SQL injection, lilupophilupop-style
Update/Errata: I got all excited when I saw "information_schema", hoping that this is finally something new. Turns out in my ignorance of SQL Server, I didn't realize that Microsoft SQL Server uses information_Schema as well. So this is just "yet another" SQL Injection like we have seen so many over the last few year. (and prior attacks used "information_Schema" already)
I removed the paragraph about MySQL below.
Sorry. Johannes.
(can someone please come up wiht something new and different? ;-) )
It's been a while since we published the diary about the lilupophilupop SQL injection (https://isc.sans.edu/diary.html?storyid=12127) that back in January had infected LOTS of web sites. But guess what, they are b-aaa-ck, and are trying pretty much the same thing.
which decoded looks as usual:
Searching for the injected "lasimp04risoned" URL via Google shows that bad guys don't seem to be as 'successful' with this attack as last time, but this can change. If you have additional information from your web server logs, especially also information on which server or content management system is being targeted this time, please let us know.
Thanks to ISC reader Mike for sharing the excerpt from his web logs!
End of Days for MS-CHAPv2
Moxie Marlinspike and David Hulton gave a talk at Defcon 20 on a presentation on cracking MS-CHAPv2 with 100% success rate. This protocol is still very much in use with PPTP VPNs, and WPA2 Enterprise environments for authentication.
Moxie's recommendations [1]:
1- All users and providers of PPTP VPN solutions should immediately start migrating to a different VPN protocol. PPTP traffic should be considered unencrypted.
2- Enterprises who are depending on the mutual authentication properties of MS-CHAPv2 for connection to their WPA2 Radius servers should immediately start migrating to something else.
Knowing that MS-CHAPv2 can now be cracked, what alternatives are you considering to secure your now insecure communications? The two alternatives suggested by Moxie are "[...] OpenVPN configuration, or IPSEC in certificate rather than PSK mode."
[1] https://www.cloudcracker.com/blog/2012/07/29/cracking-ms-chap-v2/
[2] https://github.com/moxie0/chapcrack
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
17 Comments
BIND 9 Security Updates
BIND has released 4 new versions that takes care of 2 security issues. They can be downloaded here.
- 9.6-esv-r7-p2
- 9.7.6-p2
- 9.8.3-p2
- 9.9.1-p2
New security bulletins
- CVE-2012-3868: High TCP Query Load Can Trigger a Memory Leak in BIND 9
- CVE-2012-3817: Heavy DNSSEC Validation Load Can Cause a "Bad Cache" Assertion Failure in BIND9
[1] http://www.isc.org/downloads/all
[2] http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-3817
[3] http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-3868
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
ISC Feature of the Week: The 404Project - now with IP Mask
Overview
We've covered the 404 Project https://isc.sans.edu/404project/ in a previous feature https://isc.sans.edu/diary/ISC+Feature+of+the+Week+The+404Project/12415 and announced reports in https://isc.sans.edu/diary/ISC+Feature+of+the+Week+404Project+Reports/12685.
Today we feature an IP Mask for those who would like to obfuscate the IP for privacy or legal concerns. The parsing scripts have been tested to handle v1 format (without IP mask) or v2 (with mask) so backwards compatibility is ensured.
Features
A quick summary explanation with example ranges has been added at https://isc.sans.edu/404project/index.html#summary.
The full details are in the code block at https://isc.sans.edu/404project/index.html#instructions
Simply copy/paste the new code, fill in the variables as before with the addition of updating $sIPMask if you want to obfuscate the IP or leave the default to pass the entire value unchanged. Possible masks include but not limited to:
- 0xffffffff = 192.168.1.1 (Default)
- 0xffffff00 = 192.168.1.0 (mask /24)
- 0xffff0000 = 192.168.0.0 (mask /16)
- 0xff000000 = 192.0.0.0 (mask /8)
- 0x00ffffff = 0.168.1.1 (mask first octet)
- 0xff00ffff = 192.0.1.1 (mask second octet)
- etc...
Please send us a note if you encounter any problems or post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center https://isc.sans.edu
0 Comments
Apple Releases Safari 6
Even if you don't plan to upgrade to Mountain Lion, as of today Safari 6 is available as an update for older versions of OS This new version includes numerous security fixes and improvements.
For a (long) list of fixed bugs, the the Apple security announcement [1]. There are also some new security related features:
- extensions can now figure out if you are in private browsing mode, which should make it easier for extensions to avoid leak.
- the "https" in https urls is highlighted more, and the lock with more information about the certificate is placed right next to it.
- The safe password feature got redone, but it doesn't look like Safari will suggest new passwords unless you run Mountain Lion.
[1] http://support.apple.com/kb/HT5400
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
1 Comments
Apple OS X 10.8 (Mountain Lion) released
You probably saw by now that Apple unleashed Mountain Lion earlier today. If you are lucky to make it past the overloaded App store, you may already be installing it. But some of you may not be as daring, and there are some reasons to be cautious like with any major update like this. OS X includes some interesting new security features:
One important feature, Gatekeeper, implements iOS like restrictions to install software. This feature may be turned off by an administrator, but you should consider leaving it on by default. It will prevent users from installing unauthorized software. Just like in iOS, the software has to be signed by a valid Apple developer certificate. Further, you can limit software to be installed from the app store only. In OS X Lion, the command line utility "spctl" can be used to test this feature. Mountain Lion added a GUI configuration tool to the standard OS X settings dialog. Also see our prior diary about this tool [1].
The "Roaring Apps" website maintains a pretty good list of Mountain Lion compatible applications [2]. Most security tools I use appear to be compatible (Sophos Anti Virus, Kaspersky Anti Virus, Little Snitch, 1Password...). But note that RoaringApps.com is crowd sourced. To make sure, you should check the software publisher's website.
OS X 10.8 also includes a password safe feature, and improved privacy controls. For details, see Apple's list of security features [3].
Make sure to first update ALL software on your system. Various vendors released Mountain Lion specific updates as late as today.
Of course, backups are always a good idea, but I assume you got that covered ;-)
[1] http://isc.sans.edu/diary.html?storyid=12631
[2] http://roaringapps.com/
[3] http://www.apple.com/osx/what-is/security.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Microsoft Exchange/Sharepoint and others: Oracle Outside In Vulnerability
Microosft published an unusual knowledge base article today, warning users of certain versions of Microsoft Exchange and Sharepoint server of a remote code execution vulnerability introduced by Oracle's "Outside In" libraries that are included with these products. [1]
Affected Products:
Microsoft Exchange Server 2007
Microsoft Exchange Server 2010
FAST Search Server 2010 for Sharepoint
Oracle provided a patch for this issue in it's July patch release [2]. The issue si covered by Oracles "Fusion Middleware" fix. Outside in library version 8.3.7.77 and earlier is vulnerable. The fixed version is 8.3.7.171 (US Cert also mentions 8.3.5.6369 as fixed).
As a work around, you could disable the transcoding service, but it will no longer allow you to preview attachments. Or you could disable the advanced filter pack on FAST Search Server 2010 for SharePoint.
Oracle's "Outdside In" libraries are able to decode over 500 different file formats [3]. The libraries are used to be able to index content inside files like PDFs and other common file types.
It is very likely, that not only Microsoft's software is including this library. US-CERT provides a list of software that they identified.
[1] http://technet.microsoft.com/en-us/security/advisory/2737111
[2] http://www.oracle.com/technetwork/topics/security/cpujul2012-392727.html
[3] http://www.kb.cert.org/vuls/id/118913
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
4 Comments
Report of spike in DNS Queries gd21.net
A reader reported (thanks @Scott) that he is observing a sudden jump in DNS Traffic all asking for the same thing.
Here is a snip from logs, slightly edited.
Jul 24 13:28:56 ns1 named[3240]: client XX.194.158.62#55148: query: gd21.net IN TXT +E
Jul 24 13:28:56 ns1 named[3240]: client XX.194.158.62#63757: query: gd21.net IN TXT +E
Jul 24 13:28:56 ns1 named[3240]: client XX.194.158.62#50037: query: gd21.net IN TXT +E
Jul 24 13:28:57 ns1 named[3240]: client XX.194.158.62#57822: query: gd21.net IN TXT +E
Jul 24 13:28:57 ns1 named[3240]: client XX.194.158.62#21294: query: gd21.net IN TXT +E
Jul 24 13:28:57 ns1 named[3240]: client XX.194.158.62#6076: query: gd21.net IN TXT +E
Jul 24 13:28:58 ns1 named[3240]: client XX.194.158.62#27221: query: gd21.net IN TXT +E
Jul 24 13:28:58 ns1 named[3240]: client XX.194.158.62#34485: query: gd21.net IN TXT +E
Jul 24 13:28:58 ns1 named[3240]: client XX.194.158.62#56117: query: gd21.net IN TXT +E
** used with permission **
gd21.net seems to link to a Korean Shopping site of some kind. As always, use caution when following links
Is anyone else seeing this? If so could you report it?
Richard Porter
--- ISC Handler on Duty
16 Comments
Most Anti-Privacy Web Browsing Tool Ever?
For a while now, I got requests triggering our IDS, for their enormous cookie payload. The payload doesn't appear to be an attack, but includes tons of information, that appears to identify the user. These are not cookies we are setting, so some other site or tool is setting them. The content looks a bit like this may be used to pre-fill forms.
Please let me know if you have any idea what is sending all the data. I have no idea if this is legit, or just a "denial of service agains the analyst". But so far, it looks like the data is "real".
Over the last 10 days, I have seen 50 such requests for 13 different IPs. These are all "HEAD" requests and they hit various URLs on our site. Some have Google analytics "utm" strings appended to the URL indicating that they may come from Twitter related services. For example:
User Agent: AppleWebKit/525.13 (KHTML, like Gecko) Safari/525.13.
I am quoting a typical entry below, but I replaced and shortened some of the data with 'xxxxx'
charitydine[repeatad]=yes; default_location[offset]=-4; default_location[city]=ASHBURN; ua-device[look]=web; default_location[region_name]=VIRGINIA; default_location[lat]=39.xxxx; default_location[country_name_code]=US; default_location[lng]=-77.xxxx; default_location[country_name]=UNITED+STATES; lsd=AXxxx_Jq; pid.guid=xxxxx-xxxx-xxxx-xxxx-xxxxxxxxxx; ua-device[mobile]=0; ua-device[setDate]=134291xxxx; www.marykay.com=5711xxxxx.xxxxx.xxxx; NSC_gbsfcvaa.dpn=ffffffff09091cc14xxxxxxxxxxxxx; default_location[postal_code_number]=20146; pds%5Fsess=d=xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx default_location[locality_name]=ASHBURN; www.apache.sid=bd28e6405d09ce1f263d9040bbae88db; default_location[ip]=[IP address of request] runkeeper.channel=web.activity.shorturl; datr=ixELUAbi2WAU-IBZ34yrGE5v; BIGipServerWWW.3NEWS.CO.NZ=1113893056.20480.0000; default_location[lang]=US; _shuffler.web_session=xxxxxxx[long URL encoded string]; vglnk.Agent.p=8645d6bf081026933xxxxxxxx; WP_SessionId_wishpot.com=3b0kpjwunqqkvexqgtbrbdt4; CB%5FSID=0f54b689a5314dbbbc1bff1eb8b68cbb-396224260-12-6; general%5Fmaturity=1; BIGipServerPOOL-xxx.xxx.x.xx-COMPLEX=xxxxx.20480.0000; locale=en-US; BIGipServerPOOL-xx.xxx.9.45-80=1392xxxx0.20480.0000; BIGipServerwebpool.microsites.prod=2xxxxx50.20480.0000; BIGipServerPOOL-94.236.9.5-80=3305285824.20480.0000; CakeCookie[user_uid]=xxxxxxxx app.session=xxxxxxx--xxxxxxxxxx; BIGipServerwww-lb.informatica=xxxxx.20480.0000; BIGipServerpool_www.briargatemedia.com_80=xxxxxx.20480.0000; reg_fb_gate=http%3A%2F%2Fapps.facebook.com%2Ftopface%2Fhoroscope%2F%3Fref%3Dastro; _trance-mixes.com_session=xxxxx; .ASPXANONYMOUS=ypvS7qCGzgEkAAAAYTxxxxxxGM1MTU5KOC9Bdg1cTmhf2I-v1VzJ8JuBtA1; jive.server.info=\"serverName=scn.sap.com:serverPort=80:contextPath=:localName=localhost.localdomain:localPort=9001:localAddr=127.0.0.1\"; BIGipServerPOOL-94.236.9.97-80=3422726336.20480.0000; derStandard%2Eat=MGUID=3507f291-5b32-4a36-8941-014aa483b475&Timestamp=2012-07-22T07:09:17; BIGipServerPOOL_198.101.142.28_80=4010062602.20480.0000; framework.security_id=e5003d6c6cef93db59e92c852aa37766; next=http%3A%2F%2Fwww.facebook.com%2Fpages%2FMy-Vault-Card%2F408213029194706%3Fref%3Dstream; next_path=%2Fpages%2FMy-Vault-Card%2F408213029194706%3Fref%3Dstream; gnm.m.u=On7_FOVzE7gcRS1hhjrvkwhl5cknme_4u1CVwx-62PSD_JY7vJm7IA; ASP.NET_SessionId_4=R1342036983; ASP.NET_SessionId=xsanyvzyuql4m245mkprzl45; =true; ax-sess-www.allfacebook.com=xxxOAEAK; connect.sid=LXjcpJkARqE4fNMmCGtL5o6Y.04kX5MkuGDxxxxxbSFgwi6gkWMj0vNnEH38; rack.session=7dca39e61fe4e8483f6740bedc6c68a6eebf3aacdf941bf8afbc0a06efe54140; _swombat.com_session=aba737b1ef62c56e8102e829ecb7d; cnetuk%3Aproduction%3Asid=kn1iu3s75pe6mulnopc2gafnh0; reg_fb_ref=http%3A%2F%2Fwww.facebook.com%2Fphoto.php%3Fpid%3xxxxxx21304754582841; pds%5Flife=d=AQAC%2BDOCwhxxx=5; _session_id=1fa55bffc2162773f73d947ad45f243f; _bit=500be69b-00340-06202-441cf10a; cpsession=ff2f611c-d3f1-11e1-9a88-1231381f8344; SITE=FLPET; SECTION=HOME; ZDEDebuggerPresent=php,phtml,php3; snowball=xxxxxx-cf9e-43f8-b5fc-210449bd06bd; CAKEPHP=xxxxx; __cfduid=dc11c055eed8c7124c5686f5143e7f63f1342957212; spsite_sid=mgv7401bt5hadkhr733apu87g3; zdregion=xxxx; edition=us; session-zdnet-production=k9ia8jlxxxxxxxxbbes3hs3; NID=62=xxxxxx-jFcgLhqWQKx1D1z9_WRjn_xxxxxx-e5SnM0uw4mEwK;
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
8 Comments
OpenDNS is looking for a few good malware people!
Most readers of this space will be familiar with OpenDNS for its DNS based approach to Internet filtering. One of the components of that is a crowd sourced classification of URLs into categories, something that OpenDNS refers to as domain tagging. OpenDNS is looking to take domain tagging one step further. OpenDNS CTO, Dan Hubbard, has put out a request for knowledgeable security people to domain tag the malware category.
If you have a few cycles and you think this might be a fun way to contribute to Internet safety, then please check it out.
-- Rick Wanner - rwanner at isc dot sans dot org - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
2 Comments
TippingPoint DNS Version Request increase
-- Rick Wanner - rwanner at isc dot sans dot org - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
3 Comments
Syria Internet connection cut?
We received a report that there is a loss of connectivity with Syria. The report claims that 90% of the Syrian prefixes disappeared from the BGP tables between 13:32 and 14:13 (UTC) earlier today (2012-07-19). If you have more information please comment or send a note to handler@isc.sans.edu
Thanks to NANOG
UPDATE: Gizmodo has some more information here: http://www.gizmodo.com.au/2012/07/syria-deleted-itself-from-the-internet-today/
UPDATE 2: More good information on the outage: http://www.renesys.com/blog/2012/07/syria-leaves-the-internet.shtml
Mark Baggett
@markbaggett
2 Comments
A Heap of Overflows?
The heap is a section of memory where applications can dynamically allocate and free memory space. Heap Overflows occur when a computer application is able to overwrite the operating system's data structure at the beginning of a block of heap memory and then free that memory. That data structure contains a double link lists with pointers to the previous and next block of memory. When the memory block is freed an "unlink" function is called that uses those two overwritten pointers to find the previous and next blocks of allocated memory and change their pointer so they point to one another and no longer point to the block being freed. To "safely unlink" a block of memory the OS should verify the pointers on previous and next blocks tpoint to the block being freed before it is unlinked. WIthout this check an attacker can use the overwritten pointers to change a value in the memory location of their choosing to the value of their choosing and in most cases gain control of the program's execution.
Ben Hawkes did some analysis of the unlink functions inside the DLLs that are in Windows 8 and found that most of the core libraries in Windows are in fact verifying those pointers and safely unlinking the blocks. That is good news! The bad news is he found many instances of DLLs that are not using those core libraries and not safely unlinking memory.
What does this mean? I don't know. But the research is pretty cool. Mr Hawkes provided a list of DLL's that are not using safe unlinking. They may or may not be exploitable. That is yet to be seen. It is worth a read. http://www.inertiawar.com/win8_unlink/
Join me for SANS 504 Hacker Techniques, Exploits and Incident response in San Antonio Texas November 27th - December 2nd 2012 in San Antonio Texas!
Mark Baggett
On Twitter @markbaggett
1 Comments
Diagnosing Malware with Resource Monitor
Window’s Resource Monitor is a hidden gem within the OS that can be very useful to an incident responder in a crunch. It isn’t as comprehensive as SysInternals Process Monitor but it is built in to Windows so you can use it on a computer with no internet connection. It lacks the depth of WMIC but it does have a very nice GUI (if you are into that sort of thing). In short, resource monitor is a worthy addition to the incident responders toolkit. Resource Monitor isn’t a separate program, but rather it is an operational mode for Performance Monitor (Perfmon.exe). If you start Performance Monitor with the "/res" option you will see the Resource Monitor interface. Click START->Run and type “Perfmon.exe /res” and press Enter. Here is what it looks like.
.png)
It has a series of Tabs across the top (Number 1) for Overview, CPU, Memory, Disk and Network. Each of the tabs is broken down into sections that can be expanded or collapsed by clicking the arrow on each section's header (Number 2). The top section on each tab allows you to check a box next to a process names that will apply a filter to the other sections of the tab. So by checking the box next to “Firefox.exe” you will only see disk, memory and network resources associated with the Firefox process. The disk section shows you files that are open by the process. The networking section will show you the fully qualified DNS name for each of the TCP and UDP connections in use by that process. The memory section gives you a quick look at how much memory is in use by the process. That’s about it for the Overview tab. If that didn't tell you everything you wanted you can refer to the CPU, Memory, Disk and Network tabs for more information. Lets take a look at the CPU tab.
.png)
The CPU tab has some nice features. By selecting a process you can see all of the OS Handles in use by the process (number 4). It even has a search feature that allows you search all of the open handles. The Modules section (number 5) will show you all of the DLLs that are in use by the process.
I’ll leave the remaining tabs for you to explore on your own. I think you will find that in a pinch resource monitor is a good way for a first responder to get a first look at what is happening on a computer.
Performance monitor used Performance counters and Event Tracing for Windows to capture data from various sources. The "/res" option is one of performance monitors way of displaying that information to you. If you are curious what other modes Performance Monitor has give “perfmon.exe /report” a try. If your want to see how a penetration tester might use Event tracing check out this article.
Join me for SANS 504 Hacker Techniques, Exploits and Incident response in San Antonio Texas November 27th - December 2nd 2012 in San Antonio Texas!
Mark Baggett
On Twitter @markbaggett
1 Comments
Snort Updated today
Thanks for the heads-up to our reader Bill, who pointed out that Snort 2.9.3 is just released, details are here ==> http://blog.snort.org/2012/07/snort-2930-has-been-released.html
A couple of new features, and lots of changes to existing ones, the release notes are well worth the read !
===============
Rob VandenBrink
Metafore
0 Comments
Vote NO to Weak Encryption!
This topic is likely more important than the Weak Key story I published earlier. Unfortunately, we all DO get a vote on weak encryption, and almost everyone votes wrong - - enabling the defaults, which include easily attacked crypto algorithms.
I do a fair number of security assessments, and invariably I find servers that support "weak ciphers". What this means is that encryption using weak algorithms is supported, methods such as the ones below (taken from a recent assessment):
SSLv2
EXP-RC2-CBC-MD5 Kx=RSA(512) Au=RSA Enc=RC2(40) Mac=MD5 export
EXP-RC4-MD5 Kx=RSA(512) Au=RSA Enc=RC4(40) Mac=MD5 export
SSLv3
EXP-DES-CBC-SHA Kx=RSA(512) Au=RSA Enc=DES(40) Mac=SHA1 export
EXP-RC2-CBC-MD5 Kx=RSA(512) Au=RSA Enc=RC2(40) Mac=MD5 export
EXP-RC4-MD5 Kx=RSA(512) Au=RSA Enc=RC4(40) Mac=MD5 export
TLSv1
EXP-DES-CBC-SHA Kx=RSA(512) Au=RSA Enc=DES(40) Mac=SHA1 export
EXP-RC2-CBC-MD5 Kx=RSA(512) Au=RSA Enc=RC2(40) Mac=MD5 export
EXP-RC4-MD5 Kx=RSA(512) Au=RSA Enc=RC4(40) Mac=MD5 export
Note that no matter what the hash (MD5 or SHA1), the encryption is all using symmetrical algorithms with a 40 bit key(!), also the Key Exchange (Kx) is 512 bits for each. And yes, you can still implement weak encryption in SSLv3 and TLS - why we all decided that should be in the default set for these newer protocols is beyond me! We're (mostly) past the days where we need to worry about our customers being subject to the old export regulations that limited them to 40 or 56bit encryption (full disclosure - there are still a few exceptions).
The problem is that until very recently, support for these weak encryption methods was part of the default installation - so if you run setup and press enter or "OK" 15 times, this is what you'll have. An attacker only needs to downgrade your encryption, either during the initial negotiation or by triggering a renegotiation, and they can decrypt your data. With the right tools the decryption of these algorithms can be almost real-time.
The sad thing is that, while it's very easy to disable these algorithms, almost every server you'd care to check still supports them. Mostly because folks don't know that they are there, don't know what they are, or don't know what the risks are. Or don't care (though people are starting to come around on caring about it)
I'm hoping that Microsoft's recent emphasis and patches on weak keys will trigger some interest in what's going on inside our corporate webservers.
... Because if the application and the information is important to your organization, it should be considered important enough to protect properly!
===============
Rob VandenBrink
Metafore
2 Comments
Vote NO to Weak Keys!
OK, so I'm a bit off base with the title - we don't get a vote, but that's a good thing!
As part of the August patch cycle (just 3 weeks away), Microsoft will be pushing out a patch that will block all RSA keys under 1024 bits in length. This will affect the whole fleet - Windows XP, Windows Server 2003, Windows Server 2003 R2, Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2. This is being done in the certificate store, so it'll affect all Microsoft encryption services (the most visible being IE).
Their blog entry on this patch is here:
http://blogs.technet.com/b/pki/archive/2012/06/12/rsa-keys-under-1024-bits-are-blocked.aspx
They highlight the more common issues that folks may see:
- Error messages when browsing to web sites that have SSL certificates with keys that are less than 1024 bits
- Problems enrolling for certificates when a certificate request attempts to utilize a key that is less than 1024 bits
- Creating or consuming email (S/MIME) messages that utilize less than 1024 bit keys for signatures or encryption
- Installing Active X controls that were signed with less than 1024 bit signatures
- Installing applications that were signed with less than 1024 bit signatures (unless they were signed prior to January 1, 2010, which will not be blocked by default).
Those last two I hadn't thought of until I read this article - I could see lots of organizations being vulnerable on application and ActiveX signing and not realizing it. (many companies don't realize that they are even using signed applications or controls!)
Not only does the blog describe the patch, and the possible issues, but they go through the steps organizations should make to assess any internal (or external) web applications and services, to ensure that they'll still work post-patch.
The follow-on blog entry covers how to implement work-arounds to permit continued operation. Their approach uses (of course) certutil.exe, the command line certificate utility that is in all affected versions of windows. Find this follow-on blog here:
http://blogs.technet.com/b/pki/archive/2012/07/13/blocking-rsa-keys-less-than-1024-bits-part-2.aspx
Hopefully the impact of this change will be minimal. Remember that the 1024 bit keys in question are in the certificate, so these are the keys used to secure the initial authentication of an SSL conversation. These keys are not the used in the subsequent cipher that encrypts the actual data. Most of the public CAs (Certificate Authorities) all moved to longer keys quite some time ago, so support for weak keys within the certificates is likely a legacy issue, one that will mostly be seen on poorly implemented internal CA infrastructures.
===============
Rob VandenBrink
Metafore
1 Comments
An analysis of the Yahoo! passwords
Last month the biggest security news in the mainstream press was about the password (hash) "breaches" at LinkedIn, eHarmony, and last.fm. Last week, it was a bunch of passwords that were leaked via a Yahoo! service. These passwords were for a particular Yahoo! service, but the e-mail addresses being used were for quite a few domains. There has been some discussion of whether, for example, the passwords for Google accounts were also exposed. The short answer is, if the user committed one of the cardinal sins of passwords and reused the same one for multiple accounts, then, yes, some Google (or other) passwords may also have been exposed. Having said all of that, that isn't primarily what I wanted to look at today. I also don't plan to spend too much time on the password policy (or lack thereof) or the fact that the passwords were apparently stored in the clear, both of which most security folks would probably agree are bad ideas.
The domains
First, I did a quick analysis of the domains. I should note that some of the e-mail addresses were clearly invalid (misspelled domains, etc.). There were a total of 35008 domains represented. The top 20 domains (after converting all to lower case) are shown in the table below.
137559 yahoo.com
106873 gmail.com
55148 hotmail.com
25521 aol.com
8536 comcast.net
6395 msn.com
5193 sbcglobal.net
4313 live.com
3029 verizon.net
2847 bellsouth.net
2260 cox.net
2133 yahoo.co.in
2077 ymail.com
2028 hotmail.co.uk
1943 earthlink.net
1828 yahoo.co.uk
1611 aim.com
1436 charter.net
1372 att.net
1146 mac.com
The passwords
I saw an interesting analysis of the eHarmony passwords by Mike Kelly at the Trustwave SpiderLabs blog and thought I'd do a similar analysis of the Yahoo! passwords (and I didn't even need to crack them myself, since the Yahoo! ones were posted in the clear). I pulled out my trusty install of pipal and went to work. As an aside, pipal is an interesting tool for those of you that haven't tried it. As I was preparing this diary, I noted that Mike says the Trustwave folks used PTJ, so I may have to take a look at that one, too.
The first thing to note is that of the 442,836 passwords, there were 342,508 unique passwords, so over 100,000 of them were duplicates.
Looking at the top 10 passwords and the top 10 base words, we note that some of the worst possible passwords are right there at the top of the list. 123456 and password are always among the first passwords that the bad guys guess because for some reason we haven't trained our users well enough to get them to stop using them. It is interesting to note that the base words in the eHarmony list seemed to be somewhat related to the purpose of the site (e.g., love, sex, luv, ...), I'm not sure what the significance of ninja, sunshine, or princess is in the list below.
Top 10 passwords
123456 = 1667 (0.38%)
password = 780 (0.18%)
welcome = 437 (0.1%)
ninja = 333 (0.08%)
abc123 = 250 (0.06%)
123456789 = 222 (0.05%)
12345678 = 208 (0.05%)
sunshine = 205 (0.05%)
princess = 202 (0.05%)
qwerty = 172 (0.04%)
Top 10 base words
password = 1374 (0.31%)
welcome = 535 (0.12%)
qwerty = 464 (0.1%)
monkey = 430 (0.1%)
jesus = 429 (0.1%)
love = 421 (0.1%)
money = 407 (0.09%)
freedom = 385 (0.09%)
ninja = 380 (0.09%)
sunshine = 367 (0.08%)
Next, I looked at the lengths of the passwords. They ranged from 1 (117 users) to 30 (2 users). Who thought allowing 1 character passwords was a good idea?
Password length (count ordered)
8 = 119135 (26.9%)
6 = 79629 (17.98%)
9 = 65964 (14.9%)
7 = 65611 (14.82%)
10 = 54760 (12.37%)
12 = 21730 (4.91%)
11 = 21220 (4.79%)
5 = 5325 (1.2%)
4 = 2749 (0.62%)
13 = 2658 (0.6%)
We security folks have long preached (and rightly so) the virtues of a "complex" password. By increasing the size of the alphabet and the length of the password, we increase the work the bad guys must do to guess or crack the passwords. We've gotten in the habit of telling users that a "good" password consists of [lower case, upper case, digits, special characters] (choose 3). Unfortunately, if that is all the guidance we give, users being human and, by nature, somewhat lazy will apply those rules in the easiest way.
First capital last symbol = 1259 (0.28%)
First capital last number = 17467 (3.94%)
On the other hand, if we don't enforce at least that much, users won't bother.
Only lowercase alpha = 146516 (33.09%)
Only uppercase alpha = 1778 (0.4%)
Only alpha = 148294 (33.49%)
Only numeric = 26081 (5.89%)
I thought it was also interesting looking at the passwords that contained a year:
Years (Top 10)
2008 = 1145 (0.26%)
2009 = 1052 (0.24%)
2007 = 765 (0.17%)
2000 = 617 (0.14%)
2006 = 572 (0.13%)
2005 = 496 (0.11%)
2004 = 424 (0.1%)
1987 = 413 (0.09%)
2001 = 404 (0.09%)
2002 = 404 (0.09%)
What is the significance of 1987 and why nothing more recent that 2009? When I analyzed some other passwords, I'd see either the current year, or the year the account was created, or the year the user was born. And finally, some statistics inspired by the Trustwave analysis:
Months (abbr.) = 10585 (2.39%)
Days of the week (abbr.) = 6769 (1.53%)
Containing any of the top 100 boys names of 2011 = 18504 (4.18%)
Containing any of the top 100 girls names of 2011 = 10899 (2.46%)
Containing any of the top 100 dog names of 2011 = 17941 (4.05%)
Containing any of the top 25 worst passwords of 2011 = 11124 (2.51%)
Containing any NFL team names = 1066 (0.24%)
Containing any NHL team names = 863 (0.19%)
Containing any MLB team names = 1285 (0.29%)
I wish I had their list of curse words to test. :)
Conclusions?
So, what conclusions can we draw from all of this? Well, the obvious is that without any direction, most users will not choose particularly strong passwords and the bad guys know this. What constitutes a good password? What constitutes a good password policy? Personally, I think the longer, the better and I actually recommend [lower case, upper case, digit, special character] (choose at least one of each). Hopefully none of these users were using the same password here as on their banking sites. What do you, our faithful readers, think?
---------------
Jim Clausing, GIAC GSE #26
jclausing --at-- isc [dot] sans (dot) edu
The opinions expressed here are strictly those of the author and do not represent those of SANS, the Internet Storm Center, the author's spouse, kids, or pets.
13 Comments
Oracle July 2012 Critical Patch Pre-Release Announcement
On Tuesday, July 17, 2012, Oracle is to release 88 new security vulnerability fixes for multiple Oracle products. Some of the vulnerabilities addressed in this Critical Patch Update affect multiple products.The pre-announcement list of affected product is posted here.
http://www.oracle.com/technetwork/topics/security/cpujul2012-392727.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
0 Comments
User Awareness and Education
User education and awareness is a very generic term that is often used in business today to refer to the process of
'educating' users on the company's internal computer policy. This effort often times addresses company policy, best, practices, security, etc. What I don't see in most of these programs that I have reviewed as part of audits is the 'awareness' portion, and most likely because this takes a bit more effort. Security professionals for years have been aware that a vulnerability within one of our systems has the potential to become an exposure on a global scale; most users and many system administrators have yet to recognize this new dynamic. The very statement "we are a mid-size company in America, why would anyone in Asia care about our systems, even if they are vulnerable", is a concern.
So my question to all IT Managers out there today is "what are we trying to accomplish? with this training effort?" In the past my goal was to raise the level of awareness for the users so that they can begin to understand the scale of threats that exist on the Internet today. One website that has a great basic summary of things a user can do to improve the overall security of their computer or computers is the IS site at MIT. This article reflects simple approaches, talking about technical and user practices that will aide tremendously in the overall security effort.
The title of my article today is "User Awareness and Education", as opposed to "User Education and Awareness", because I believe that user awareness is one of the most effective cybersecurity tools in our arsenal. With awareness usually comes the desire for education, to understand the why.
As an old friend used to say "This is where we have to engage the gray matter in our brain".
What say you?
tony d0t carothers --gmail
10 Comments
Yahoo service SQL injection vuln leads to account exposure
We're a bit slow on the uptake given SANSFIRE, but as you are likely well aware, a SQL injection vulnerability was leveraged to gain access to the Yahoo Voice service which was utilized by attackers to acquire then post login credentials for more than 453,000 user accounts that they said they retrieved in plaintext.
2 Comments
VMWare Security Advisory 12 JUL 2012
VMSA-2012-0012 is an advisory specific to a VMware ESXi update that addresses several security issues.
This includes an ESXi update to third party component libxml2. The libxml2 third party library has been updated which addresses multiple security issues.
All the details are available here: http://www.vmware.com/security/advisories/VMSA-2012-0012.html
0 Comments
2 for 1: SANSFIRE & MSRA presentations
It's been a busy week for me having presented OWASP Top 10 Tools and Tactics at SANSFIRE in Washington, DC Tuesday evening 10 July, followed by Evil Through The Lens of Web Logs at the Microsoft Security Response Alliance Summit in Redmond (the other Washington) Thursday morning 12 July.
0 Comments
Yesterday (not as on the ball as Rob) at SANSFire
Last night I presented a series of tips and gotchas whilst setting up a home lab for Malware and Packet collection.
Packet and Malware Collection for the Home Network, Research Starts at Home!
- Richard Porter, ISC Handler
- Wednesday, July 11 * 8:15pm - 9:15pmIf you are just getting started in the Information Security Field, or want to practice your packetFu or MalwareFu? A place to start is on the home network! Often at a SANS Conference you will hear the Instructors, Faculty or even the Handlers reply with "Get Written Permission!" With that, you have permission on a network you own. This talk will go over setup, tools, pit-falls and things to be aware of for the home network. This discussion is a useful addition to both Security 503: Intrusion Detection In-Depth and Forensics 610: Reverse Engineering Malware.
It was well attended, and thanks for all the kind words. There were so many requests for my presentation and tips that when we recover from SANSFire, I will write another diary on more hints and tips but here are a couple:
1 - Roomate/Spouse/KId Alerting: Let them know you will be capturing traffic (Or not  )
)
2 - Power: Check power where your lab is, your home wiring may be in series [1]
[1] http://en.wikipedia.org/wiki/Electrical_wiring
@packetalien - Twitter
And thanks again for all those who attended. Check back for more tips about running a lab at home (along with the Dionaea Virtual machine, when it is more stable.)
From SANSfire 2012, signing off!
3 Comments
ISC Feature of the Week: Internet Storm Center Events
Overview
We just added an Internet Storm Center Events page at https://isc.sans.edu/events/sansfire-2012.html! This can be used for announcing upcoming events and posting updates as they happen involving ISC and our handlers.
Features
The Internet Storm Center Events page lists past, current and upcoming events pertaining to ISC and our handlers. There is also a link to Internet Storm Center Events RSS feed you can subscribe in from your favorite feed reader!
The listings include the Event Host (link to their website if available), Date(s), Location, short description and a link to either the event page on the hosts website or an ISC page where we'll list details of the event as they unfold.
The ISC Event details page content will vary depending on the event type and activities. Check out the first one for SANSFIRE 2012!! Be sure and check back for updates, added talks, presentations, links and to keep up with what's happening at the event!
Post suggestions or comments in the section below or send us any questions or comments in the contact form on https://isc.sans.edu/contact.html#contact-form
--
Adam Swanger, Web Developer (GWEB, GWAPT)
Internet Storm Center https://isc.sans.edu
0 Comments
Today at SANSFIRE - Dude Your Car is PWND !
Ok, so I'm a bit late on this - my SANSFIRE presentation was actually on Tuesday (July 10).
In this presentation, we discussed the basics of the on board computer and network within your car. Well-established and legislated SAE and ISO standards define the basics of the OBD (On Board Diagnostic) interface and the network behind it. Unfortunately, these standards don't include such security basics as authentication or authorization - in fact. Even worse, the wireless interfaces in your car (Tire Pressure sensors, in-car Bluetooth etc) don't include these concepts either, and in most cases connect directly back to same network. Any command injected into this computer is blindly followed by the target
Current work into future standards for automotive communications is even bleaker - with peer-to-peer networks for cars (for accident avoidance for instance) and roadside data collection (for emissions monitoring and other uses) on the horizon. The current guidance document for roadside data collection (remote OBD communications) includes such sage advice as "your database should be password protected", but the wireless communications guidance is all about maximizing range and minimizing the impacts of handing off a session between successive peers as the car moves - - not a word about protecting data in transit (wireless encryption or authentication for instance).
A common thread at SANSFIRE this year is security exposures of embedded devices and security issues on SCADA controlled critical infrastructure networks. The automotive OBD network combines these two alarming issues on one critical infrastructure network that most of us use every day. And no-one seems to be working on addressing this issue.
Combining these threats with wireless interfaces (tire pressure sensors, bluetooth and newer zigbee-like interfaces) and recent research (University of Michigan, UCSD etc) describes a significant threat and a viable potential for attack against the civilian population. We discussed the potential for an cellphone-sized magnetic or remote device that could kill or control a car for law enforcement (or malicious actors), or a roadside "accident generator" - a very possible attack would be to engage the front-left brake of a single (or many, or many-many) target vehicle(s). Worse yet, if remote OBD is deployed in high traffic areas (as is currently being discussed) to monitor things such as speed, safe driving or emmissions in real-time, the platform for such an attack might be supplied to the attacker, all they'd need to do would be to hijack this benign platform for evil.
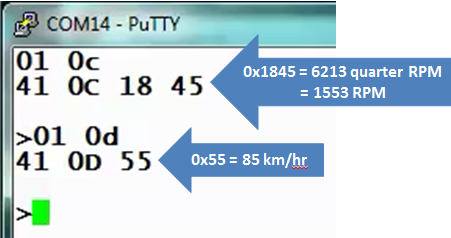
Interfacing to the OBD bus in useful ways was demonstrated, starting with the basics using Putty (or Hyperterminal) to query for OBD parameters.
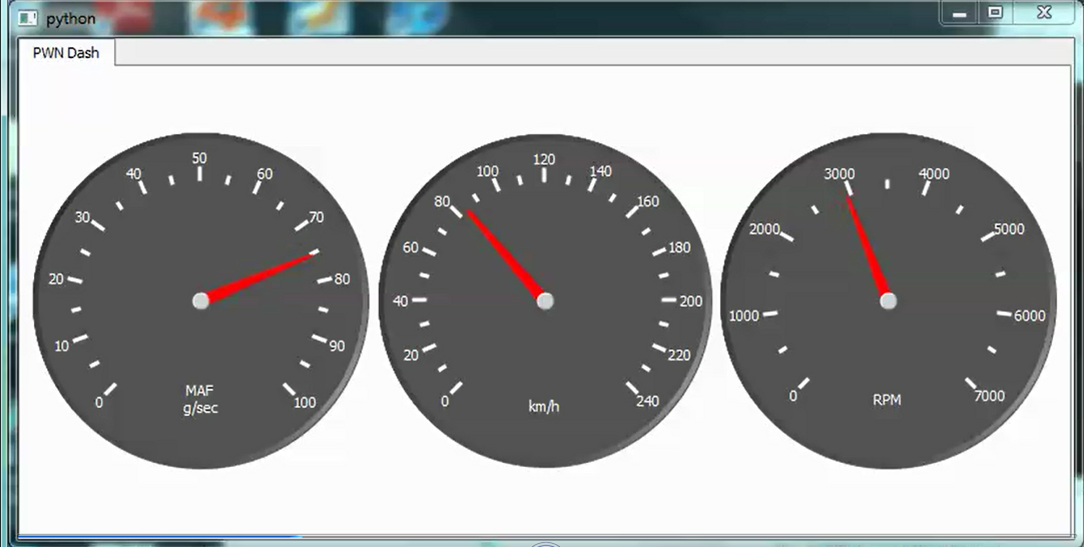
From there we discussed using higher level languages to perform more useful functions - a Python library was used for similar queries, then leveraged to write two "real time dashboards" in Python.
An OBD packet capture utility was also shown, with a nifty time-mark function that is useful in network forensics within the car.
This presentation and example code used will all be posted in our presentations area - watch for them at https://isc.sans.edu/presentations/#sansfire
0 Comments
Excellent Security Education Resources
This week is the annual SANSFire Conference in Washington DC. SANSFire is a SANS conference event like no other in that it is hosted and powered by the Internet Storm Center. All week the Internet Storm Center Handlers are providing insight and talks on all manner of security topics. If you, like me, were unable to attend in-person, most Handlers will be posting summaries of their presentations as diaries at the ISC.
- Digital Forensics Blog - http://computer-forensics.sans.org/blog
- Penetration Testing and Ethical Hacking Blog - http://pen-testing.sans.org/blog
- Software Security Blog - http://software-security.sans.org/blog
- IT Audit Blog - http://it-audit.sans.org/blog
- Cloud Security Blog - http://www.sans.org/cloud
- The SANS/GIAC Reading Room - http://www.sans.org/reading_room/
- Securing the Human - http://www.securingthehuman.org/
- STI and Faculty Research - http://www.sans.edu/research/
-- Rick Wanner - rwanner at isc dot sans dot org - http://namedeplume.blogspot.com/ - Twitter:namedeplume (Protected)
2 Comments
Microsoft fix-it to disable gadgets - SA 2719662
Microsoft Security Advisory 2719662 announces the availability of a fix-it to disable windows sidebar and gadgets. The threat seems to be insecure gadgets that allow random code to be executed with the rights of the logged on user.
See:
The fix-it disables the sidebar and gadgets.
--
Swa Frantzen -- Section 66
6 Comments
Microsoft revoking trust in Microsoft certificates - SA 2728973
Microsoft Security Advisory 2728973 announces that Microsoft is revoking trust in a number of Microsoft certificates. A list of 28 Microsoft intermediate certificates are placed on an untrusted list.
See:
The updat eis cumulative in that it also places previously problematic certificates in the untrusted store.
--
Swa Frantzen -- Section 66
1 Comments
Today at SANSFIRE (09 July 2012) - ISC Panel Discussion on the State of the Internet
Johannes Ullrich was our MC for the evening. He covered off where the ISC came from, the major data collection projects we have ongoing (Dshield Firewall logs, the 404 Project and the Web Honeypot). He also covered off many of the major stories that we’ve seen over the last 12 months.
Russ McRee discussed DDOS attacks against Microsoft as well as service abuse against cloud offerings
Rob VandenBrink - The Microsoft Root Certificate compromise/abuse story was pretty big, along with the follow-on windows update to fix windows update. This is something that's been predicted - - it’s been a part of SEC504 and SEC560 for some time now, and really they should have been more prepared for something like this.
Related to that - SSL support on most browsers do not correctly use the CRL (Certificate Revocation List) - only Opera correctly uses the CRL. So while the "correct" fix for the Microsoft issue would have been to revoke the affected certificate, only Opera would have correctly used that fix !
Manuel Humberto Santander Pelaez highlighted SCADA attacks in South America, as well as the challenges SCADA hardware faces in having to support the legacy protocols and co-exist on general purpose networks. We had a deeper discussion on this after the panel discussion, with some different issues and viewpoints from the Oil and Gas sector thrown in. SCADA was a big part of the evening, both in the follow-on Q and A, and the after-panel-panel.
Richard Porter
- Mobile malware is rapidly on the rise
- With mobile platforms being pushed by both users and management, we’re seeing admins “giving up” on real security for BYOD
- Again related to BYOD, the network perimeter is no longer easy to define. We’ve got external devices, not owned by the corporation that now demand internal access
- With new protocols (IPv6 for one), we're seeing all the old attacks becoming new (and successful) again
Jason Lam
- Many of our new web app problems aren't new. Most of our web apps don't do anything against the newer attacks, we've got our hands full keeping up with the old stuff
- We tend to solve problems that have easy fixes, one thing at a time, ignoring problems that need multiple solutions to actually solve
- Focus on pentest is only looking at one face - mechanisms for defense of web apps are simply not being deployed
- For instance, look for hash compromises next year - we're still not hashing correctly
- We’ve seen a rise in hacktivism over the last while - these folks often don't have budget, they just have time on their hands and the will to succeed
Lenny Zeltser discussed the impact of PCI - for all that many view it as "the minimum bar" for security rather than as a demanding standard, it has had a marked, positive impact on the state of internet security, especially on smaller businesses
But PCI compliance still gives a false sense of security, again, especially to smaller businesses. While it raises awareness, many of them view their security as a solved, completed problem with PCI certification done.
Security products need to become more intelligent, more automated and cheaper – what’s custom and expensive now needs to become automated, smarter, commodity products
William Salusky covered off his top 5:
- spear phishing, targetted at and originating from AOL
- compromised accounts - specifically webmail accounts. targetting financial data, contact lists, leverage compromised pwds against other things (like bank and financial sites)
- hacktivism - not politically motivated, each hactivism group want to be "better” than the last hactivism group. Most aren't particularly political, this phenomena seems to be more of a "We're badder than Lulzsec" one-upmanship thing
- More discussion on certificate authorities and the recent compromises
- Lots and lots (and lots) of malicious advertising has been seen this year - ads with malware embedded / drive by compromises
Lots of questions followed on, notably several on malware and especially several SCADA questions
After the panel, the fun continued with a good after-after-panel discussion ranging over some future SDN (Software Defined Networking) compromises and resourcing issues, what we can see coming on AVB (Audio Video Bridging) compromises, lots on web app security and defense, and a truly great software demo that we can’t really disclose (but stay tuned)
===============
Rob VandenBrink
Metafore
0 Comments
Microsoft July 2012 Black Tuesday Update - Overview
Overview of the July 2012 Microsoft patches and their status.
| # | Affected | Contra Indications - KB | Known Exploits | Microsoft rating(**) | ISC rating(*) | |
|---|---|---|---|---|---|---|
| clients | servers | |||||
| MS12‑043 | The well know memory corruption vulnerability in Microsoft XML Core Services (MSXML). Note that the updates for XML core services 5.0 are still missing. Replaces MS08-069 and MS10-051. |
|||||
| XML core services CVE‑2012‑1889 |
KB 2722479 | The patch for the problem first described in SA 2719615. Is used according to Microsoft in limited targeted attacks. | Severity:Critical Exploitability:1 |
PATCH NOW | Important | |
| MS12‑044 | The usual MSIE cumulative patch fixing an additional 2 vulnerabilities that allow random code execution with the rights of the logged on user. Replaces MS12-037. |
|||||
| MSIE CVE‑2012‑1522 CVE‑2012‑1524 |
KB 2719177 | No publicly known exploits | Severity:Critical Exploitability:1 |
Critical | Important | |
| MS12‑045 | An vulnerability in ActiveX Data Objects (ADO), part of Microsoft Data Access Components (MDAC), allows random code execution with the rights of the logged on user. | |||||
| MDAC CVE‑2012‑1891 |
KB 2698365 | No publicly known exploits | Severity:Critical Exploitability:1 |
Critical | Important | |
| MS12‑046 | A vulnerability in how Visual Basic for Applications loads DLLs allows random code execution with the rights of the logged on user. This is one more in a long list of bulletins that are related to Security Advisory 2269637. This can be attacked through webdav or other file sharing methods. Note that -as is usually the case with VBA- there might still be vulnerable VBE6.dll files lingering on patched systems as Microsoft does not patch all vulnerable dll's installed by third parties. |
|||||
| VBA CVE‑2012‑1854 |
KB 2707960 |
Is used according to Microsoft in limited targeted attacks. | Severity:Important Exploitability:1 |
PATCH NOW | Important | |
| MS12‑047 | Multiple vulnerabilities in the windows kernel mode drivers allow escalation of privileges. Replaces MS12-041. |
|||||
| Windows kernel mode drivers CVE‑2012‑1890 CVE‑2012‑1893 |
KB 2718523 | No publicly known exploits; Microsoft claims CVE-2012-1890 was publicly released. | Severity:Important Exploitability:1 |
Important | Important | |
| MS12‑048 | A vulnerability in handling file and directory names allows random code execution. Can be exploited by as little as opening an attachment of an email. Replaces MS10-046. |
|||||
| Windows shell CVE‑2012‑0175 |
KB 2691442 |
No publicly known exploits | Severity:Important Exploitability:1 |
Critical | Critical | |
| MS12‑049 | A TLS protocol vulnerability relating to CBC cyphers that allows the encryption to be broken. Relates to the Windows Secure Channel (SChannel) and the Cryptography API: Next Generation (CNG) components. Replaces MS10-049, MS12-006 and MS10-085. |
|||||
| TLS CVE‑2012‑1870 |
KB 2655992 |
Microsoft claims CVE-2012-1870 is public and that proof of concept code was released. | Severity:Important Exploitability:3 |
Critical | Critical | |
| MS12‑050 | Multiple vulnerabilities in Sharepoint, InfoPath and Groove Server allow escalation of privileges. CVE-2012-1858 was already discussed and fixed in MS12-037 and MS12-039 last month. Replaces |
|||||
| Sharepoint CVE‑2012‑1858 CVE‑2012‑1859 CVE‑2012‑1860 CVE‑2012‑1861 CVE‑2012‑1862 CVE‑2012‑1863 |
KB 2695502 |
CVE-2012-1858 was publicly discussed and fixed by Microsoft in last month's batch. | Severity:Important Exploitability:1 |
N/A | Important | |
| MS12‑051 | Folder permission problems in Office for Mac 2011 allows other users to cause unsuspecting users to execute code unintentionally. Replaces MS12-030. |
|||||
| Office for Mac CVE‑2012‑1894 |
KB 2721015 |
Microsoft claims the vulnerability was publicly discussed. | Severity:Important Exploitability:1 |
Less Urgent | Less Urgent | |
We appreciate updates
US based customers can call Microsoft for free patch related support on 1-866-PCSAFETY
- We use 4 levels:
- PATCH NOW: Typically used where we see immediate danger of exploitation. Typical environments will want to deploy these patches ASAP. Workarounds are typically not accepted by users or are not possible. This rating is often used when typical deployments make it vulnerable and exploits are being used or easy to obtain or make.
- Critical: Anything that needs little to become "interesting" for the dark side. Best approach is to test and deploy ASAP. Workarounds can give more time to test.
- Important: Things where more testing and other measures can help.
- Less Urgent: Typically we expect the impact if left unpatched to be not that big a deal in the short term. Do not forget them however.
- The difference between the client and server rating is based on how you use the affected machine. We take into account the typical client and server deployment in the usage of the machine and the common measures people typically have in place already. Measures we presume are simple best practices for servers such as not using outlook, MSIE, word etc. to do traditional office or leisure work.
- The rating is not a risk analysis as such. It is a rating of importance of the vulnerability and the perceived or even predicted threat for affected systems. The rating does not account for the number of affected systems there are. It is for an affected system in a typical worst-case role.
- Only the organization itself is in a position to do a full risk analysis involving the presence (or lack of) affected systems, the actually implemented measures, the impact on their operation and the value of the assets involved.
- All patches released by a vendor are important enough to have a close look if you use the affected systems. There is little incentive for vendors to publicize patches that do not have some form of risk to them.
(**): The exploitability rating we show is the worst of them all due to the too large number of ratings Microsoft assigns to some of the patches.
--
Swa Frantzen -- Section 66
--
Swa Frantzen -- Section 66
12 Comments
Internet Storm Center panel tonight at SANSFIRE 2012!
If you are at Washington DC enjoying SANSFIRE 2012, don't forget that the Internet Storm Center State of the Internet Panel discussion is tonight at 7:15 PM in the Hilton Washington International Ballroom Center. See you all there!
Manuel Humberto Santander Peláez
SANS Internet Storm Center - Handler
Twitter: @manuelsantander
Web:http://manuel.santander.name
e-mail:msantand at isc dot sans dot org
1 Comments
The FBI will turn off the Internet on Monday (or not)
On Monday, the DNS Changer Working group will discontinue providing DNS service to hosts infected with the DNS changer virus. This new item led to a flood of news reports, which IMHO blow the entire affair out of proportion (the headline to this diary entry pretty much reflects a discussion I had today with a non technical person responding to one of these articles). Reading this article, it is likely that you will be one of the people being asked for advice as "how to protect yourself" from this virus. I find it useful to stick to these talking points:
The DNS Changer malware was spreading last year and changed DNS settings in computers it infected. After arresting the group behind this malware, the FBI, as permitted by a court order, worked with ISPs and the DNS Changer Working Group to continue to operate the DNS server that the infected systems pointed to. The hope was to identify and notify as many infected systems as possible. As expected, over the last few months, these efforts had diminishing results. The court order permitting the DNS server is about to expire and as a result, this stand in DNS server will not continue to operate.
If your system is still configured to use the bad DNS server, you will not be able to resolve host names. Even if you removed the malware, it is still possible that you didn't revert the DNS settings change.
For Windows users, this may actually not matter. According to some reports, Windows may actually revert to the default settings once the DNS server is turned off. If you used the bad DNS server, chances are that various entities tried to notify you. Google for example should have shown you a banner. If you don't see a warning banner when visiting Google, you are not one of the systems identified as infected.
Some ISPs setup their own DNS servers for DNS Changer victims. These DNS servers will remain active for now.
This malware is also old enough where Antivirus, if you run any, should have signatures for it.
In short: Don't worry. There are estimates of 250,000 infected systems based on data from the DNS changer working group. There are about 2,000,000,000 internet users. So about 0.01% of internet users are infected. In other words: Very few. People who have disregarded warning banners, phone calls from ISPs, AV warnings, and other notification attempts. They probably should be disconnected from the Internet.
In a few cases routers may be affected by the change, and the router will use the wrong DNS server. Again: if you are connected to one of these routers, you should have seen warning banners. If you haven't seen warning banners at Google: Don't worry.
Lastly: Tell people to go to dcwg.org (short for DNS Changer Working Group.org). It has a little test to tell you if you are affected or not. It also got a lot of first hand information about this malware.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
8 Comments
Microsoft advanced notification for July 2012 patch Tuesday
Microsoft have released the advanced notification for the upcoming July 2012 patch Tuesday and reboot Wednesday extravaganza. There are 16 vulnerabilities to be addressed in 9 bulletins. 3 of the bulletins are rated as critical, the remaining 6 as important. The notification is here:
http://blogs.technet.com/b/msrc/archive/2012/07/05/advance-notification-service-for-july-2012-security-bulletin-release.aspx
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
I will be teaching SANS Sec542 in Minneapolis July, Sec560 in Montreal September, and Sec542 in Vancouver December.
1 Comments
New OS X trojan backdoor MaControl variant reported
Kaspersky has reported that a new previously undetected variant of the MaControl backddor is being used in the wild. The malware arrived as an email attachment, and if installed connect to a C&C server. More information on the malware, its behaviour, and the attack campaign is available from Kaspersky, who discovered this variant. As more malware authors become motivated to attack OS X it is likely that we will continue to see targeted attacks such as this in the future.
http://www.kaspersky.com/about/news/virus/2012/New_Mac_OS_X_Backdoor_Being_Used_for_an_Advanced_Persistent_Threat_Campaign
http://www.securelist.com/en/blog/208193616/New_MacOS_X_backdoor_variant_used_in_APT_attacks
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
I will be teaching SANS Sec542 in Minneapolis July, Sec560 in Montreal September, and Sec542 in Vancouver December.
2 Comments
ocsp.comodoca.com blocklisted (by comodo itself)
Update: Looks like Comodo fixed its classification of the site in an updated report [2]. The site still shows one suspicious scan, but the overall status is "safe". McAfee classifies the site as "minimal risk" but the history still shows a red high risk for web reputation as of today/yesterday. [3]
---
A couple of readers have noticed that "ocsp.comodoca.com" has been labeled as "suspicious" and distributing malware for the last couple of days. In particular Comodo's own site inspector service has been identifying the URL as suspect [1]
OCSP is a newer web service that allows clients to verify if an SSL certificate has been revoked. The older standard, CRL (Certificate Revocation List) required that browsers download the entire list. With OCSP, it is possible to query the status of an individual certificate. The certificate has to have the URL for the respective CRL or OCSP service embedded.
Many browsers will accept a certificate, even if the OCSP service does not respond. They will only mark it as invalid, if the OCSP service responds with a result marking the certificate as revoked. However, for Extended Validation (EV) certificates, browsers tend to be more specific and require a positive OCSP response.
ocsp.comodoca.com appears to be the valid OCSP URL for Comodo. For example, the certificate used for https://www.comodo.com uses this particular OCSP URL. https://isc.sans.edu uses a Comodo based certificate ("Usertrust") as well, and the OCSP URL used for our certificate, ocsp.usertrust.com appears to be affected.
[1] http://siteinspector.comodo.com/public/reports/4753361
[2] http://siteinspector.comodo.com/public/reports/4779683
[3] http://www.mcafee.com/threat-intelligence/ip/default.aspx?ip=178.255.83.1
Also a good article about this in Dutch can be found here: http://www.security.nl/artikel/42063/1/McAfee_blocks_ocsp.usertrust.com_%28178.255.83.1%29.html
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
0 Comments
Linux & Java leap second bug
ISC reader Joel B wrote in with these two links illustrating a couple of the hiccups that people may be experiencing with the recent leap second (on the 30th of June) that happened. Please take a look at these two articles if you think you may be affected:
https://lkml.org/lkml/2012/6/30/122
access.redhat.com/knowledge/articles/15145
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments
Storms of June 29th 2012 in Mid Atlantic region of the USA
9 Comments
A rough guide to keeping your website up
While I didn't write this article, or even know the person that did, I thought it was interesting given the AWS outage recently:
http://blog.rainforestapp.com/post/26217277790/a-rough-guide-to-keeping-your-website-up-through
This may help some of you that run websites. So give it a read.
-- Joel Esler | http://blog.joelesler.net | http://twitter.com/joelesler
0 Comments



5 Comments