20/20 malware vision
In his diary entry "Malware Delivered Through MHT Files", Xavier show some malicious VBA code with obfuscated strings.
Often, in VBA code, when strings are obfuscated, each character to be obfuscated is replace with another character: a string of 7 characters remains a string of 7 characters when obfuscated.
This can be seen in Xavier's sample:
There this line:
Set F3e = CreateObject(A5i("X^cXW=9cXWS__["))
A call to CreateObject with an obfuscated string of 14 characters, in malicious VBA code? That's most likely string MSXML2.XMLHTTP that's obfuscated.
This line:
F3e.Open A5i("RP_"), N7a, False
A string of 3 characters as the first argument to the Open method? That's most likely string GET.
Another line:
Set N0x = CreateObject(A5i("LOZOM9^_]PLX"))
A call to CreateObject with an obfuscated string of 12 characters, in malicious VBA code? That's most likely string ADODB.STREAM that's obfuscated.
Indeed, method SaveToFile is invoked (a member of object ADODB.STREAM):
N0x.SaveToFile P2e, 2
P2e is the file name:
P2e = A5i("WQN9UL]")
OK, so here we are stuck. We can not make an educated guess for the filename, just by knowing the number of characters (7).
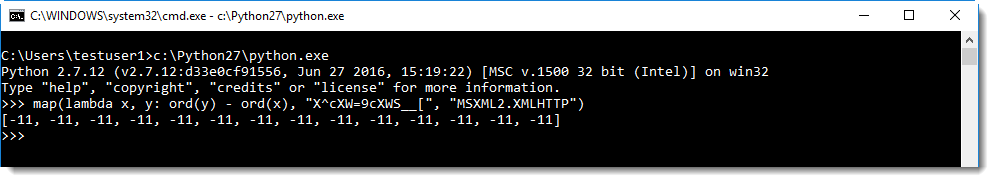
But maybe we can figure out the obfuscation algorithm, by looking at obfuscated strings for which we have guessed the cleartext string. Here I use Python's map function to calculate the difference between the numerical value of the cleartext string and the obfuscated string:
I can see the difference is always -11. So you just need to substract 11 from each character to get the deobfuscated string (using translate.py):
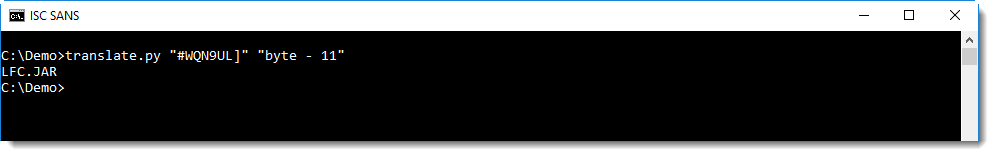
This shows us that the filename of the downloaded file is LFC.JAR.
Just by looking at the length of obfuscated strings passed to CreateObject and/or known methods, you can often guess what the cleartext string is.
And with this information, you can try to figure out the obfuscation algorithm and decode other strings like filenames and URLs.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments