FLOSS 2.0 Has Been Released
When you have to deal with malware in your day job, for research purposes, or just for fun, one of the key points is to have a lab ready to be launched. Your sandbox must be properly protected and isolated to detonate your samples in a safe way but it must also be fulfilled with tools, and scripts. This toolbox is yours and will be based on your preferred tools but starting from zero is hard, that's why there are specific Linux distributions built for this purpose. The one that I use in FOR610 and for my daily investigations is REMnux[1], created and maintained by Lenny Zeltser[2]. This environment offers tons of tools that help to perform all the malware analysis steps from static analysis up to code reversing and debugging.
Even if it does not reveal a lot of information about the malware capabilities (especially today with all the obfuscation techniques in place), static analysis remains an important first step because:
- It's safe (you don't execute the malware)
- It's fast and can be automated to perform the "triage" of your sample
- It main still reveals interesting information that will help you to conduct the next steps.
The static analysis relies on information present in the file like... strings! But even strings can be challenging to find, we can indeed face:
- ASCII strings
- Unicode strings
But they are techniques used by attackers to hide strings. A common technique is called "stack strings".
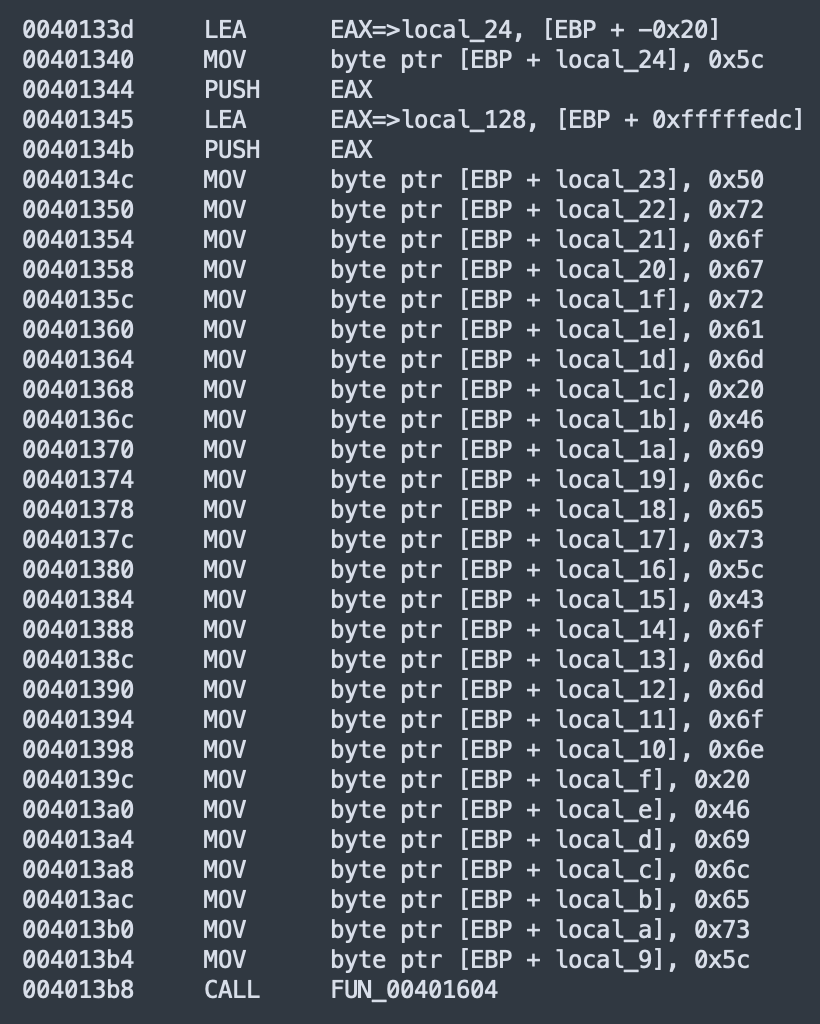
The technique is pretty simple: some space is reserved on the stack then the string is rebuilt by moving all characters one by one. In the example above, the string will be:
0x50 ("P"), 0x72 ("r"), 0x6F ("o"), 0x67 ("g") ...
The results in memory will be:
Program Files\...
FLOSS is a tool that helps to extract strings from an executable (PE) file. FLOSS means "FLARE Obfuscated String Solver". It supports stack strings but also a new version has been released two days ago and it supports a new obfuscation technique: "tight strings". The principle is close to the stack strings but strings are also encoded!
FLOSS supports also simple ASCII & Unicode strings. This make is a perfect tool to extract useful strings from a PE file. Remember: it works only with executable files because it emulates the code to rebuild the strings!
FLOSS is a Python project[3] and is available as a standalone script but can be also "imported" and used in your own projects. It is available on REMnux and I'm sure that Lenny will push an update soon!
[1] https://remnux.org
[2] https://zeltser.com
[3] https://github.com/mandiant/flare-floss
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | British Summer Time | Jul 28th - Aug 1st 2025 |



Comments