Costco, BestBuy, Walmart really want to send you a package!
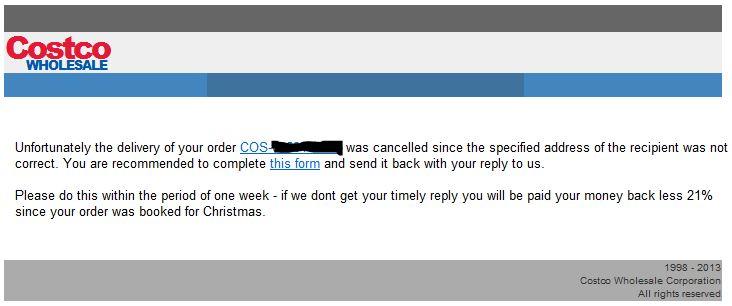
Yes, it's this time of the year again. There's a new wave of email making the rounds, with a message that looks as follows
The URLs look like this
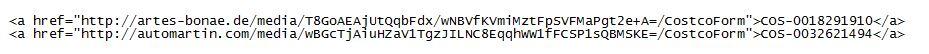
The subject seems to be one of "Delivery Canceling", "Express Delivery Failure" or "Standard Delivery Failure". Next to Costco, the same scam is currently ongoing for BestBuy and Walmart, maybe others. The links are (appear to be) random or encoded, there is no repeat occurrence of the URL and "package number" for the entire sample set that we have. It could well be that the BASE64 portion of the URL contains an encoded hash of the email address to which the phish was sent, so when you play with one of the samples, be mindful that you could be confirming the email address back to the bad guys [for that reason, the two URLs above are facsimile only, and not the real thing]
For a change, clicking on the link doesn't bring up a web form asking for your credit card number. Instead, it quite bluntly downloads a ZIP which contains an EXE. What makes this particular version more cute than others is that the EXE inside the ZIP is re-named on the fly, based on the geolocation of your download request. In my case, this spoiled the fun some, because "CostcoForm_Zürich.exe" and "CostcoForm_Hamburg.exe" didn't look all that credible: There are no Costcos in Switzerland or Germany :).
We have seen this "geolocation" approach at malware delivery used more frequently in the past weeks, for example also in a WhatsApp spam spree ten days ago. I assume someone who would click on "CostcoForm.exe" might be even more inclined to do so if the file is called "CostcoForm_DesMoines.exe" or the like, and the user is in fact residing in that same town.
As for the malware: Lowish detection as usual, Virustotal 12/44 . Malwr/Cuckoo analysis. The malware family so far seems to have a MUTEX of "CiD0oc5m" in common, and when run, it displays a Notepad that asks the user to try again later (while the EXE installs itself in the background). Further analysis is still ongoing.
Hosts currently seen pushing the malware include
bmaschool.net Address: 61.47.47.35
bright-color.de Address: 78.46.149.229
am-software.net Address: 64.37.52.95
artes-bonae.de Address: 81.169.145.149
automartin.com Address: 46.30.212.214
almexterminatinginc.com Address: 50.63.90.1
brandschutz-poenitz.de Address: 81.169.145.160
All these sites have been on the corresponding IP addresses since years, which suggests that these are legitimate web sites that have been compromised/hacked, and are now being abused to push malware.
If you have additional info on this scam, especially if you have seen the same scam for companies besides Costco, Walmart and Bestbuy, please let us know in the comments below, or share a sample via our contact form.


Comments
da-fortunato.de/media/ (arrived Monday)
zakenkantoorvancauwenberghe.be/message/ (arrived Saturday)
They both purport to be from Walmart.
I can upload both emails if they would be of any help.
M
Anonymous
Dec 24th 2013
1 decade ago
Anonymous
Dec 24th 2013
1 decade ago
If you curl/wget these with the wrong or no user-agent it will fake 404 or something else. If you view them with linux or a mac, the user-agent will get you the same.
IE or Win+Firefox (usually) will get you the zip file. If you try too many times, the downloader will blacklist you.
These are a problem because you can report them to badwarebusters, et al, and they never get flagged because they look clean on casual inspection with the wrong user-agent.
There will also be some php back-door files installed on the host. Because of the fake 404s, these servers can stay compromised for months.
See:
http://rebsnippets.blogspot.com/2013/05/phishing-malware-as-service-this-blog.html
These are essentially the same as the WhatsApp / White Wedding Agency / and many others.
Someone usually has to actually contact the hostmaster or webmaster and tell them exactly what files/directories to look for.
Another hint. curl -I the url, compare that 404 with curl -I the url purposely mangled for the real 404.
Anonymous
Dec 24th 2013
1 decade ago
andysarcade.de
Anonymous
Dec 24th 2013
1 decade ago
fasaltrading.com
www.dibig.de
Anonymous
Dec 27th 2013
1 decade ago
http://garwarner.blogspot.com/2013/12/holiday-delivery-failures-lead-to.html
The same malware is being used in the "Court" spam as one of your other handlers has already observed.
Gary Warner
Malcovery Security
www.malcovery.com
Anonymous
Dec 27th 2013
1 decade ago
I have received three emails stating that there was a delivery failure due to the delivery address not being correct. They all state that if I don't reply within one week of the dated email that they would refund my money minus 17% . Dec. 25/13 8:11am invoice # WM 007502651, Dec. 27/13 9:04am invoice # WM 008068022 and Dec. 29/13 9:51pm invoice # WM 009546603.
There should be some kind of criminal charges applied to these individuals who Falsely misrepresent these companies, as well as stealing personal information from people who are naive enough to actually fall for these illegal and immoral practises.
I hope to see more feedback from everybody.
Thanks. Bill
Anonymous
Dec 30th 2013
1 decade ago
?
Thank you for your order
Actions
Best Buy (order@miracatstore.com)
Add to contacts
12/04/14
From:
Best Buy (order@miracatstore.com) Microsoft SmartScreen classified this message as junk.
Sent: Thu 12/04/14 8:29 PM
To: ######@hotmail.com
1 attachment | Download all as zip (103.2 KB)
BestBuy_Order_ID_6758450MN.zip (103.2 KB)
E-shop Best Buy has received an order addressed to you which has to be confirmed by the recipient within 4 days.
Upon confirmation you may pick it in any nearest store of Best Buy.
Detailed order information is attached to the letter.
Wishing you Happy Thanksgiving!
Best Buy
From:
Costco (support@businesscontinental.com) Microsoft SmartScreen classified this message as junk.
Sent:
To: #####@hotmail.com
Our online store Costco.com received an order and the personal data of the recipient coincide with yours.
You may get your order in the nearest Local Store.
Attention! Your order can be reserved within 4 days.
You may see order details here.
Happy Thanksgiving Day!
Truly yours,
Costco.com
Anonymous
Dec 5th 2014
1 decade ago
Anonymous
Dec 6th 2014
1 decade ago
Anonymous
Dec 6th 2014
1 decade ago