Malicious Code Passed to PowerShell via the Clipboard
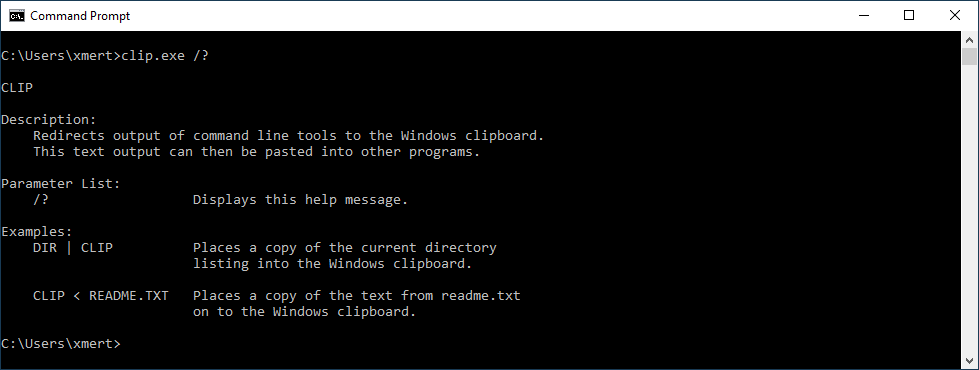
Another day, another malicious script was found! Today, the script is a Windows bat file that executes malicious PowerShell code but the way it works is interesting. The script has a VT score of 16/54 ( )[1]. The script uses the Windows command-line tool "clip.exe" which is often unknown to people:
This tool helps to save the STDIN content in the clipboard. I checked the LOLBAS[2] project page and did not find "clip.exe".
How does it work?
cmd / c echo "[Redacted_malicious_payload]" | clip.exe && powershell.exe "<code>"
The malicious code is saved into the clipboard and PowerShell fetches it by executing <code>. It contains:
[System.Windows.Clipboard]::GetText.invoke()
The code is executed and the clipboard is cleared:
[System.Windows.Clipboard]::SetText.invoke()
It's a nice technique to implement fileless malware!
Note: The malware family is Boxter[3].
[1] https://www.virustotal.com/gui/file/294de23e4f510838c370ffff2b297fbd38f7da5171988dca091569389b262d6a/content
[2] https://lolbas-project.github.io
[3] https://www.trendmicro.com/vinfo/us/threat-encyclopedia/malware/trojan.ps1.boxter.a
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | Greenwich Mean Time | Oct 27th - Oct 31st 2025 |


Comments
Anonymous
Jun 27th 2022
3 years ago
I look and see that we have at least two instances of clip.exe to watch for their execution, System32, SysWOW64 and some in WinSxS
Anonymous
Jun 27th 2022
3 years ago
Anonymous
Jun 29th 2022
3 years ago