Finding an Agent Tesla malware sample
I was browsing through the Any Run sandbox looking through the public submissions of malware with pcaps of infection traffic from Tuesday 2019-11-26. I found this one, and it's tagged agenttesla. Agent Tesla is an information stealer. Based on the file name, this Agent Tesla malware sample may have been disguised as an installer for Discord.
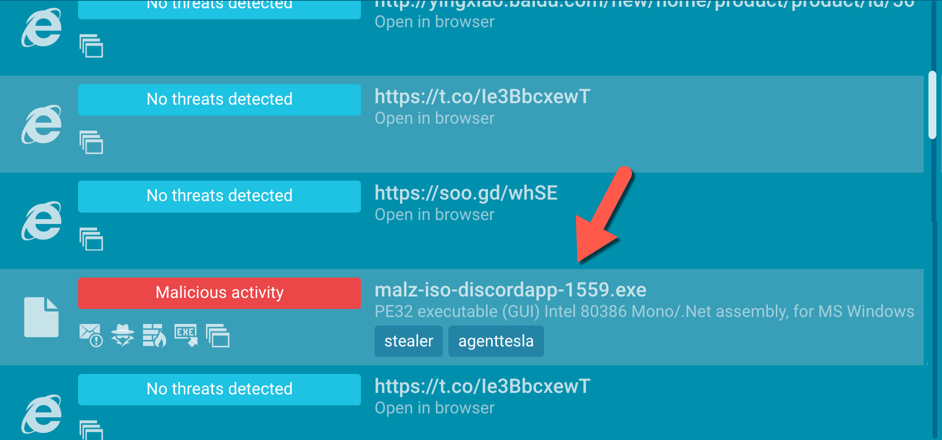
Shown above: The Agent Tesla malware sample I found on Any.Run.
I retrieved the pcap from Any.Run's analysis of this malware sample, so I could review the traffic. Agent Tesla sends an email containing information from the victim's Window host. In many cases, email traffic generated by Agent Tesla is encrypted SMTP, but sometimes the post-infection SMTP traffic is unencrypted. Luckily, this example was unencrypted SMTP.
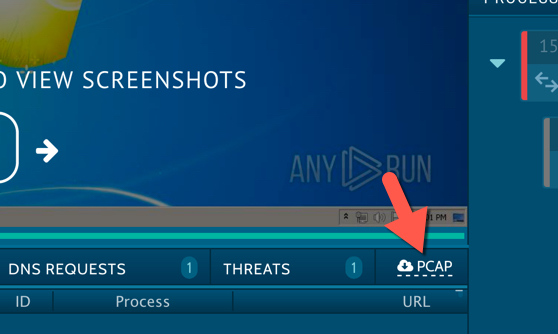
Shown above: Getting the pcap from analysis of the malware sample.
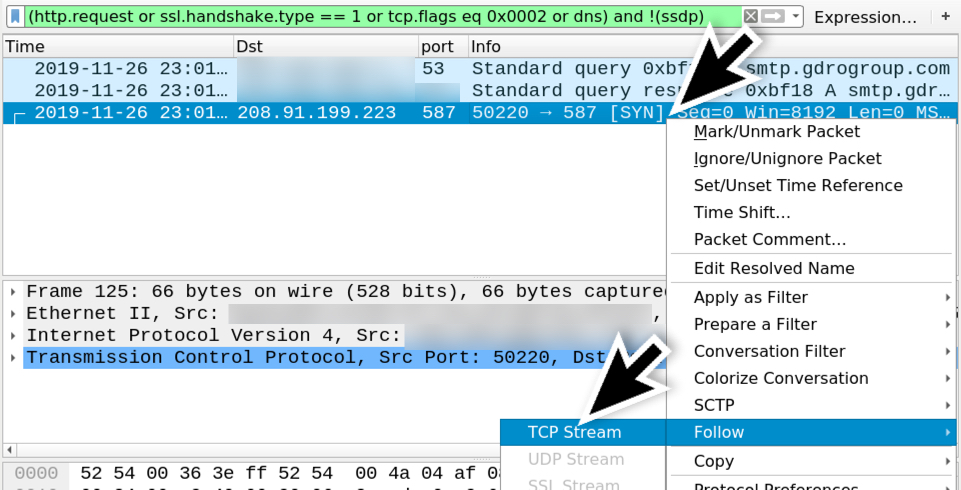
Shown above: Filtering on the pcap in Wireshark and finding the TCP stream to follow for the SMTP traffic (over TCP port 587).
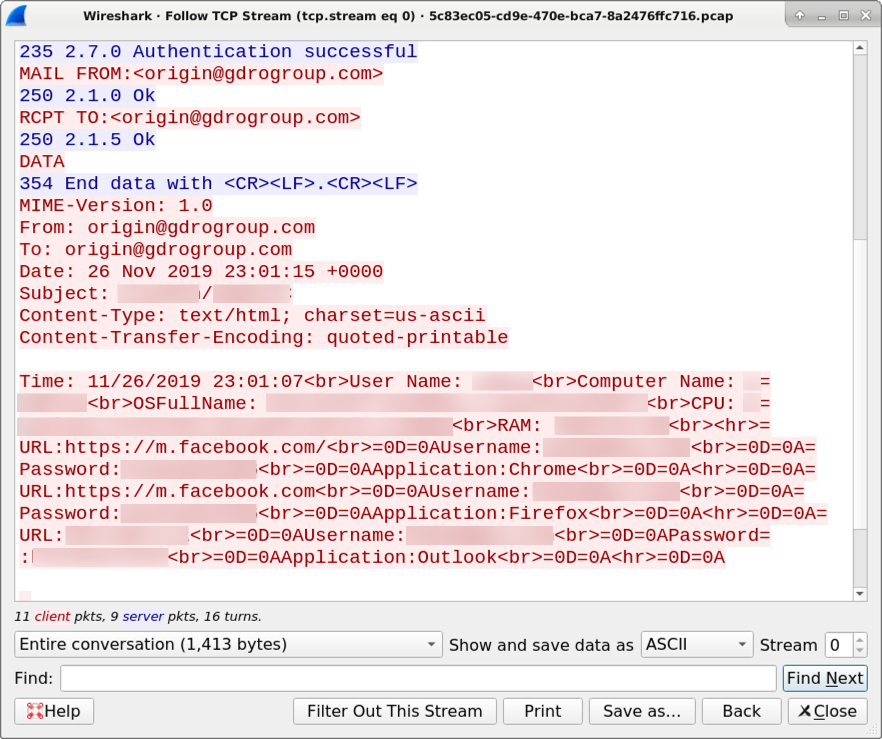
Shown above: TCP stream showing unencrypte SMTP traffic caused by this sample of Agent Tesla.
As shown in the image above, this sample of Agent Tesla malware exfiltrated stolen data to the email address origin@gdrogroup.com. I've filtered out what would normally be sensitive data in the above image, so if you're curious, you can review the pcap (here's a link again for the analysis page) and discover for yourself.
--
Brad Duncan
brad [at] malware-traffic-analysis.net



Comments
Anonymous
Nov 27th 2019
5 years ago