Fake tech reps calling
Fake Anti-Virus isn't enough, now we also have to contend with fake Microsoft reps! This scam has been going on for a while, but continues to be rampant, which suggests that it is quite successful for the bad guys.
ISC reader Fred received such a call earlier today. The caller claimed to be from the "Tech department of Windows" and asked Fred to open the event viewer via run command, to check for errors or warnings. Of course there were some errors (it is Windows, after all :-), but the alleged techie then theatrically exclaimed "You indeed have the deadly errors" .. and proceeded to ask Fred to connect to www.ammyy.com and launch a remote desktop app. Fred, savvy security guy that he is, went there with Firefox and Noscript, and while Fred was still launching Wireshark to capture the next steps, the alleged Windows techie got cold feet, and hung up.
Bottom line: If "tech support" calls you without you having opened a ticket with them first, be veeery suspicious. Chances are high it is a scam.
Tomorrow, the world will end
No, this isn't about the Mayan calendar, and that particular instance of "End of the World" is anyway not scheduled to happen until December 21st.
This is about March 31st, and the announcement by "Anonymous", or those who claim to be "Anonymous", to wipe out the DNS root servers with a Distributed Denial of Service (DDoS) attack on March 31. Cricket Liu, the author of most of the O'Reilly DNS books and an authority on the subject, has posted a good blog entry at http://www.cricketondns.com/post.cfm/could-a-ddos-attack-against-the-roots-succeed, explaining in-depth that while such an attack is theoretically feasible, it is unlikely to succeed at a large scale.
We'll have to see. If DNS stops working tomorrow, we at least only have to live without it until December 21st, when the world will end for good anyway :).
7 Comments
Adobe Flash Player APSB12-07 - 28 March 2012
Adobe released a critical update today for Flash Player.
The basic gist is that most of the platforms are exposed to a crash and a remote attacker can get potential control of your system. Details elude to memory corruption as the cause, which are patched with this update.
APSB12-07 http://www.adobe.com/support/security/bulletins/apsb12-07.html
Flash Auto-update Feature http://blogs.adobe.com/asset/2012/03/an-update-for-the-flash-player-updater.html
Adobe Security Bulletins http://www.adobe.com/support/security/index.html
Many thanks to our readers Michael, Toby, Fred, Rene' and Mike for keeping on top of things and sending in links to us.
Keep it coming!
3 Comments
Wireshark 1.6.6 and 1.4.2 Released
Wireshark released today version 1.6.6 and 1.4.12 that includes fixes for several vulnerabilities.
Highlights
Versions 1.6.6 include updates for the following protocols:
- ANSI A, BSSGP, DIAMETER, DTLS, GOOSE, GSM Management, GTP, HTTP, IAX2, IEEE 802.11, IPP, ISAKMP, ISO SSAP, MP2T, MPLS, MySQL, NTP, PacketBB, PGM, Radiotap, SSL, TCP, UDP, USB, WSP
The following new and updated capture file support is included in this update:
- Endace ERF, Pcap-NG, Tektronix K12
Versions 1.4.12 include updates for the following protocols:
- HTTP, ISAKMP, MySQL, PacketBB, PGM, TCP, UDP
The following new and updated capture file support is included in this update:
Endace ERF, Pcap-NG.
The updates are available here.
[1] http://www.wireshark.org/download.html
[2] http://www.wireshark.org/lists/wireshark-announce/201203/msg00000.html
[3] http://www.wireshark.org/lists/wireshark-announce/201203/msg00001.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
ISC Feature of the Week: ISC Poll
Overview
Your vote counts! The ISC Poll https://isc.sans.edu/poll.html is a quick and easy way to weigh in and compare your answer to hundreds of others in the industry. A new poll is posted occasionally to gauge the opinion or interest of current events and topics. The latest poll is always in the right column of the homepage. You can jump to the poll page, vote/comment or view results directly from the box.
Features
Current Poll
https://isc.sans.edu/poll.html#results Each poll consists of a question and list of answers to choose from and generally a comment box for additional information about your answer. Choosing an answer and clicking the Vote button will automatically display the poll results and selected comments.
Archive Polls
https://isc.sans.edu/poll.html#poll_archive Previous poll questions are listed newest to oldest. Clicking the question will show poll results and selected comments.
Post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center https://isc.sans.edu
0 Comments
Firefox 3.6 EOL
Ever since Mozilla started its controversial new versioning scheme, Firefox 3.6 was still maintained as a stable and supported version of Firefox. Today, Mozilla announced that Firefox 3.6.28, to be released "over the next few weeks", will be the final version of Firefox 3.6. As of April 24th, no more security fixes will be published for Firefox 3.6
Of course, the Firefox version number is at first just a number. One could consider the just released Firefox "11" more like a Firefox 4.11.0 (or 5.11.0). However, plugins and extensions have never quite caught up to the new versioning scheme.
A Firefox add-on XPI file is a "zip" file, that once unpacked reveals a number of components, including a "install.rdf" file, which among other settings governing the install of the extension lists the range of version numbers for which a certain extension will work. Developers usually do not include future major versions as changes to the extension API and to the Firefox feature set will make it necessary to adapt the extension. This will require extension developers to consistently maintain and update extensions as Firefox releases new major versions.
In some ways, this may be a good thing as this will remove unmaintained extensions. In other ways, developers of valuable extensions may get discouraged by this practice. As a user, you could edit install.rdf file, and modify the range of supported versions. I have done this in a couple cases myself, and had decent succes. However, there is a good chance that this will fail in some cases.
http://blog.mozilla.com/futurereleases/2012/03/23/upcoming-firefox-support-changes/
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
8 Comments
evilcode.class
Exploit authors sometimes like to be cute:
A Java archive called "fun.jar" containing an "evilcode.class" file that runs as an applet of 1x1 pixels size ... well, this can't be anything good. And it indeed isn't. This code snippet was lurking on quite a few web sites over the past days.
Sending fun.jar to Virustotal shows that only 10 of 43 anti-virus tools actually recognize the exploit code, whereas 27/43 recognize the d.exe malware file that the exploit currently downloads and runs.
Evilcode.class exploits the Java Rhino Engine vulnerability (CVE2011-3544), published back in October 2011 and affecting all Java Runtime Engines up to JRE 1.6_27. The exploit still seems to work well enough for the bad guys that they don't see any need to re-tool to newer exploits. In slight modification of Oracle's own words:
![]()
2 Comments
ISC Feature of the Week: Presentations and Papers
Overview
ISC's https://isc.sans.edu/presentations/ is a informative list of detailed presentations and papers written by ISC handlers or written about the ISC and DShield. Note that not all of them are hosted on this site.
Features
Webcasts / Podcasts - https://isc.sans.edu/presentations/#casts
- ISC Monthly Threat Updates webcasts on SANS' Webcast archive
- Latest webcast PDF (Now posted along with webcast on access page)
- ISC Podcasts main page
Flyers / Cheat Sheets - https://isc.sans.edu/presentations/#sheets
- ISC Flyer
- IPv4 and IPv6 flyers
Reference Papers - https://isc.sans.edu/presentations/#reference
- Link to SANS Reading Room
SANSFIRE Presentations - https://isc.sans.edu/presentations/#sansfire
- SANSFIRE 2012 is coming up! http://www.sans.org/sansfire-2012/
Other Recent Presentations - https://isc.sans.edu/presentations/#recent
Older Presentations - https://isc.sans.edu/presentations/#older
Post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center (https://isc.sans.edu)
0 Comments
Virus Bulletin Spam Filter Test
Virus Bulletin updated its spam filter test, and found that compared to last year, spam filters are doing worse. Sadly, the detailed results are only for paid subscribers. But Virus Bulletin published a brief summary of the latest result as a teaser [1].
I think this is not all bad news. To understand this, one has to consider that the overall volume of spam has dropped significantly. The take down of some large botnets removed a lot of easy to classify spam off the net, leaving a more diverse "spam zoo" that is not as easy to classify. So I don't think this trend is as "worrying" as Virus Bulletin makes it sound.
[1] http://www.virusbtn.com/news/2012/03_18.xml
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
A Reminder: Private Key Security
One of the special features of Stuxnet was the use of a stolen private key to sign drivers. This made it harder to detect the injected files as malicious. Since (and before) Stuxnet, we have seen stolen keys used a few times. Most recently, Kaspersky is reporting about malware which employs a key stolen from Swiss company Conpavi AG [1].
Time to re-visit some of the best practices to secure the private key. These rules are written with SSL keys in mind, but apply to other private keys as well (ssh, PGP, code signing...)
First of all, limit the machines that the private key "touches". Ideally, you have an isolated system that is used to create the key and to back it up. Then, a dedicated USB key, a CD or another non-network medium is used to move the key to the server. At least one certificate authority I am aware of offers to create the private key for you. DONT. The certificate authority only needs the public key which is included in the certificate signing request. It does not need the private key and should never ask for it.
It is possible to encrypt the private key. It very much depends on the use case if this is appropriate or not. For a server SSL key, this would imply that you will need to enter the passphrase whenever you restart the service. On the other hand, the key should only be readable by "root". In this case, if an attacker already has root, the attacker may be able to read the encrypted key directly from memory. However, for keys used for code signing or e-mail signatures or encryption, entering the pass phrase is more feasible.
In some cases, the private key can be stored on a smart card and secured with a PIN. This is preferred for interactive applications if the key is used to log in to a system. For ssh, it is frequently required to use the key for automatic cron/batch processes. In this case, a specific key can be generated and its permissions can be limited (this is a topic for a follow up diary on securing ssh).
Before generating a key pair, think about how it is used and what parameters should be selected. Here are some of the options:
- Key Strength: For RSA, a 2048 bit key is said to be equal in strength to a 112 bit symmetric cipher key. This is sufficient for most applications, but 4096 bits is typically preferred as it is still feasible and doesn't "break the bank" for CPU cycles on a modern server.
- Algorithm: RSA is usually providing the best tradeoff with respect to speed and security, but for some applications, DSA may be more appropriate. Read up on the particular application and find out what algorithm works best.
- Entropy: good keys need good random numbers. It can be hard to create good random numbers on a system that is used exclusively to create keys. Sometimes, I prefer to create the key on the target server and then move it to a USB stick for backup. I haven't tried it yet, but I assume that a simple game like Solitair may be useful ;-) (you do want to install something that is part of the core OS install in order to avoid additional untrusted software).
- key transfer: if you don't create the key on the target server, you have to move it somehow to the target server. Even if you create it on the target server, a backup may be necessary. The key should only be moved over an encrypted connection or "in hardware" (= USB token). I would try and avoid having all keys on one USB token (imagine plugging it into an infected server!). The keys should be encrypted "at rest" . A backup to DVD or CD may sound wastefull (couple KB of keys on a GB of DVD), but its < $1 per key, hopefully less money then you made reading this article. CDs and DVDs are easily archived and accounted for. However, not all servers have DVD/CD drives.
There are a number of harware solutions to store keys that are more appropriate for servers. They tend to be a bit more pricey (I have seen them for $500) and may not work in all cases.They are typically referred to as hardware security modules (HSM) and they may include random number generators.
Any other ideas? Anything I missed?
[1] http://www.securelist.com/en/blog/682/Mediyes_the_dropper_with_a_valid_signature
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
13 Comments
LAN Airlines scam - Social Engineering Attacks still happening and will keep happening ...
This diary is being posted in both english and spanish, because it is a local attack that happened to Colombia users. I am unsure if this attack has been seen in other countries as well.
BEGIN OF ENGLISH SECTION
Last friday, many users at my company received the following message:
This e-mail is rejecting a change of flight request because the existing Mastercard credit card cannot be used because of lack of contract between Mastercard and LAN Airlines and states that for approval the airline needs a VISA Credit Card Number, CVC, Expiring date, name of card owner, ID and phone number.
My team began to receive many reports about this e-mail. There was a Reply-to directive to a gmail e-mail that would receive all the information sent by the users. First thing we did was to get a full report on what uses received this e-mail. Second, we sent a warning telling those users to avoid sending any confidential information though e-mail. Third and last, we proceeded to call every user to enforce the warning.
15 minutes passed between receiving the SCAM e-mails and sending the warning e-mail to my users. 183 users were targeted and 8 sent their information because they purchased tickets to LAN and thought that the mail was legitimate. We gave them a final recommendation to report their credit card as lost so they can get a new one with a new number.
We keep doing Security awareness campaigns on a regular basis and they start the moment the employee starts working in the company. I just hope there will be one day where users won't be that naive to risk their private information or the company information assets.
END OF ENGLISH SECTION
BEGIN OF SPANISH SECTION
El viernes pasado, muchos usuarios corporativos en mi empresa recibieron el siguiente correo electrónico:
Mi equipo empezó a recibir muchos reportes sobre este correo. Al revisarlo en detalle, nos dimos cuenta que el correo incluía una directiva Reply-to, la cual direccionaba hacia un correo de gmail todas las respuestas de los usuarios a dicho mensaje. Lo primero que hicimos fue sacar una lista de todos los destinatarios del mensaje de correo en la figura. Lo segundo fue enviar un correo electrónico de advertencia a dichos usuarios advirtiendoles del peligro y de abstenerse de enviar cualquier información confidencial vía correo electrónico. Por último, se realizaron llamadas a cada uno como medida adicional para reforzar la advertencia realizada.
Pasaron sólo 15 minutos entre la recepción del correo malicioso y el envío de la advertencia. De un universo de 183 usuarios a quienes se les envió el correo electrónico malicioso, 8 enviaron la información solicitada porque habían comprado recientemente tiquetes con LAN y creyeron que el correo que les enviaron era legítimo.
Continuamente realizamos campañas de sensibilización de seguridad a todos los usuarios y estas inician desde la misma inducción del usuario al entrar a laborar en la compañía. Solo espero que llegue un día en que los usuarios no sean tan ingenuos con correos como estos en donde puedan poner en riesgo su información personal o los activos de información de la compañía.
END OF SPANISH SECTION
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter:@manuelsantander
Web:http://manuel.santander.name
e-mail:msantand at isc dot sans dot org
2 Comments
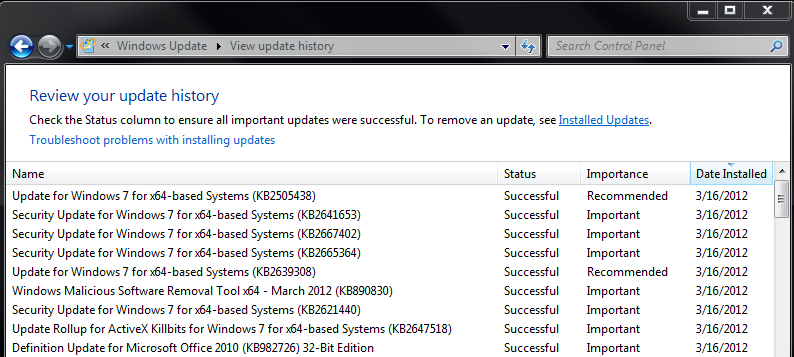
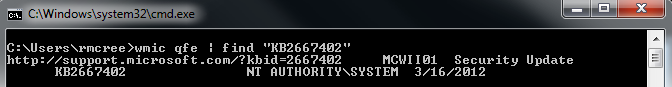
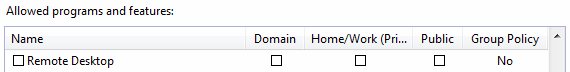
MS12-020 RDP vulnerabilities: Patch, Mitigate, Detect
As a follow up to the fact the we've raised the INFOCON level to yellow for MS12-020, a step not taken lightly, it was suggested that we offer a few simple things folks can do to ensure that they're patched appropriately, as well as employ possible mitigations and detection.
4 Comments
INFOCON Yellow - Microsoft RDP - MS12-020
As we feared the MS12-020 bulletin from last black Tuesday caused a race for finding an exploit.
The last few evolutions in that process cause our worries to increase significantly. In order to help raise awareness and call administrators to action, we're raising our INFOCON to YELLOW for 24 hours.
Some history:
- Luigi Auriemma found a problem on May 16th, 2011.
- Microsoft was warned on August 24th, 2011 working with TippingPoint's Zero Day Initiative
- Microsoft released bulletin MS12-020 on March 13th, 2012, crediting "Luigi Auriemma, working with TippingPoint's Zero Day Initiative, for reporting an issue described in MS12-020"
- Luigi Auriemma released his work on March 16th, 2012
Luigi wrote today: "now that my proof-of-concept is out (yeah rdpclient.exe is the poc written by Microsoft in November 2011 using the example packet I sent to ZDI) I have decided to release my original advisory and proof-of-concept packet written the 16 May 2011... full-disclosure as usual :)" and he released his analysis and exploit of the vulnerability.
This is expected to speed up the efforts of the bad guys significantly and gives those having exposed RDP services very little time to fix before it will get exploited somehow.
The clock is ticking, please consider:
- block off RDP from all sources but those you absolutely need
- install the Microsoft patch
--
Swa Frantzen -- Section 66
6 Comments
VMware New and Updated Security Advisories
VMware issued the following security advisories:
VMware View privilege escalation and cross-site scripting (VMSA-2012-0004) [1] and VMware vCenter Server, Orchestrator, Update Manager, vShield, vSphere Client, ESXi and ESX address several security issues (VMSA-2012-0005) [2].
[1] http://www.vmware.com/security/advisories/VMSA-2012-0004.html
[2] http://www.vmware.com/security/advisories/VMSA-2012-0005.html
The following advisory has been updated:
VMware ESXi and ESX updates to third party library and ESX Service Console address several security issues (VMSA-2012-0001.1) [3]
[3] http://www.vmware.com/security/advisories/VMSA-2012-0001.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
ISC Feature of the Week: Infocon
Overview
You can view the current Infocon status at https://isc.sans.edu/infocon.html as well as in other areas of our site.
The intent of the 'Infocon' is to reflect changes in malicious traffic and the possibility of disru pted connectivity. Our handlers monitor DShield logs, emails and numerous other internet sources in order to determine if the Infocon level should be adjusted. There are 4 definition levels of the Infocon as outlined below.
Features
Link To Current Infocon Status - https://isc.sans.edu/infocon.html#link
- A text box, for easy copy/paste, contains the HTML code you need to display the current Infocon status graphic and link back to ISC site.
- https://isc.sans.edu/infocon.txt - returns a text representation of the current Infocon level, you can include
- https://isc.sans.edu/infocon.js - sets a javascript variable you can include in your code
- https://isc.sans.edu/daily_alert.html - returns an HTML page of the current Infocon status as well as the title/link to the latest diary entry.
Applications and Widgets - https://isc.sans.edu/infocon.html#apps_and_widgets
There are a variety of additional ways to keep an eye on the Infocon level. Methods include Windows systray, OS X widget, KDE application, nagios alerts and Firefox extension.
Infocon Definition - https://isc.sans.edu/infocon.html#definition
Note: There is a Blue TEST status not used in everyday alert levels.
- Green - Everything is normal
- Yellow - Currently tracking a significant new threat
- Orange - Major disruption in connectivity is imminent
- Red - Loss of connectivity across a large part of the internet.
Infocon HIstory - https://isc.sans.edu/infocon.html#infocon_history
A list of Infocon changes by date with a reason and link where possible.
What ways and where do you use the Infocon? Share suggestions or feedback in the section below or send us any questions or comments in the contact form at https://isc.sans.edu/contact.html
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center (http://isc.sans.edu)
2 Comments
Why We Rated the MS12-020 Issue with RDP "Patch Now"
Microsoft's March 2012 "Black Tuesday" announcement included the MS12-020 patch, which fixes a vulnerability in Microsoft's implementation of RDP. This vulnerability (CVE-2012-0002) could allow a remote unauthenticated attacker to execute arbitrary code on the affected system. Microsoft labeled this issue "Critical" and we assigned it our highest severity label "Patch Now" for servers. Here's why:
- The CVE-2012-0002 vulnerability applies to most flavors of Microsoft Windows.
- It can be exploited over the network.
- Companies often make RDP accessible on the standard TCP port 3389 from the Internet for remote access to servers and sometimes workstations.
These factors make it very attractive for attackers to attempt reverse-engineering Microsoft's MS12-020 patch to, understand the details of the bug and craft an exploit. This will likely happen sooner than 30 days. The universal applicability of the exploit and its targetability over the Internet and internal networks might motivate the creation auto-propagating worms to capture systems quickly and efficiently.
For these reasons, we recommend applying the MS12-020 patch as quickly as practical in your environment. Until you install the patch, consider moving your RDP listeners to non-standard ports. You should also explore the applicability of Microsoft's advice to enable Remote Desktop’s Network Level Authentication (NLA). This will mitigate the problem: "On systems with NLA enabled, the vulnerable code is still present and could potentially be exploited for code execution. However, NLA would require an attacker to first authenticate to the server before attempting to exploit the vulnerability."
------
Lenny Zeltser
zeltser.com
@lennyzeltser
17 Comments
Please transfer this email to your CEO or appropriate person, thanks
The following domain name registration scam has been making rounds at least for a couple of years. Its longevity suggests that it remains effective at separating the victims from their money. The scam's email messages usually begin with the phrase:
"(It's very urgent, Please transfer this email to your CEO or appropriate person, thanks)"
The message is typically addressed to the generic title of CEO, President or Principal without specifying the person's name. It claims to come from a Chinese domain registration organization and states that some company is trying to register Asian versions of the domain name associated with the recipient's company, in TDs such as:
.asia, .cn, .co.in, .com.cn, com.hk, com.tw, .hk, .in, .net.cn, .org.cn, .tw
The text urges the recipient to contact the sender to protect this domain from the alleged impostor. Here's a sample:
"After our initial checking, we have found the name were similar to your company's, so we need to check with you whether your company has authorized that company to register these names. If you have authorized this, we will finish the registration at once. If you have not, please let us know within 7 workdays, so that we will handle this issue better. Out of the time limit we will unconditionally finish the registration for 'Arub Asia Investment Ltd'."
The sender signs off with "Best Regards" and includes an email signature block that usually looks like this:
"Best Regards,
Charles Chen
Tel:+86-5515223114 Fax:+86-5515223113
No.1688 Taihu Road,Baohe District,Hefei,Anhui,China"
The text of the email message is mostly the same as it was when we saw this scam in 2010, though the sender's name, company association, domain name and address details are different.
Blogger Michael Lerner described his email interactions with the company sending such email messages in 2010, which confirmed that the scammers' goal was to convince the victim into registering the domain names in question through their company. Here's an excerpt from a response to Michael's correspondence:
"If you think his registration will confuse your clients and harm your profits, we can send an application document to you and help you register these domains within our approving period. This is a better way to prevent domain name dispute"
The most recent variant we've seen asked the sender to respond to "charles.chen@dnsip-net.com.cn". The website residing at that domain claims to belong to a "comprehensive company engaged in the Internet intellectual property services that mainly provides network-based service, network intellectual property service, network promotion service, etc." The organization's website includes the slogan "The Better Network, The Better Solutions." Searching for this slogan reveals lots of websites with nearly identical text and similar design.
If you analysed this old, yet still widespread scam, or if you have additional details to share regarding it, please contact us.
-- Lenny Zeltser
2 Comments
March 2012 Microsoft Black Tuesday
Overview of the March 2012 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS12-017 | Vulnerability in DNS Server Could Allow Denial of Service | |||||
| DNS Server CVE-2012-0006 |
KB 2647170 | no. | Severity:Important Exploitability: Likely |
N/A | Important | |
| MS12-018 | Vulnerability in Windows Kernel-Mode Drivers Could Allow Elevation of Privilege | |||||
| Kernel-Mode Drivers CVE-2012-0157 |
KB 2641653 | no. | Severity:Important Exploitability: Difficult |
Important | Important | |
| MS12-019 | Vulnerability in DirectWrite Could Allow Denial of Service | |||||
| DirectWrite CVE-2012-0156 |
KB 2665364 | no. | Severity:Important Exploitability: Unknown |
Important | Less Urgent | |
| MS12-020 | Vulnerabilities in Remote Desktop Could Allow Remote Code Execution | |||||
| Remote Desktop CVE-2012-0002 CVE-2012-0152 |
KB 2671387 | no. | Severity:Critical Exploitability: Likely |
Critical | PATCH NOW | |
| MS12-021 | Vulnerability in Visual Studio Could Allow Elevation of Privilege | |||||
| Visual Studio CVE-2012-0008 |
KB 2651019 | no. | Severity:Important Exploitability: Likely |
Important | N/A | |
| MS12-022 | Vulnerability in Expression Design Could Allow Remote Code Execution | |||||
| Expression Design CVE-2012-0016 |
KB 2651018 | no. | Severity:Important Exploitability: Likely |
Important | N/A | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
(**): The exploitability rating we show is the worst of them all due to the too large number of ratings Microsoft assigns to some of the patches.
------
Lenny Zeltser
zeltser.com
@lennyzeltser
2 Comments
OpenSSL Security Update
OpenSSL has issued a security update for the CMS and S/MIME Bleichenbacher attack (CVE-2012-0884). "SSL/TLS applications are *NOT* affected by this problem since the SSL/TLS code does not use the PKCS#7 or CMS decryption code." [1]
OpenSSL 0.9.8u and OpenSSL 1.0.0h are available for download here.
[1] http://www.openssl.org/news/secadv_20120312.txt
[2] http://www.openssl.org/source/
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
Apple Released Safari 5.1.4
Apple released Safari 5.1.4 for Windows as well as for OS X.
This update addresses a large number of bugs in Safari itself and in WebKit. Some of the issues fixed:
- Safari for Windows: An International Domain Name (IDN) issue with look alike characters. (I just patched Safari for OS X, and oddly, Safari still appears to render .com domains using international characters vs. punny-code. Firefox and Chrome do not show international characters for .com )
- All versions of Safari: While private browsing was active, sites were still recorded in the browsing history.
- 5 different cross site scripting vulnerabilities in WebKit
- a cookie disclosure vulnerability (WebKit)
- a cross origin issue in Webkit.
- 40 or more webkit issues that could lead to arbitrary code execution.
The update should be listed eventually at the standard Apple security URL: http://support.apple.com/kb/HT1222
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
An Analysis of Jester's QR Code Attack. (Guest Diary)
[This is a guest diary contributed by STI Student TJ O'Connor ] [Many claim this to a be a hoax]
This week saw an interesting turn in the US government's battle against the Hacker Group Anonymous. Official court documents and details emerged that finally showed that #sabu was turned by the US government as an informant to arrest and dismantle members from the LulzSec splinter cell. (Bray, 2012) In the last two days, another dramatic turn of events highlighted the demise of the once though invincible hacker group; a group the Director of the NSA said could be capable of hacking the power grid within a year or two. (Liebowitz, 2012)
A lone-wolf patriot hacker, known as Th3J35t3r, claims to have successfully targeted, exploited, and raided personal information from members of Anonymous, LulzSec, and Anti-Sec alongside Islamic Extremists and Al Qaeda, and Rhode Island State Representative Dan Gordon. If you are living in a cave and haven't heard about the Jester, read the SANS whitepaper. (OConnor, 2011) So how did the attack occur? And how can you protect yourself? Lets quickly answer these questions.
The Jester laid the groundwork for his attack over two weeks ago when he changed the ICON for his Twitter account @th3j35t3r.
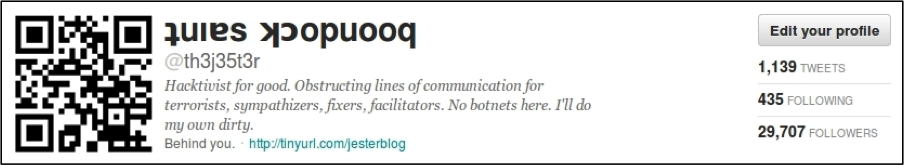
Here's where the Jester really relied upon his adversaries' technical prowess and curiosity as a weakness. Changing the photo to a QR-code, The Jester encoded a url address into the photo as seen in the photo. The victims used their mobile phones to scan the QR code and then visit the tinyurl address out of sheer curiosity. Since most of us (including the author) use our mobile phones to scan QR-codes, this allowed The Jester to scope his attack to browsers for the IOS and Android Operating Systems,. Both IOS and Droid rely heavily upon the WebKit framework for their web browser.
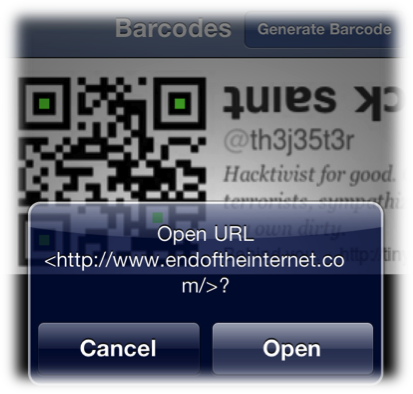
A Webkit exploit isn't necessarily novel. Previously exploits have succeeded in targeting Webkit. In 2010, Itzhak (Zuk) Avraham wrote a use-after free exploit for Webkit for the Droid 2.1 framework. (Abraham, 2010) Dr. Charlie Miller followed in March 2011 with a use-after-free Webkit exploit the IOS 4.2.1 operating system. (Naraine, 2011)
For a great example of how use-after-free exploits work, check out the Grey Corner Blog. Use-after-frees have been seen in usage for a while, especially during Advance Persistent Threat Attacks. Notably, the Operation Aurora attack that targeted Google succeeded via an Internet Explorer use-after-free vulnerability. By allocating memory for a specific object, then freeing the memory for the object, followed by accessing the pointer to the object's pointer can trigger arbitrary code execution. This can easily be combined with a technique known as heap spraying, filling the heap with executable code in multiple locations. When combined with a heap-spraying, a use-after free can jump to the heap to find its payload (shell code) and executes it.
In the Jester's attack this code executed a netcat command, passing the Twitter credentials to the Jester. At this point, the patriot hacker checked the credentials against a list of known targets before proceeding in his attack. Specifically targeted in the attack were @alemarahweb,@HSMPress @AnonymousIRC, @wikileaks, @anonyops, @barretbrownlol, @DiscordiAnon, @RepDanGordon.
Even under the current IOS 5.1, the com.atebits.Tweetie2 database contains com.atebits.Tweet2.plist which holds Twitter username, recent searches, device UDIDs, among other information that makes identifying specific users easy if they have the default Twitter application installed.
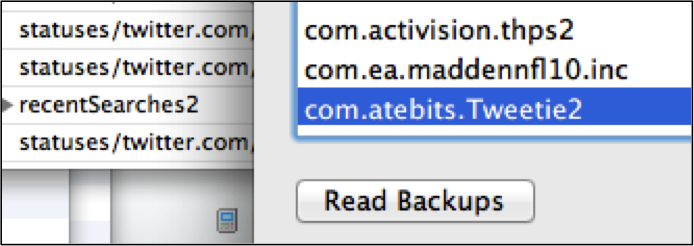
Next, the Jester raised his permissions on each exploited device. Under the IOS operating system, this proves trivial since the IOS has a default username/password combination of root/alpine. (Heider, 2012) Under Android, there are a variety of privilege escalation attacks. (Davi, 2010) With elevated privileges, the Jester then targeted specific databases that contained the SMS, Voicemail, Call Logs, and Email on the phone. Since, the default applications store all this data in default databases on the phone ; extracting this proves as easy as writing a few sqlite3 queries.
th3j35t3r$ sqlite3 sms.db SQLite version 3.7.9 2011-11-01 00:52:41 Enter ".help" for instructions Enter SQL statements terminated with a ";" sqlite> select address, text from message; +15555551234| Where can I download LOIC? +15555551234| Whats the new IRC Hivemind Server? +15555551234| Where can I find a good attorney?
At this point, the Jester has threatened to upload the contents of the raid to the Internet, holding the victims hostage. Unapologetic for the attack, the Jester continues his patriot hacking campaign.
"I also had a list of "targets" twitter usernames I was interested in, these were comprised of usernames of: Islamic Extremists, Al Qaeda Supporters, Anonymous Members, Lulz/Antisec Members EVERYONE else without exception was left totally "untouched" so to speak. This was a Proof of Concept QR-Code based operation against known bad guys, the same bad guys that leak YOUR information, steal YOUR CC nums, and engage in terror plots around the world. I do not feel sorry for them. In the interests of convenience I will be taking the liberty of uploading the captured bad-guy data in a signed PGP encrypted file to a suitable location very soon. How's that for "lulz"?
Included in the attack was US State Representative Dan Gordon. Angered over a 2010 new article about the US State Representative, (CBS, 2010) The Jester made the attack personal against the Representative. The twitter account for the US representative holds messages indicating that the FBI will now target The Jester under crimes ranging from threating a state official to hacking the cellular phone of the representative. As with all developing news, it is still unclear whether the representative's Twitter account has also been hacked with his phone. A less than professional message on Twitter leads us to believe his Twitter account has been hacked. This brings us to an interesting lesson learned in the attack. Once compromised on a mobile device, you must consider all your accounts compromised. Since our mobile devices often contain multiple mail, phone, contact, social media, and personal information ; we must consider all this information compromised.

Some technical questions still remain. The Pw2Own exploit used by Charlie Miller in 2011 could not bypass Address Space Layout Randomization (ASLR). Since OS 4.2.3, The iPhone has had a limited ASLR implementation that would have made Miller's exploit not work correctly. Did the Jester recycle Miller's 1-year-old exploit or did he upgrade it for iOS? If so, how did he bypass ASLR? Further, CVE-2010-1807 only works for Android 2.1 and below devices. How was this exploit upgraded? Additionally, would changing the default credentials on iOS (through jail-breaking the device) have prevented the privilege escalation portion of the attack against iOS? If the victims used non-standard mail, twitter, and SMS applications ; the attacker would not have not noticed them (Win one for security through obscurity.)
Although we are constantly reminded of the threats facing us, at least this threat was targeted and against specific members of Anonymous and Al Qaeda, which the majority of us do not belong in. But it reminds us of the threat that is out there. I'll repeat again what I've said multiple times: Cyber is assymetric warfare ; it favors the individual, it favors the adversary. Did the Jester just accomplish in two weeks what it took the federal government months and deals with a known criminal? Maybe, the details have yet to emerge.
References
Avraham, I. (2011, November 14) Android 2.0 / 2.1 Use-After-Free Remote Code Execution ÷ Packet Storm. Packet Storm ÷ Full Disclosure Information Security. Retrieved March 11, 2012, from http://packetstormsecurity.org/files/95850/Android-2.0-2.1-Use-After-Free-Remote-Code-Execution.html
Bray, C. (2012, March 9). FBI's 'Sabu' Hacker Was a Model Informant - WSJ.com. Business News & Financial News - The Wall Street Journal - Wsj.com. Retrieved March 11, 2012, from http://online.wsj.com/article/SB10001424052970204603004577269844134620160.html?mod=googlenews_wsj
CBSNEWS, (2011, November 24). Lawmaker's Gulf War claims, records don't match - CBS News. Breaking News Headlines: Business, Entertainment & World News - CBS News. Retrieved March 11, 2012, from http://www.cbsnews.com/2100-250_162-20111212.html
Davi, L. (2010, November 13). Privilege Escalation Attacks on Android. System Security Lab Ruhr-University Bochum, Germany. Retrieved March 11, 2012, from www.ei.rub.de/media/trust/veroeffentlichungen/2010/11/13/DDSW2010_Privilege_Escalation_Attacks_on_Android.pdf
Heider, J. (2012, February 27). Further Information on iOS Password Protection. Fraunhofer Institute for Secure Information Technology (SIT). Retrieved March 11, 2012, from http://sit.sit.fraunhofer.de/studies/en/sc-iphone-passwords-faq.pdf
Liebowitz, M. (2012, February 21). Could Anonymous Really Knock Out the Power Grid? - Technology & science - Security - msnbc.com. msnbc.com - Breaking news, science and tech news, world news, US news, local news- msnbc.com. Retrieved March 11, 2012, from http://www.msnbc.msn.com/id/46468844/ns/technology_and_science-security/t/could-anonymous-really-knock-out-power-grid/
Naraine, R. (2011, March 10). Charlie Miller wins Pwn2Own again with iPhone 4 exploit | ZDNet . Technology News, Analysis, Comments and Product Reviews for IT Professionals | ZDNet. Retrieved March 11, 2012, from http://www.zdnet.com/blog/security/charlie-miller-wins-pwn2own-again-with-iphone-4-exploit/8378
OConnor, T. (2011, December 30). SANS Reading Room. The Jester Dynamic. Retrieved March 11, 2012, from http://www.sans.org/reading_room/whitepapers/attacking/jester-dynamic-lesson-asymmetric-unmanaged-cyber-warfare_33889
4 Comments
VMware New and Updated Advisories
VMware issued the following security advisories:
The VMware vCenter Chargeback Manager contains a vulnerability that allows information leakage and DoS [1]. VMware recommend applying the following patch available here [2].
The VMware VirtualCenter and ESX, Oracle (Sun) JRE update 1.5.0_32 Oracle (Sun) JRE is updated to version 1.5.0_32, which addresses multiple security issues that existed in earlier releases of Oracle (Sun) JRE [3]. VMware recommend applying the following patch for VMware Virtual Center 2.5 Update 6b available here [4] (registered users with a valid serial number) and ESX350-201203401-SG and here [5].
The following advisories have been updated
VMware ESX third party updates for Service Console packages glibc and dhcp (VMSA-2011-0010.3) [6]
VMware ESXi and ESX updates to third party libraries and ESX Service Console (VMSA-2011-0012.3) [7]
VMware third party component updates for VMware vCenter Server, vSphere Update Manager, ESXi and ESX (VMSA-2011-0013.2) [8]
[1] http://www.vmware.com/security/advisories/VMSA-2012-0002.html
[2] http://downloads.vmware.com/d/info/it_business_management/vmware_vcenter_chargeback/2_0
[3] http://www.vmware.com/security/advisories/VMSA-2012-0003.html
[4] http://www.vmware.com/download/download.do?downloadGroup=VC250U6B
[5] http://downloads.vmware.com/go/selfsupport-download
[6] http://www.vmware.com/security/advisories/VMSA-2011-0010.html
[7] http://www.vmware.com/security/advisories/VMSA-2011-0012.html
[8] http://www.vmware.com/security/advisories/VMSA-2011-0013.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
Apple Patches
Apple's new mobile operating system, iOS 5.1, not only includes a number of new features, but also a large list of security relavant patches. Eventually, a link to the patches will be listed on Apple's security update page (http://support.apple.com/kb/HT1222)
iOS fixes the latest passcode lock bypass (CVE-2012-0644). In addition, a number of Safari and Webkit issues are fixed. In addition, code execution issues are fixed in the HFS subsystem (exploitable by mounting a corrupt disk), libresolv, and VPN configuration.
Note that the new Apple TV operating system, as well as the iTunes update add security fixes as well as new features. An update is recommended.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Reflected XSS in Splunk Web Affecting Version 4.0 to 4.3
A vulnerability has be found in Splunk 4.0 - 4.3 that allows partial confidentiality and integrity violation, when a user click on a specifically crafted link that can disclose sensitive information to the attacker. Splunk recommend consumers upgrade to version 4.3.1 and to follow its hardening standard [3] to mitigate the risk of exploitation.
[1] http://www.splunk.com/view/SP-CAAAGTK
[2] http://www.splunk.com/download
[3] http://docs.splunk.com/Documentation/Splunk/latest/Admin/Hardeningstandards
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
What happened to RFI attacks?
Recently, I noticed a remarkable decrease in remote file inclusion attacks against my web servers. Usually, I easily detected 100+ attacks per day using a simple regular expression match. These days, I see maybe a dozen (and they are usually only 2-3 distinct "attacks" meaning different exploits or different attackers.
The number of vulnerabilities exploited also decreased a lot, with many of the older vulnerabilities being no longer probed.
Have all vulnerable systems been exploited or cleaned up? These attacks where never very effective, and a lot of exploits used would not have been successful even against vulnerable systems. In addition, the attacks where usually launched blindly without recognizance, leading to a lot of hits to non existent pages.
For the few attacks still out there, the pattern doesn't have changed much. I checked out a couple of the payloads and they are either simple indicators or PHP IRC bots.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
2 Comments
ISC Feature of the Week: Follow us on Twitter
Overview
This week we feature Twitter accounts! ISC and the Handlers post on Twitter regularly. This is a great way to keep up with diary posts, current security information, Handler activities and more.
Features
ISC related tweets are tagged with the hash tag #sansisc.
ISC's twitter feed http://twitter.com/sans_isc is checked regularly and posts when a new diary is released, security news is published or special announcements are made. Note: Diary tweets begin with [Diary].
Our ISC account and Handlers that opt to list their twitter handles are available on https://isc.sans.edu/twitter.html.
An ISCHandlers list is at https://twitter.com/#!/tuxlien/ischandlers and mirrors the handlers list on our twitter page.
We also include Twitter feed boxes in the last row on the Dashboard at https://isc.sans.edu/dashboard.html.
Let us know in the section below if you have a suggestion or feedback or send us any questions or comments in the contact form at https://isc.sans.edu/contact.html
--
Adam Swanger, Web Developer (GWEB)
Internet Storm Center (http://isc.sans.edu)
2 Comments
Adobe Flash Player Security Update
Adobe today released bulletin with details regarding two new vulnerabilities in Adobe Flash Player [1]. The vulnerabilities can lead to arbitrary code execution and affects all platforms (don't forget Android and Google Chrome patches!).
There is no indication at this point that the vulnerability has been exploited yet. However, I believe this is an unannounced out-of cycle release.
Also note that twitter is littered with links to various "adobe updates" with suspect destinations. Only download adobe updates using Adobe's own update tools or use the Adobe site itself.
Thanks all the readers who alerted us about this issue. It took a little bit long to publish this diary in part as I first needed to verify that the update is valid. The security bulletin below isn't link yet from Adobes bulletin overview page.
http://www.adobe.com/support/security/bulletins/apsb12-05.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
5 Comments
Flashback Malware now with Twitter C&C
The OS X malware family Flashback is making news again. This time around, antivirus vendor Intego uncovered a new version of Flashback that will use Twitter as a command and control channel [1]. The malware will check twitter for daily changing hashtags to look for commands.
Today's hashtag, #pepbyfadxeoa, has already been heavily "abused" on twitter. Given all the additional posts, it isn't really clear if the actual command will be parsed correctly by the bot.
Overall, the twitter channel isn't exactly implemented very strongly. For example, Intego points out that the bot will use specific, but alternating, user agents to hide. However, some of these user agents are pretty easy to spot. Hiding in plain sight only works if you are actually trying to blend in and not lighting yourself with a big flare.
So far, we haven't seen any first hand reports of the infection. If anybody runs across a sample, let us know. I would like to test if Apple's XProtect software adds a signature for it, or if existing signatures cover this one. Apple has been steadily updating the XProtect signatures, but it is not always if it covers version reported by other vendors as the naming is not always in sync. According to my monitoring of XProtect, it was last updated February 7th.
[1] http://blog.intego.com/flashback-mac-malware-uses-twitter-as-command-and-control-center/
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
New automated sandbox for Android malware
One of the things that I've been working on lately is building an automated malware analysis environment to handle Android malware similar to the one I built for Windows malware. I'm not quite there yet, but I was quite pleased to here about the new service being offered by the folks at Die Universität Erlangen-Nürnberg. This is still a research project, so if you choose to use it, be understanding. Don't expect 24x7 uptime and let's try not to DoS them. That said, I'm looking forward to seeing how well it works and how the dynamic analysis will work once it is actually in production.
The Sandbox: http://www.mobile-sandbox.com/
---------------
Jim Clausing, GIAC GSE #26
jclausing --at-- isc [dot] sans (dot) edu
0 Comments
Phishing with obfuscated javascript, shellcode and malware
Be careful with the links showed in this diary because they are live and could infect your computer if not handled properly
Phishing e-mail artwork is becoming more effective everyday. Users are having a bad time trying to distinguish the fake sites from the real ones. I am going to show you a different phising e-mail that does not take the user to a website to try to steal a password but installs malware to the computer using obfuscated javascripts and shellcodes.
I received today the following message:
This looked strange. I reviewed the link and pointed me to http://thedizzybaker.com/wp-includes/int-market.html. The following javascript appeared:
This javascript is obfuscated. I used firebug to get more information and got an iframe pointing to other website:
Following the new link, we find another obfuscated javascript. Let's see a snip of it:
Now here is where the malicious stuff begins. After deobfuscating the script, we find the following:
- The script tries to determine which navigator is running the system:
- The script tries to determine the Adobe Flash and Adobe Reader version installed:
- A shellcode is executed:
Let's take a look to the shellcode. It executes the following instructions:
- kernel32.VirtualProtect: This function is called in the shellcode to establish a 255-byte memory segment where the memory protection attributes can be modified. For more information about the available attributes, see http://msdn.microsoft.com/en-us/library/windows/desktop/aa366786%28v=vs.85%29.aspx.
- kernel32. LoadLibraryA: This function is called to load the urlmon.dll library, which is used to transfer information using the http protocol. A couple of functions inside the file are:
- urlmon.URLDownloadToFileA: The function is called to download http://migdaliasbistro.net/w.php?f=f7d19&e=1 and save it to wpbt0.dll.
- kernel32.WinExec: This function is called to register the dll using regsvr32 -s and then executed.
- kernel32.TerminateThread: This function is called to end the execution of the shellcode.
The file download in step 3 is a dll with MD5 c3124a2981d8e1b9e13e8c21c96448f7. Virustotal shows a 7/43 detection ratio. It injects into explorer.exe and performs inline hooking to ntdll.dll. Once it is installed, it reports to hbirjhcnsuiwgtrq.ru, which resolvs to the following ip addresses: 94.20.30.91, 98.103.133.13, 173.203.211.157, 211.44.250.173, 46.137.85.218, 83.170.91.152, 87.120.41.155 using a http POST to the /rwx/B2_9w3/in/ location.
Such threats are increasing and control of these involves the establishment of malware control measures as part of te Information Security Architecture of the company, like the following:
- Antimalware perimeter defense: I recommend using the Trend Micro and Mcafee web gateways. They are scalabe and integrates very good with the antimalware monitoring system inside the corporation. This measure allows to protect users from downloading malicious code like javascript and executables.
- Host IPS: The antimalware control is not enough in these days as the threats are evolving and the antivirus companies are not capable anymore to control in real time all the emerging malware attacks. This tool is used to prevent the materialization of the vulnerabilities on computers, such as buffer overflow, code injection, among others. Thus, the computer is protected until the virus signature is out so the antimalware program is able to deal with the respective threat.
- Antimalware: This is the conventional antimalware control that is sold by the antivirus companies.
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail: msantand at isc dot sans dot org
8 Comments
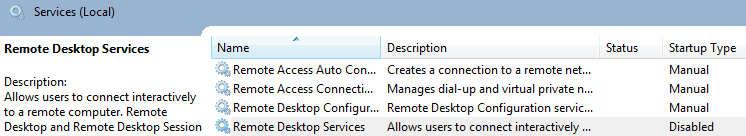
Monitoring Remote Desktop Services logs ... or not?
Remote Desktop Services (or RDP, as most people call this service) is undoubtedly one of the most useful services that Windows administrators depend on. Introduced all the way back with Windows NT, Microsoft has been continually adding new features to Remote Desktop Protocol, with the current version 7.1.
One of the cool features Microsoft added initially with Windows Vista was Network Level Authentication (NLA). This new feature that must be supported by both the RDP client and server allows a client to go through the authentication process before connecting to the remote server. This has several benefits, the biggest one being that it requires fewer resources until the authentication process has successfully completed.
As I’ve been spending a lot of time analyzing Windows logs, I found that the introduction of NLA changed behavior of RDP servers regarding logs, due to the way it works. While the overall security level remains the same, consider this more a kind of a reminder on what to look for if you ever have to investigate a security incident concerning RDP connections.
So, before Windows 7 and Windows Server 2008, once we decided to use RDP to connect to a remote machine we fired up mstsc.exe, entered the name or IP address of the destination server and soon (or not so soon, depending on how fast or slow your connection is), the following screen welcomed us:
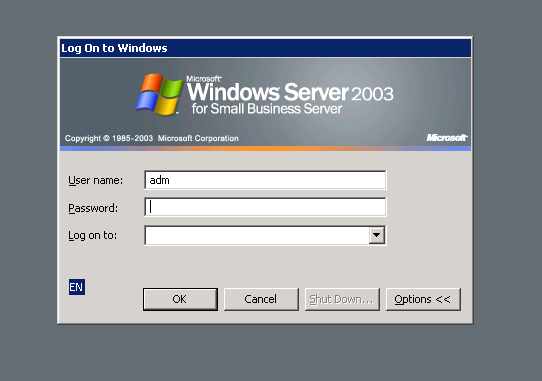
In this case the user can enter his/her credentials for the server to verify. In this case, the verification process is done by the target RDP server – behind the curtains, this server either contacted the domain controller or authenticated the user locally. In this case, an event 672 (for successful Kerberos authentication; event 4768 on Windows Vista/7/2008) or event 680 (4776) (in both successful and failed NTLM authentication) will be logged, following by a 528 or 529 (or 4624 and 4625 on Windows Vista/7/2008) event. In case of this event (528 or 529), its Logon Type value will show 10 which means RemoteInteractive or simply RDP.
All good in this case, since we can see the server that the user tried to connect to (the server requesting the authentication), and on the server we can see the source IP address of the user and his/her successful or unsuccessful connection attempt. If you are now collecting logs to a central log management server you can simply report or alert on brute force attempts on RDP.
However, with NLA things changed a bit. Since the authentication process has been changed, if the user now tries to login to a RDP server with his domain credentials, the mstsc.exe client will try to authenticate with the domain controller directly. If this attempt was unsuccessful it will result in a 675 event (pre-authentication failed), or 4771. This is as expected – if we haven’t supplied a valid username and password, the authentication will fail.
The problem I noticed here is lack of context: this event is same as any other authentication attempt in the domain. In other words, there is absolutely no way for an administrator monitoring logs to know if the user in question is trying to connect to a RDP server or just brute forcing accounts. Of course, this is not a security vulnerability since the domain controller will respect all implemented security controls such as account locking but there is a small lack of context which can help an attacker “hide” his true actions (accessing RDP).
So, to wrap this up – if you are monitoring your Windows logs don’t be surprised if suddenly you don’t see many (or any) 529/4625 events with Logon Type 10.
--
Bojan
INFIGO IS
4 Comments



11 Comments