Hunting SSL/TLS clients using JA3
JA3 is a method to profile the way server and clients do their SSL/ TLS handshake. It has been created by Salesforce engineers, John B. Althouse, Jeff Atkinson and Josh Atkins. Many servers and clients use different tls configurations, making this a good way of identifying applications, libraries and their corresponding versions. Each tls configuration uses its own set of ciphers, extensions and elliptic curves.
As an example, if you look at this screenshot, it shows the same JA3 signature for multiple different useragents. This means that the same tls configuration is being used within different applications, or the same application with different useragents configured.
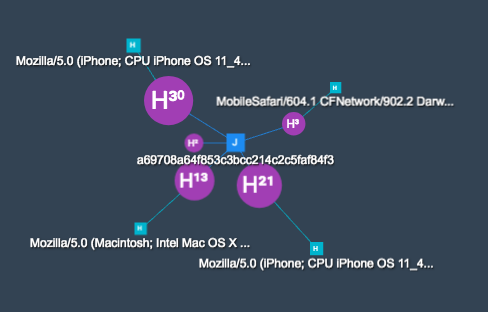
The same signature connects the following useragents:
- MobileSafari/604.1 CFNetwork/902.2 Darwin/17.7.0
- Mozilla/5.0 (Macintosh; Intel Mac OS X 10_13_5) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/11.1.1 Safari/605.1.15
- Mozilla/5.0 (iPhone; CPU iPhone OS 11_4 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/11.0 Mobile/15E148 Safari/604.1
- Mozilla/5.0 (iPhone; CPU iPhone OS 11_4_1 like Mac OS X) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/11.0 Mobile/15E148 Safari/604.1
Taking a look at how JA3 works, it builds a signature out of the following fields which are being sent within the Client Hello message from the TLS/SSL handshake:
SSLVersion,Cipher,SSLExtension,EllipticCurve,EllipticCurvePointFormat
Which corresponds to:
769,47-53-5-10-49161-49162-49171-49172-50-56-19-4,0-10-11,23-24-25,0
Now we can md5 hash this value and the JA3 signature for this specific configuration is:
de350869b8c85de67a350c8d186f11e6
Because the Client Hello message is sent in clear, it allows fingerprinting without access to the encrypted stream. The fingerprinting works for all TLS/SSL enabled protocols. When hunting for threats, the JA3 signature can be used to correlate multiple attacks to the same tool.
Important to know:
- when omitting the Server Name Indication, you'll get a different hash. The hash is built on the extension numbers.
- different versions of applications or operating systems will give a different hash
- a different tls configuration, gives a different hash
Many applications have implemented JA3 support, like Splunk, Suricata, Bro and many more. A complete list can be found on the github page of JA3. The README contains a link to a list of known signatures and their application / library.
References
- https://github.com/salesforce/ja3 (ja3 repository)
- https://github.com/salesforce/ja3/tree/master/lists (list of known signatures)
- https://github.com/danielguerra69/ja3 (bro package)
Remco Verhoef (@remco_verhoef)
ISC Handler - Founder of DutchSec
PGP Key



Comments