Jolokia Scans: Possible Hunt for Vulnerable Apache Geode Servers (CVE-2022-37021)
On Tuesday, the Apache project released an update for Geode. The update patches a typical deserialization issue we often see in Java software like Geode (CVE-2022-37021). Geode is a data management platform. It has to deal with a wide range of objects and formats. The simple allow listing approach usually doesn't work well in these environments.
But the vulnerability has a few dependencies:
- You are only vulnerable if you are using Java 8. Java 8 is considered "on its way out," but it is still widely used. In particular, enterprise applications using Geode will often use Java 8 and are difficult to migrate.
- JMX and RMI are used for the attack. These protocols are common in Java but are usually not directly exposed to the outside. You may remember RMI for its use in log4j exploits. An attacker would likely need to find a gateway to reach the Geode server via HTTP.
And here comes Jolokia. "JMX on Capsaicin," as it calls itself. It provides a simple HTTP to JMX gateway. So it is somewhat interesting that I also saw some scans for Jolkia starting yesterday.
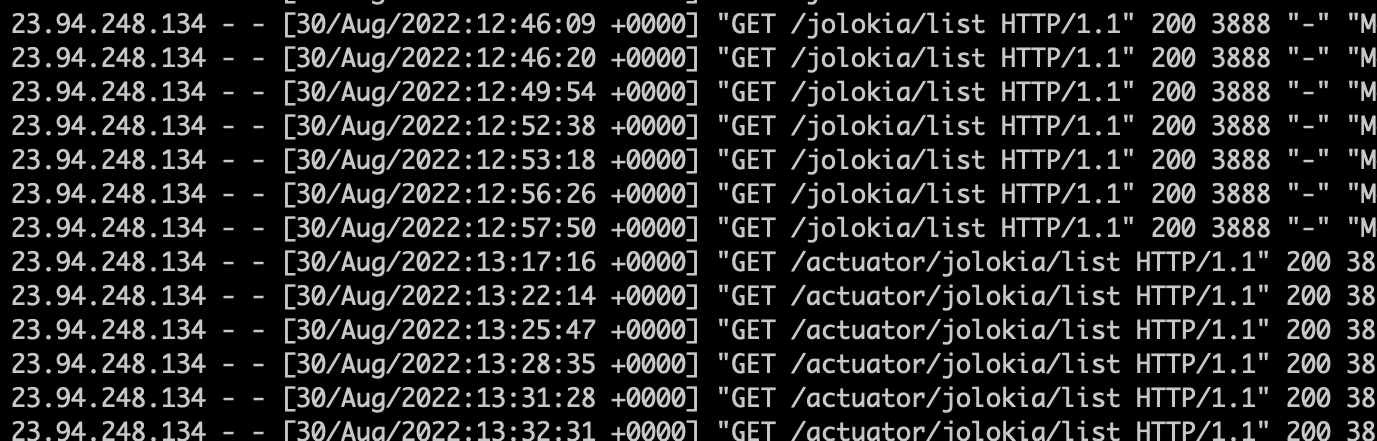
The scans all arrive from 23.94.248.134. I saw the first requests arrive at around 12:30 pm UTC on Aug 30th, a couple of hours before the vulnerability was made public on Geode's website. I am not sure if it was made public via other channels earlier.
The IP address itself is "unremarkable." It is assigned to ColoCrossing. We got some logs from this IP from 2015 and 2016. It looks like a "random colocated server" that gets compromised ever so often. Shodan only shows port 53 open.
The scans target ports 80 and 8080, likely targets for a Jolokia setup. Two URLs are requested:
GET /actuator/jolokia/list HTTP/1.1
GET /jolokia/list HTTP/1.1
All requests use a specific User-Agent:
Mozilla/5.0 (Windows NT 6.1; WOW64; rv:6.0) Gecko/20100101 Firefox/6.0
My recommendation at this point:
- First of all, make sure to patch Geode.
- You may as well block that IP and User-Agent for the time being. It may not do much good in the long run, but it is simple enough.
The link between these scans and Geode is based on the timing of the scans. I do not have any actual exploit payloads right now. Time to figure out if it is worthwhile to set up a full Geode honeypot/VM.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
| Application Security: Securing Web Apps, APIs, and Microservices | Washington | Jul 14th - Jul 19th 2025 |



Comments