Introduction to KAPE
In this diary, I will talk about KAPE by SANS Instructor Eric Zimmerman.
What is KAPE?
Kroll Artifact Parser and Extractor (KAPE) is primarily a triage program that will target a device or storage location, find the most forensically relevant artifacts (based on your needs), and parse them within a few minutes.
Because of its speed, KAPE allows investigators to find and prioritize the more critical systems to their case. Additionally, KAPE can be used to collect the most critical artifacts prior to the start of the imaging process.
While the imaging completes, the data generated by KAPE can be reviewed for leads, building timelines, etc.
Install
KAPE can be downloaded from the following link:
Once you download and unzip KAPE you can find two executables:
One is kape.exe which is the command line version and the other one is gkape.exe which is the GUI version.
Usage
For this diary, I am going to use the GUI version. Like most of forensics acquisition tools, KAPE needs an administrative privilege to do its job.
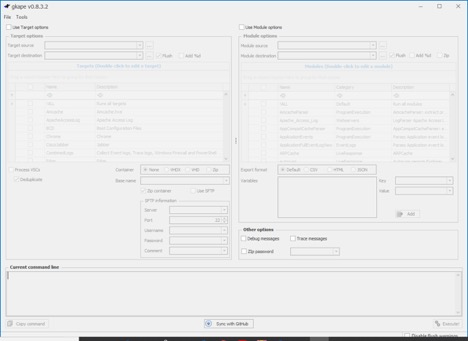
To collect data first click on the “Use Target Options” checkbox then choose what do you want to collect. In this example, I am going to select the C drive as a target source and I am going to choose the following “EvidenceOfExecution, RegistryHives, and FilSystem.
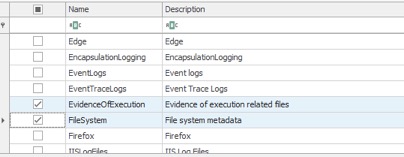
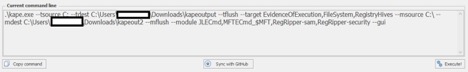
This step will just collect the evidence file. To parse these files, you need to choose it from the modules, For this example, I will choose “JLECmd,MFTECmd_$MFT,RegRipper-sam and RegRipper-security “.
Unfortunately, some of the modules do not come by default with KAPE. One of these modules is reg.exe. but that’s not the end of the world, you can just go kape\modules and open the yaml of the specific module. In this example, I am going to open RegRipper-sam.mkape and check which additional module does it need.
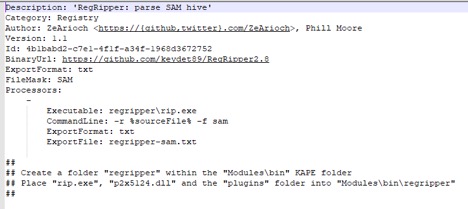
Now just follow the instructions in the file. You need to specify the output directory for both Target and Modules.Now back to the gkape and click “Execute”. Or if you would like to run it from a command line you can just copy the command line version of the same selection from current command line section



Comments
Anonymous
May 1st 2019
6 years ago