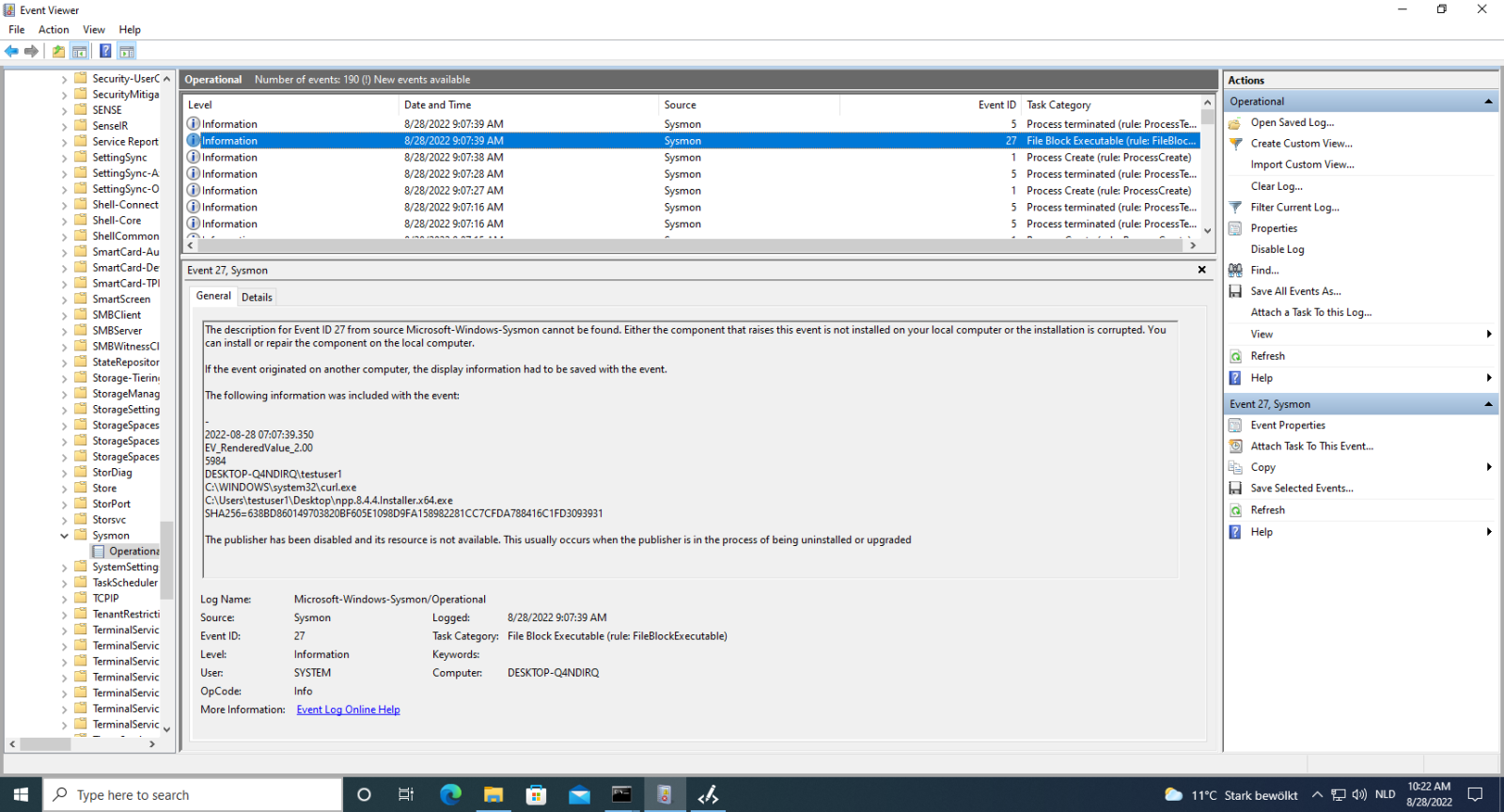
Event 27 (FileBlockExecutable) can now be used to block writing of executables to disk, when they match the given conditions.
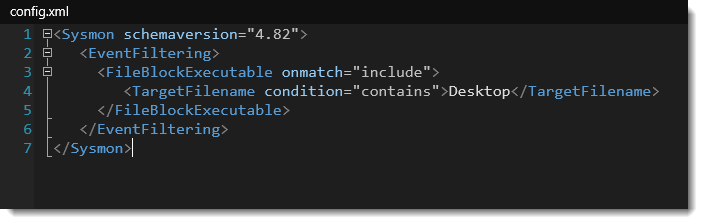
For example, here I use a rule to block the writing of executables to any file path & name that includes the string Desktop:
ZoomIt
While ZoomIt is not a security tool, it can be handy while presenting to zoom in on your screen.
And now it can record your screen too:
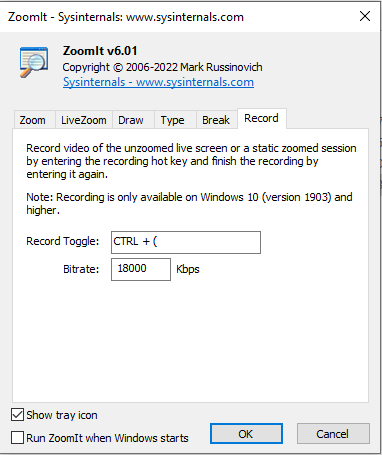
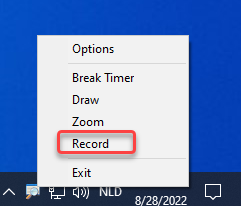
Even if you don't create videos, it can come in handy to quickly record a small howto for your colleagues.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com


Comments